
What is DORA Compliance The Digital Operational Resilience Act (DORA) focuses on enhancing operational resilience… Read More

On August 8th, 2023, the National Institute of Standards and Technology (NIST) released the public… Read More

Understanding the distinction between a data processor and a data controller is crucial for those… Read More
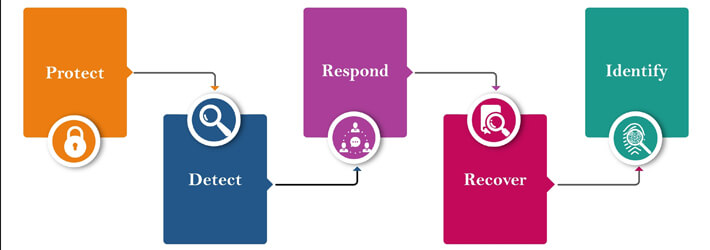
A cybersecurity framework is a set of documents that provide guidelines and best practices to… Read More

What is NIST 800-53? NIST SP 800-53 is a comprehensive set of guidelines that helps… Read More

Whether you are already using Microsoft Azure or considering migrating to it, understanding the compliance… Read More
