In many organizations you will commonly find multiple users accessing the same mailboxes, which can lead to some users having unauthorized access to sensitive data. It is very important to have suitable monitoring mechanisms in place to make sure that only those with the correct permissions have access to the correct data in shared mailboxes. PowerShell cmdlets enable tracking of shared mailbox access. Using PowerShell cmdlets you can enable mailbox auditing and then view the audit reports in the Exchange Admin Center.
With the launch of Exchange Server 2013, audit reports can be accessed through the Exchange Admin Center (EAC) too. In this article, we will show you show to generate these reports using PowerShell commands and view them using the EAC.
Steps to Audit Shared Mailbox Access using EAC
Please follow below steps
Step 1. Enabling Auditing for Shared Mailbox
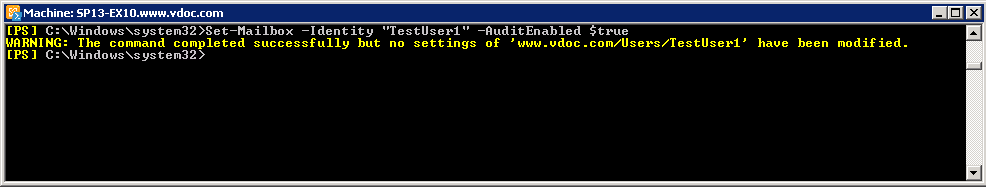
In order to enable shared mailbox auditing, run the following cmdlets in the Exchange Management Shell:
Set-Mailbox –Identity “TestUser1” -AuditEnabled $trueIn the above cmdlet, “TestUser1” is the mailbox id of the shared mailbox
Step 2. Checking the Audit Status of Mailbox
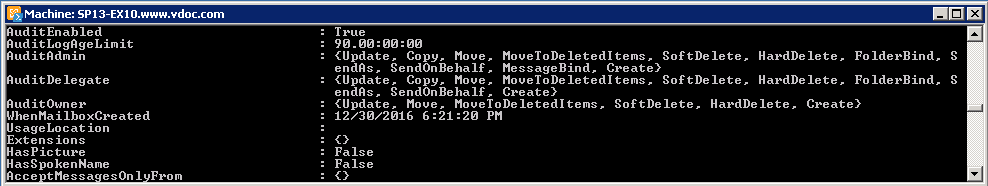
After you have enabled the auditing, you can confirm it by running the below cmdlets:
Get-Mailbox TestUser1 |FLAs you can see in the above image, the “AuditEnabled” parameter is showing “True”.
Step 3. Generate a Non-Owner Mailbox Access Report
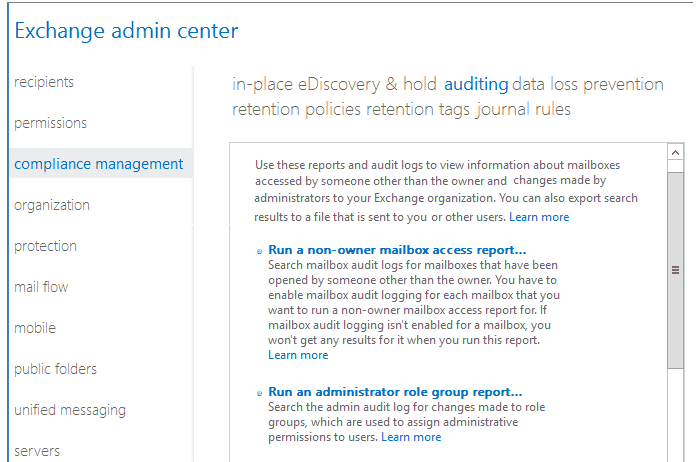
Open the “Exchange admin center”, go to “compliance management”, click on “auditing” tab at the top, and click on “Run a non-owner mailbox access report”.
Step 4. Search for Audit Entries
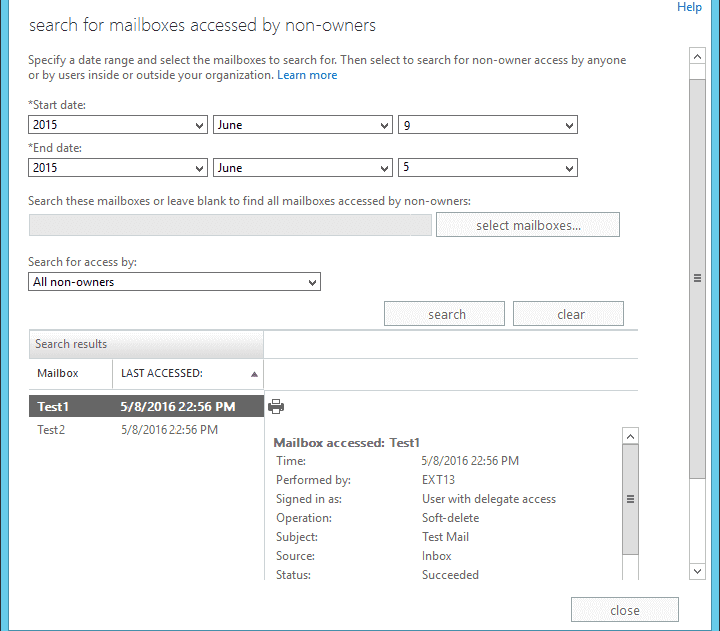
When the search window opens up, enter the start date, and end date. Go to “Search for access by” section, select “All non-owners” from the drop down, and click on “Search”. After the search is over, a list showing audited mailboxes and the last accessed times will be displayed on the bottom-left section. If you click on a mailbox in the list, its audit details will be displayed in the bottom-right corner.
Use Lepide Exchange Server Auditor to Audit Shared Mailbox Access
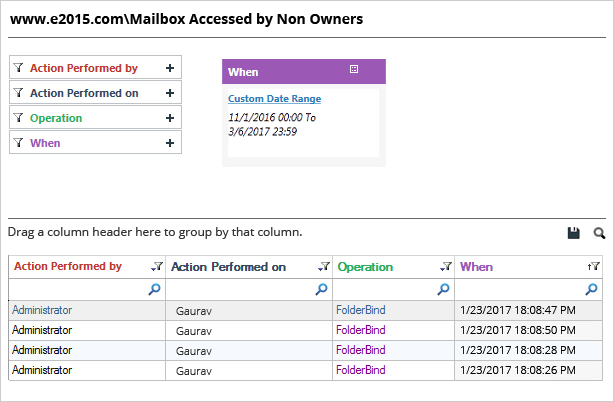
Lepide Exchange Server Auditor is an automated solution that allows users to audit shared mailboxes in real time. Simply add the Exchange Server to the solution, and it will start auditing the chosen server. There are pre-defined audit reports available to for all manner of security, systems management and compliance questions you may want answered. The below report gives details of a shared mailbox accessed by a non-owner. As you can see the answers to the “who, what, when, and where” questions can be found in one record:
Conclusion
Shared mailboxes in Exchange can be accessed by many users who have the required permissions. To ensure that these shared inboxes are secure, it is imperative to regularly audit user activities. This can be done using the native Exchange tools, but the process can be time consuming and reactive. To ensure real-time auditing of Exchange Server shared mailboxes, you may wish to deploy a pro-active solution, like Lepide’s Exchange Server audit solution. This solution automates auditing to help tighten security and enables organizations meet regulatory compliance challenges.