- Support
- |
- sales@lepide.com
- |
- +1-800-814-0578
Ensure that you are able to proactively and continuously audit, monitor and alert on changes to systems, configurations and data. With Lepide Auditor, you can audit any change made on-premise or in the cloud to help you improve visibility, security and compliance-readiness.
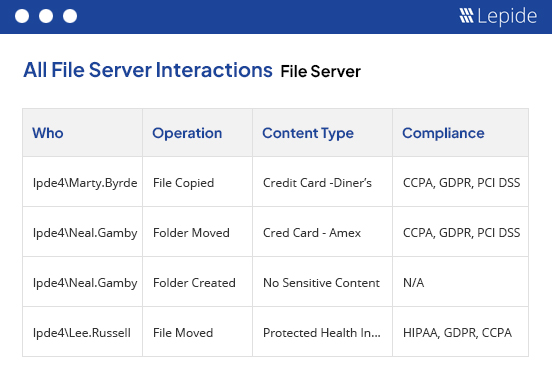
Audit changes and interactions on a wide variety of on-premises and cloud platforms, including Active Directory, File Server, Exchange, Microsoft 365, and more with Lepide Auditor. Audit how your users are interacting with your sensitive data, including moving, copying, renaming, modifying, deleting, and more. Consolidate raw log data into actionable, easy-to-understand reports. Access hundreds of pre-defined audit reports or customize your own reports to get the information you need.
Lepide Auditor identifies states and configurations that are posing risk to your sensitive data. Spot data open to all users through open shares, identify inactive users and stale data, list users with non-compliant passwords, and much more.
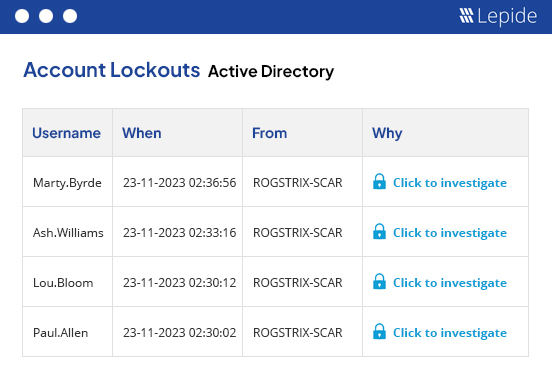
Lepide Auditor will help you speed up and simplify time-consuming tasks that often consume the free time of the IT team. Lepide Auditor can easily restore unwanted changes, such as deleted objects, investigate the source of account lockouts in AD, and remind users to reset their passwords at regular intervals. This frees up your IT team to focus on more important tasks, such as maintaining the security of your sensitive data and identities.
Lepide Auditor comes packaged with hundreds of pre-defined reports designed to help your organization meet the audit requirements of compliance regulations, including GPDR, HIPAA, FISMA, PCI, GLBA, SOX, CCPA, and more. Speed up incident investigations and bolster your incident response with interactive, searchable reporting of events.
Through our universal auditing module, which enables you to connect to any platform using a restAPI or Syslog, you can get visibility over the broadest scope of platforms on the market today. No other vendor offers the range of on-premise and cloud-based platforms that Lepide can offer, including Varonis.