
Auto share discovery enables you to spot new shares as they are created and determine whether the share is open – giving all users access to sensitive data.

Lepide analyzes user access and change behaviour to determine what level of access a user needs to a particular folder. We will then suggest full, read-only or no access.

Lepide allows you to modify the permissions of your users without leaving the console. Combine with our permissions analysis to fully implement zero trust
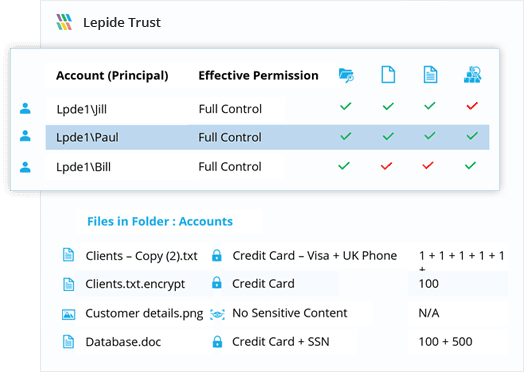
Current Permissions Find out who has access to your sensitive data and how that access is being granted. Determine effective permissions by object, by user or by mailbox.
Permission Changes Spot changes to permissions that create privileged users. Identify where they got these permissions from, and reverse the changes if required.
Users with Admin Privileges Generate a list of your privileged users, and see where they are getting their permissions from.
Take a virtual tour of the Lepide Data Security Platform in our web-based demo. See how Lepide aligns with your use case, whether it be ransomware, Active Directory security, Microsoft 365 security, data protection, data access governance or more.
Launch in-browser demo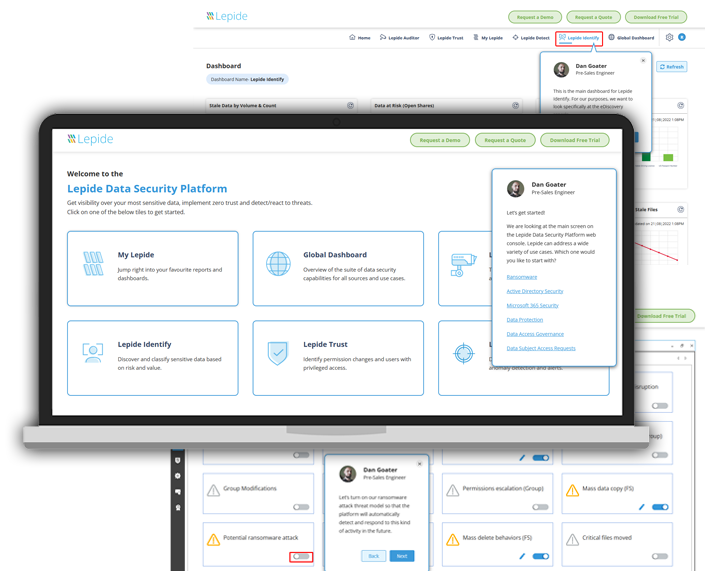

We use Lepide for the security of our Azure and On-prem environment, its real time alert system is awesome!

Lepide is straightforward to use and effective right off the bat. Plus, the level of patience, attentiveness and technical knowhow is far beyond most support and sales teams I’ve seen before.

We chose Lepide as they were able to offer us threat detection and response, and a way of separating out reporting duties to a web console – all from one platform.

Lepide is a perfect fit for our IT Security and Compliance requirements. It helps us cut out a lot of wasted time and money and now we know we can be compliant with industry standards.
