
Addressing a wide variety of use cases from one, consolidated console
Security
Classification
Want to see it in action?
Take a virtual tour of the Lepide Data Security Platform in our web-based demo. See how Lepide aligns with your use case, whether it be ransomware, Active Directory security, Microsoft 365 security, data protection, data access governance or more.
Launch in-browser demo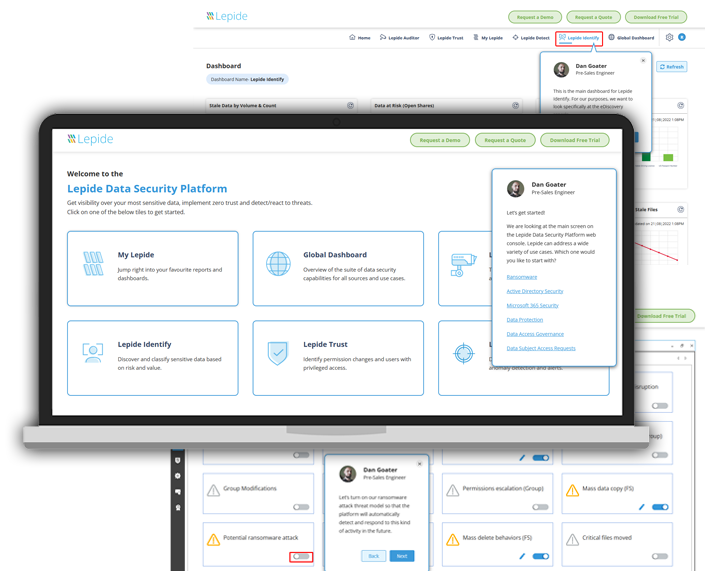
How the Lepide Data Security Platform is structured
Reduce your threat surface by identifying over-exposed data, spotting misconfigurations, and auditing changes with Lepide Auditor. Learn more...
See who has access to sensitive data, spot users with excessive permissions and govern access to data with Lepide Trust. Learn more...
Detect and react to threats with anomaly detection, alerts, threat models, and automated threat response with Lepide Detect. Learn more...
Identify where your most sensitive unstructured data is located, and classify data at the point of creation with Lepide Identify. Learn more...
Complete coverage for your on-premise, cloud, or hybrid environment
Calculate your return on investment if you choose Lepide
Calculate your ROI

Find out how our Platform works
Some data security vendors seem to make security unnecessarily confusing. But not us. We’re transparent about how our Platform works. Take a look for yourself.
What makes our technology different?
The Platform gets smarter the longer it runs, detecting and reacting to threats more accurately.
Execute automated responses when the solution detects ransomware, malware, insider threats and more.
Get alerts on user behavior and changes to data and systems delivered to your email or mobile in real time.
Divert resources to individual pieces of functionality as required to ensure smooth and reliable scalability.
Seamlessly integrate with SIEM solutions to add context to reports and streamline your threat response.
Best in class coverage for both on-premises and cloud platforms with our universal auditing integrations.

We use Lepide for the security of our Azure and On-prem environment, its real time alert system is awesome!

Integrates with Your Favorite Apps and Solutions







