Lepide Auditor
Active Directory Auditing Tool
Get complete visibility into Active Directory changes, states, and user behavior with our AD auditing tool.
Get before and after values of every change with the answers to the who, what, when and where questions through 100+ audit reports.

Helps you track account lockouts source and provides option to unlock them. Investigate which tasks, services, or processes causing account lockouts.

You can easily audit failed logon events, concurrent logon sessions, users' login history on to multiple computers and much more.

Analyze the effective permissions of your users and spot permission changes. Reverse the unwanted permission changes to an ideal state.

Rollback any unwanted or unplanned change to its original value. Even lets you retrieve objects from tombstone and recycled state.

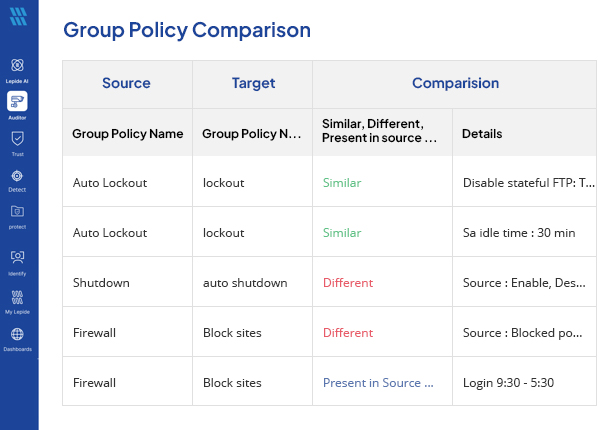
Track modifications made to Group Policy objects and proactively thwart any alterations to the most vital GPOs.
Lepide Auditor for Active Directory provides detailed audit trails with the critical “who, what, where, and when” audit information for all Active Directory changes and events. Lepide provides detailed state-in-time Active Directory security audit reporting so admins can fully understand what their AD looks like. Lepide also tracks anomalies in user behavior using AI-driven technology, including logon/logoff behavior and account lockouts.

Alerts delivered in real time for any events or changes. Automated workflows and threat models for instant visibility and response.

All our reports and dashboards are fully customizable, allowing you to search, sort, and filter to get to the information you need.

Lepide’s Active Directory auditing solution can be deployed on-premises or as SaaS to suit your requirements.
Lepide’s AI anomaly spotting enables you to spot and react to anomalies in what’s happening to your Active Directory.

Get quick, concise answers and summaries of reports by asking our AI helper, Lepide IQ, so that you can interrogate data faster.

Get real time alerts, a live feed of events, and automatic threat response in the palm of your hand.
Get a complete list of your admin users in Active Directory in a clean and easy report.
Download free toolQuickly scan your Active Directory environment to spot disabled, locked, and inactive users.
Download free toolIdentify the source of account lockouts and unlock them.
Download free toolGet a complete list of your admin users in Active Directory in a clean and easy report.
Download free tool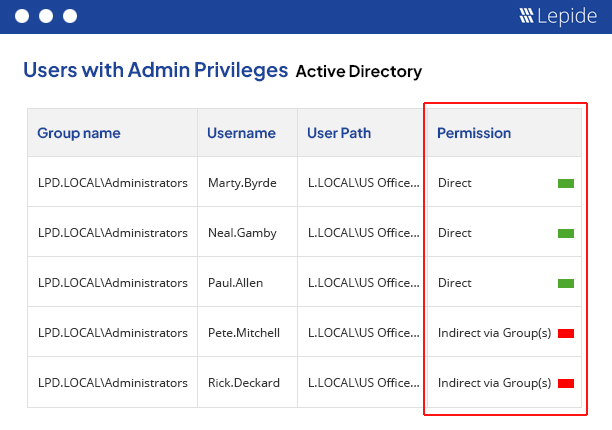
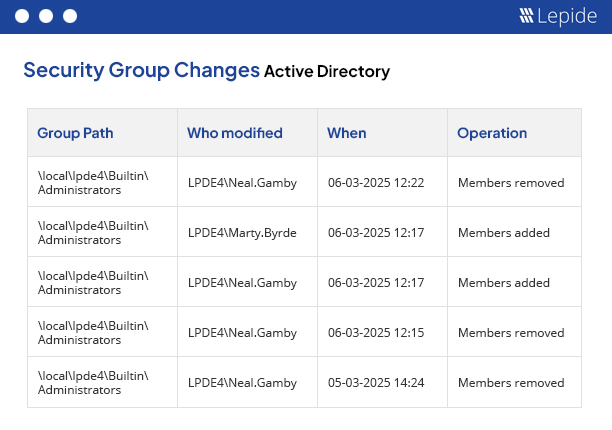
Lepide has over 80 audit reports for Active Directory. Some of our most popular reports include our all environment changes report, Group membership changes, inactive users, users with admin rights, failed logons, account lockouts, and many more.
Auditing Active Directory is an essential element of your data security strategy. It holds the keys to your kingdom, and is often the focal point of attacks. Effective Active Directory auditing enables you to detect unauthorized access, track changes that could compromise security and implement more efficient incident response. AD auditing is also essential for meeting legal compliance requirements, providing detailed audit trails that can be used for internal and external audits. It also helps with operational efficiency, allowing you to audit changes that might affect business operations, monitor user behavior to optimize resource allocation and enforce policies.
There are numerous best practices for effective Active Directory auditing, specifically related to critical activities, including logins, changes to user accounts, group memberships and permissions. AD audit logs should be regularly reviewed to identify and respond to suspicious activities in a timely manner. AD auditing should also be focused on the events that matter the most so that the system is not overwhelmed with noisy data. You should use a third-party AD audit tool that can automate much of the real time alerting and event log analysis. Ensure your event logs are stored securely and retained according to whichever compliance requirements you might be subject to. Detailed internal audits should also be regularly undertaken to ensure policies and practices are still effective.
It’s important to focus on events that are critical to the security of your Active Directory, including the creation, deletion, and modification of user accounts and group memberships. Monitoring logon activities can help to detect unauthorized access. Auditing changes to permissions and access rights can help to prevent privilege abuse or permissions sprawl. Auditing changes to AD schema can help you maintain the integrity of your AD. Additionally, it’s important to audit access to critical systems and sensitive data, as well as changes to group policy objects (GPOs) that could affect your security settings.
Companies should look for AD auditing tools that offer comprehensive and real-time monitoring capabilities, allowing them to track changes to user accounts, group memberships, permissions, and policies. The tool should provide detailed and easily searchable logs, customizable alerting mechanisms for critical events, and robust reporting features to meet compliance requirements. It should also offer integration with other security systems and support for long-term log retention with secure storage. User-friendly dashboards and automated analysis features can help in quickly identifying suspicious activities and potential security threats. Additionally, scalability and support for various environments (on-premises, cloud, or hybrid) are crucial to ensure the tool fits the company's current and future needs.
Yes. If you’re trying to understand what’s happening in your AD, Lepide is the solution for you. We give you a detailed audit trail and who, what, where and when information in a single pane of glass. If something happens, our Active Directory auditing reports will capture it.
Yes. Lepide can give you a detailed look at the state of your Active Directory prior to a migration or digital transformation project. This includes total users, enabled users, disabled users, locked users, and inactive users. We can also show you details of who your privileged users are so that you can make provisioning decisions prior to migration.