Definition: Error Code 53003 is an Azure Active Directory sign-in failure that occurs when a login attempt violates Conditional Access Policy requirements set by your organization’s administrator.
Quick Fix Summary
- Contact your IT administrator to review your Azure Conditional Access Policies
- Update your Microsoft apps and operating system to the latest versions
- Verify you’re signing in from an approved location
- Clear the app cache and restart your device
- Check your internet connection and temporarily disable firewall/antivirus
What is Error Code: 53003
Error code 53003 is a sign-in error when signing into Teams, Outlook, Office, or other Microsoft products and it can occur when your login attempt does not meet the administrator’s criteria. When this error occurs, users typically see the message: “Sign-in was blocked due to Conditional Access policies.”
Azure Conditional Access Policies are security rules configured by your organization’s IT administrators that control how and when users can access Microsoft services—such as requiring specific devices, locations, or multi-factor authentication.
The error is often triggered by permission issues, an outdated OS or application and this error is usually related to Azure Conditional Access Policies.
This guide explains native solutions that can help you resolve this error in a few simple steps, and then looks at how using the Lepide Auditor for Office 365 can help with solving issues with Azure Active Directory.
About Azure Activity sign-in activity reports
Azure Active Directory’s reporting tool generates Sign-in Activity Reports that give you an overview about who has performed the tasks that are listed in the Audit logs.
- All Sign-in activity reports can be found in the Activity section of Azure Active Directory.
- The default list view of Audit logs can be customized by adding additional fields.
- The reports can also be filtered to let you view only the activities that are relevant.
Why am I getting Error Code 53003
- Permission issues: A feature enabled by your administrator in Azure Conditional Access Policies may trigger this error code.
- Out-of-date app: This error message may be generated if the app you use to access the Microsoft service is out-of-date.
- Out-of-date operating system: Out-of-date OS versions can cause some users to experience this error.
- Unsupported sign-in location: Your administrator may have restricted access from certain geographic locations or IP addresses.
- Device compliance requirements: Your device may not meet the security requirements set by your organization.
How to Fix Error Code 53003
The first plan of action is to carry out the following steps before looking at anything more complex:
- Ask your organization’s IT administrator to check your account’s Azure Conditional Access Policies.
- Ensure that you update your Microsoft apps.
- Ensure that the location you are signing in from is supported by your administrator.
- Confirm that your internet connection is strong and reliable
- Disable your firewall or antivirus software temporarily to check whether that could be causing the error.
- Wait a short time to see if the problem resolves itself as the error may be caused by temporary issues with Microsoft’s servers.
After following the steps above if you still have the error, you can try the solutions below:
1. Update your OS
- Press Windows + I to open the Settings app.
- On the left-hand pane, click Windows update, then click Check for updates on the right.
- If there are any updates, click on Download & Install.
- Lastly, restart the computer and confirm it fixes the error.
2. Clear the app cache
- Press Windows + I to open the Settings app.
- On the left-hand pane, click Apps, then click Installed apps on the right.
- Click the ellipses in front of the app that triggers the error, and select Advanced options
- Scroll down and click the Reset button.
- Restart the computer and verify if it fixes the error
When to Contact Your IT Admin
- You’ve tried all the above steps and still receive the error
- You need changes to Conditional Access Policies (requires admin privileges)
- You’re unsure which policies are blocking your access
- You need your device added to the approved devices list
- You require access from a new location or device
If you have tried all the steps mentioned above and are still experiencing error code 53003, it would be advisable to seek further assistance from Microsoft Support. Their team can offer personalized guidance and troubleshooting to help resolve the issue on your system.
How Lepide Helps
A more straightforward approach to resolving issues with error codes is to use the Lepide Office 365 Auditor. Using the Lepide Solution it is a straightforward process to run reports for Azure AD to identify issues that can be quickly and easily resolved.
The example below shows the All Modifications in Azure AD Report which is one of several Azure AD Reports included within the Lepide Auditor:
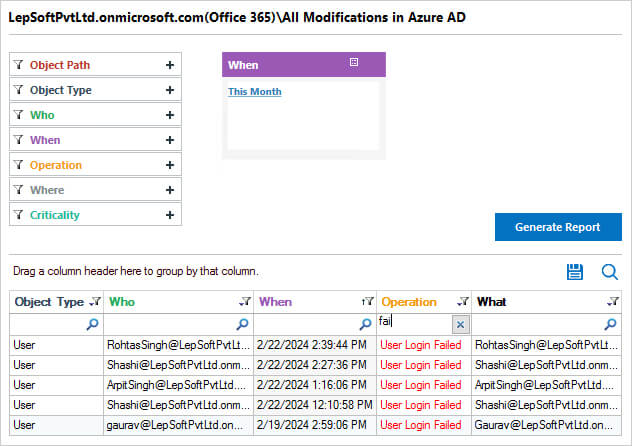
This report includes information about what was changed, who made the change and when it was made.
To run the All Modifications in Azure AD Report:
- From the States & Behavior screen, Office 365, Azure AD Modification Reports, select the All Modifications in Azure AD Report
- Select a date range, click Generate Report
- The report is generated and can be grouped, filtered, saved and exported.
Frequently Asked Questions
Some fixes like updating your OS, clearing app cache, and checking your internet connection can be done without admin access. However, changes to Conditional Access Policies require administrator privileges.
No, this error is not permanent. It can be resolved by meeting the Conditional Access Policy requirements or having your administrator adjust the policies for your account.
The error typically affects the specific app or service that has Conditional Access Policies applied. Other Microsoft apps may work normally if they have different policy requirements.
Your administrator may have recently updated Conditional Access Policies, or your device/location may no longer meet the updated security requirements.
Yes, if your organization restricts sign-ins to specific locations or IP addresses, using a VPN may trigger this error by making it appear you’re signing in from an unapproved location.