Active Directory group membership auditing is the process of tracking and recording changes to user membership within AD security and distribution groups. This is essential for security because group membership determines access privileges to sensitive resources and systems within an organization.
Monitoring Active Directory group membership changes is crucial for maintaining a secure and well-managed IT environment. Group membership determines access privileges and permissions to sensitive resources and systems within an organization.
Here are the key reasons why monitoring these changes is important:
- Security Breach Detection: By monitoring group membership changes, organizations can detect and respond to unauthorized access attempts. Any unauthorized addition or removal of users from critical groups could signify a security breach or insider threat. Prompt detection allows for immediate investigation and mitigation, preventing potential data breaches or unauthorized system access.
- Regulatory Compliance: Many regulatory frameworks, such as the Payment Card Industry Data Security Standard (PCI DSS), the General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), and the Sarbanes-Oxley Act (SOX), require organizations to maintain strict access controls and regularly audit user permissions. Monitoring group membership changes helps ensure compliance with these regulations, reducing the risk of penalties or legal consequences.
- Accountability and Auditing: Monitoring group membership changes establishes accountability for any changes made. It allows administrators to identify who made the modifications, when they occurred, and the reasons behind them. This information is valuable for auditing purposes and assists in troubleshooting and tracking any inappropriate actions.
- Change Management: Active Directory group membership changes often result from employee onboarding, offboarding, or role changes. Monitoring these changes helps organizations maintain proper change management practices, ensuring that users have appropriate access privileges and that the principle of least privilege is enforced consistently.
In this article, we go through how to audit and track Active Directory group membership changes. We will go through the native method first, and then we will show how much simpler the process is when using Lepide Active Directory Change Reporter.
Track Active Directory Group Membership Changes using Event Logs
Prerequisites
Before beginning the native auditing configuration, ensure you have:
- Windows Server Version: Windows Server 2008 R2 or later (Windows Server 2016 or later recommended for enhanced auditing features)
- Administrative Permissions: Domain Admin or equivalent privileges to modify Group Policy Objects and ADSI settings
- Group Policy Configuration: Access to Group Policy Management Console (GPMC) and the ability to create or modify GPOs linked to the domain
Below are the steps for native auditing
Step 1: Enable Active Directory Auditing through Group Policy
- Type GPMC.MSC in “Run” box and press “Enter.” The “Group Policy Management” console opens up.
- Go to “Forest” → “Domains” → “www.domain.com” in the left panel.
- Right-click the “Default Domain Policy” or any customized domain-wide policy. (However, we recommend you to create a new GPO, link it to the domain, and edit it).
- Select “Edit” to access “Group Policy Management Editor.”
- Next, navigate to “Computer Configuration” → “Policies” → “Windows Settings” → “Security Settings” → “Local Policies” → “Audit Policies”.
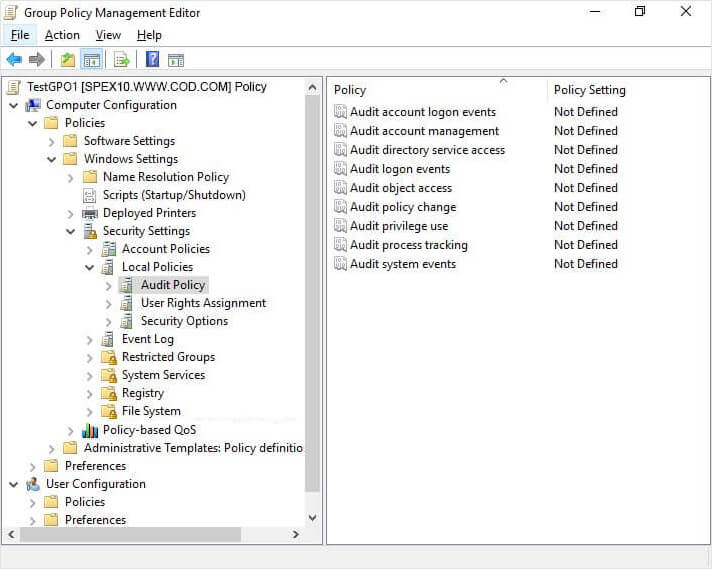
Figure 1: Group Policy Management Editor - Management and access properties.
- Click to select the “Define these policy settings” option.
- Select both the “Success” and “Failure” checkboxes to enable audit policy for monitoring successful events.
- Now, close “Group Policy Management Editor”.
- After closing it, you will be back at “Group Policy Management Console”. Select the GPO that you have modified.
- In the “Security” filtering section in the right pane, click “Add” to apply this GPO to all objects of Active Directory. Type “Everyone” in the dialog box that opens up. Click “Check Names” and “OK” to add the value.
- Close “Group Policy Management Console”.
- It is recommended to update the Group Policy instantly so that new changes can be applied to the entire domain. Run the following command at the Command Prompt or in the “Run” box to update the Group Policies on all domain controllers.
gpupdate /force
Step 2: Enable Auditing of Active Directory through ADSI edit
- In “Start Menu” or in “Control Panel”, “Administrative Tools” and open “ADSI Edit.”
- Right-click the ADSI Edit node in the left panel and select “Connect To”.
- In the “Connection Settings” window, select “Default Naming Context” in the drop-down menu of selecting a well-known Naming Context.

Figure 2: Connection Settings for ADSI Edit - Click “OK” to establish the connection to the Default Naming Context of the domain. It is a node displayed in the left tree pane, just below the top ADSI Edit node.
- Expand “Default Naming Context [dc.www.doamin.com]” and access the top node under it.
- Right-click this top node having the fully qualified domain name and click “Properties” in the context menu.
- In the properties, switch to the “Security” tab and click the “Advanced” button to access “Advanced Security Settings for www”.
- Switch to the “Auditing” tab and click the “Add” button to add a new auditing entry. It shows the “Auditing Entry for www” window on the screen.
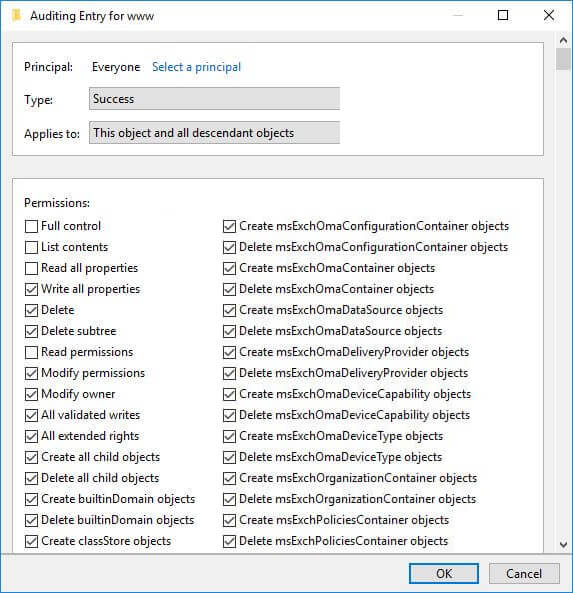
Figure 3: Auditing Entry window - Click “Select a principal” to add“Everyone”.
- Select type as “Success” and applies to as “This object and descendant objects.”
- Under “Permissions,” select all checkboxes by clicking “Full Control,” except the following permissions.
- Full Control
- List contents
- Read all properties
- Read permissions
- Click “OK”.
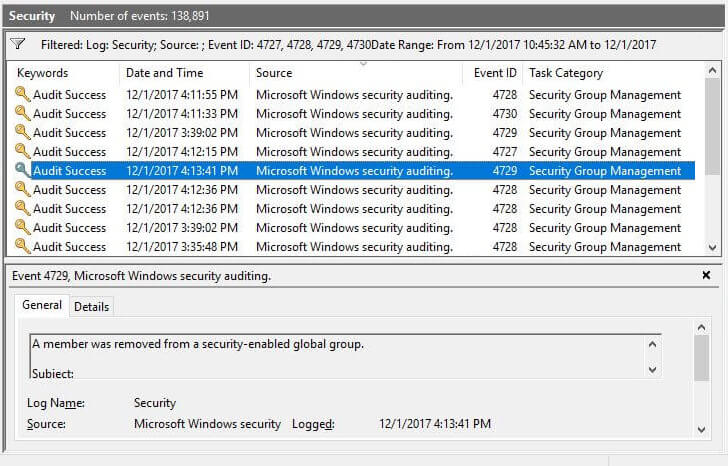
Step 3: Track Group Membership changes through Event Viewer
To track the changes in Active Directory, open “Windows Event Viewer,” go to “Windows logs” → “Security.” Use the “Filter Current Log” in the right pane to find relevant events.
The following are some of the events related to group membership changes.
Below screenshot indicates a Security Group is created.
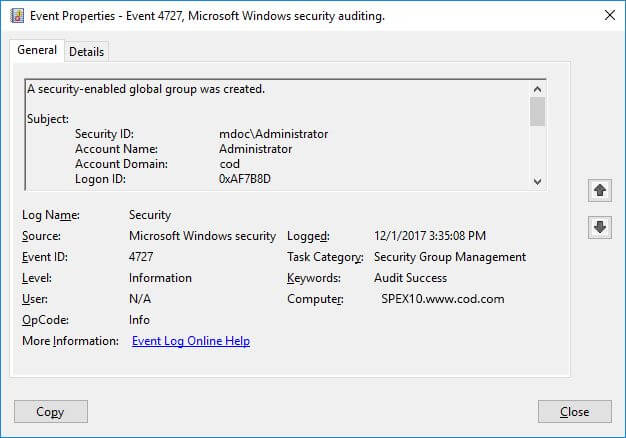
The following screenshot shows more detail of this event.
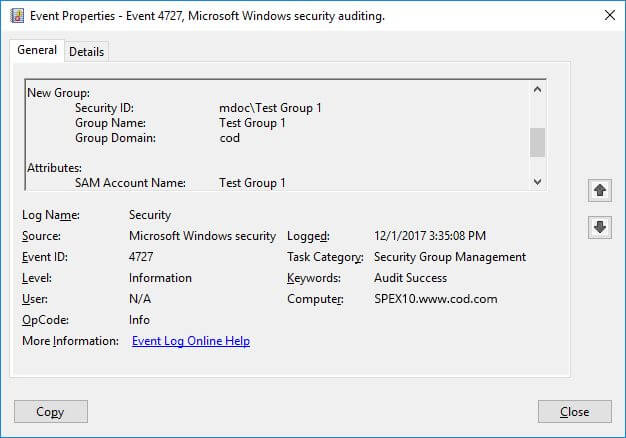
The following screenshot filters all events related to changes in Active Directory Group Memberships.
PowerShell Query Example
To programmatically query group membership change events, use the following PowerShell command:
Get-WinEvent -FilterHashtable @{LogName='Security'; ID=4728,4729,4732,4733,4756,4757} | Select-Object TimeCreated, Id, MessageThe Issues with Auditing AD Group Membership Changes Natively
Native auditing has significant limitations, especially when it comes to Active Directory and Group Policy. Multiple events are generated for a single change—for example, adding one member to a group can produce 2-3 separate log entries that must be correlated manually.
Looking for a critical change in real time is very difficult. The Security log generates thousands of events daily, making it challenging to identify relevant group membership changes without extensive filtering. It is also very difficult to draw conclusions, as events lack context on their own. You cannot see before and after values or understand the business impact of a change. In many cases, relying on native auditing when auditing AD group membership changes will not be enough to ensure the security and operability of Active Directory.
How Lepide Change Reporter for AD (Free Tool) Helps
Lepide Change Reporter for Active Directory (Free Tool) overcomes the limitations of Native Auditing with detailed, contextual, and intelligent Active Directory auditing.
Lepide displays a single event for every change made so that you get all the critical audit information you need in a single pane of glass.
In the following image, you can see a “Group Modifications” report generated in solution. It shows all group membership changes made in a given period. It also shows you the answers to who, what, when, and where questions in a way that is simple to read and understand.
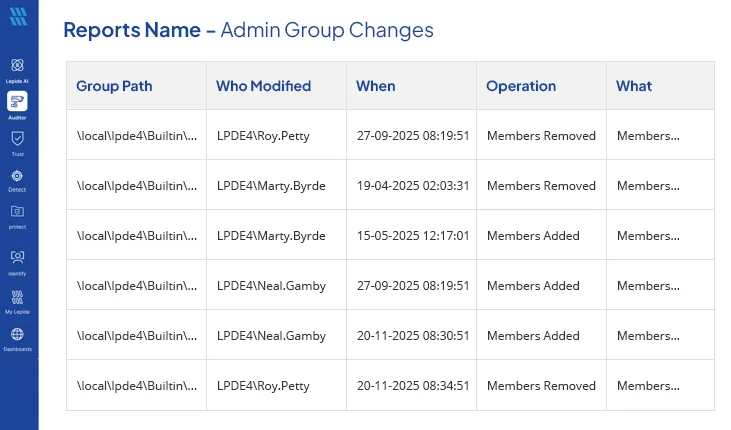
Using Lepide, you’ll be able to get far more visibility into the states and changes of your Active Directory. You’ll be able to determine the effective permissions of your users, see when those permissions change and see what data the users have access to.

