AI-led permissions analysis for Active Directory, file servers, and cloud platforms. Built for IT teams embracing Zero Trust.
A fundamental part of any good zero trust policy is enabling effective access governance over sensitive data. With Lepide Trust, you can get complete visibility over the permissions structure of your business, and receive real-time alerts to spot when changes are creating over-privileged users.
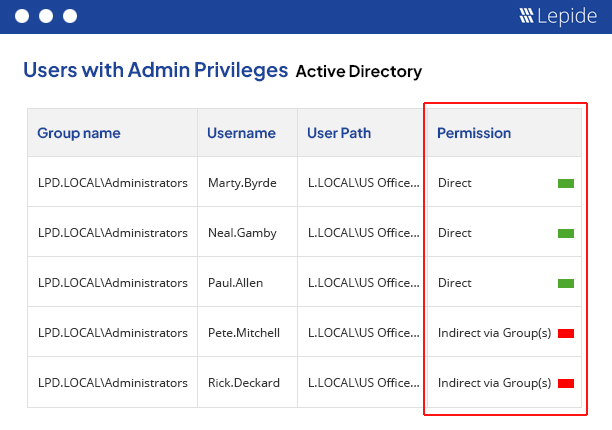
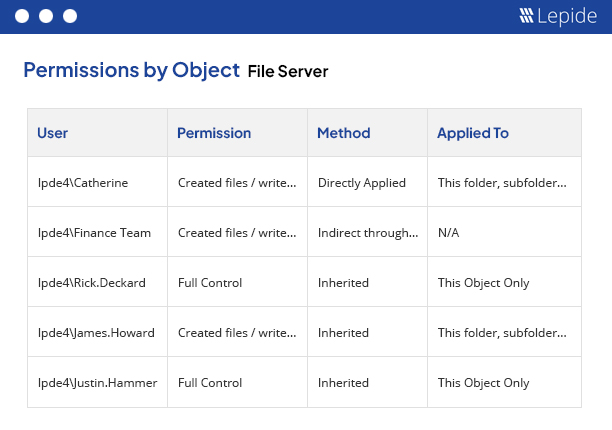
Analyze permissions.
With Lepide Trust, you can see who has access to your sensitive data and how that access is being granted. Determine effective permissions by object, by user, or by mailbox. Spot changes to permissions that create privileged users. Identify where they got these permissions from, and reverse the changes if required. Generate a list of your privileged users, and see where they are getting their permissions from.
Revoke excessive permissions.
Using AI-Led technology, analyze the way that your employees are using their permissions to determine whether the permission is excessive. Lepide Trust reports on users that have access to sensitive files or folders but are not using that access, to give you a clear picture of where to start when revoking permissions to implement zero trust.
Learn more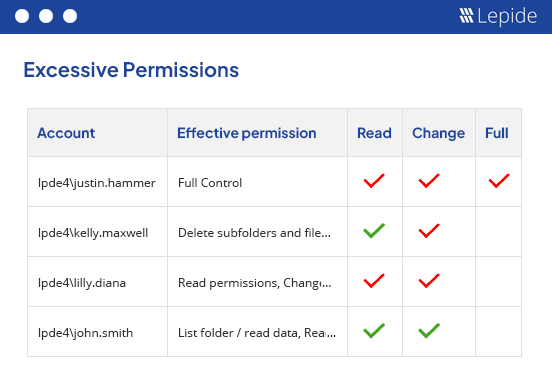
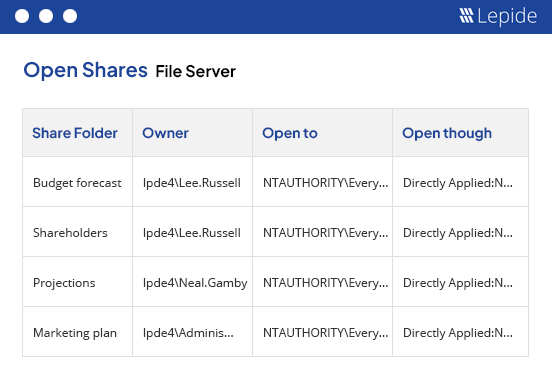
Spot data at risk.
Having sensitive data open to all users through open shares creates unnecessary risk. With Lepide Trust, you can spot and react to this risk quickly. Auto share discovery enables you to spot new shares as they are created and determine whether the share is open – giving all users access to sensitive data.