Auditing changes to permissions on file servers is a critical component of any organization’s permissions management and data security strategy, helping to protect sensitive data, maintain compliance, and improve accountability and transparency.
Detecting any unauthorized changes made to file permissions is a fundamental part of managing permissions effectively. By regularly auditing changes to permissions, system administrators can identify suspicious activity and take corrective action to prevent data breaches or other security incidents
Auditing changes to file server permissions can also help to maintain compliance with regulatory requirements, such as those governing data privacy and protection. By demonstrating that changes to permissions are being audited and appropriate access controls are in place, organizations can avoid costly fines and legal penalties.
Accountability and transparency are improved within an organization by auditing changes to permissions. By keeping a log of all changes made to file permissions, system administrators can track who made the changes and when which is essential for troubleshooting and investigating security incidents.
In this article, we will show you how to audit file server permissions firstly by using the native method of event logs and then by using the Lepide Data Security Platform.
Track Permission Changes Using the Event Logs
Follow the steps below to enable auditing and track related events in Event Viewer:
- Navigate to the required file share, right-click on it and select Properties
- Switch to the Security tab, click the Advanced button, go to the Auditing tab , click the Add button
- Select Principal: Everyone; Select Type: All; Select Applies to: This folder, subfolders and files; Select the following Advanced Permissions: Change permissions and Take ownership.
- Run gpmc.msc, edit Default Domain Policy, Computer Configuration, Policies, Windows Settings, Security Settings.
- Go to Local Policies, Audit Policy: Audit object access, select both Success and Failures
- Go to Advanced Audit Policy Configuration, Audit Policies, Object Access:
- Audit File System: select both Success and Failures
- Audit Handle Manipulation: select both Success and Failures
- Go to Event Log and define:
- Maximum security log size to 1 GB
- Retention method for security log to Overwrite events as needed
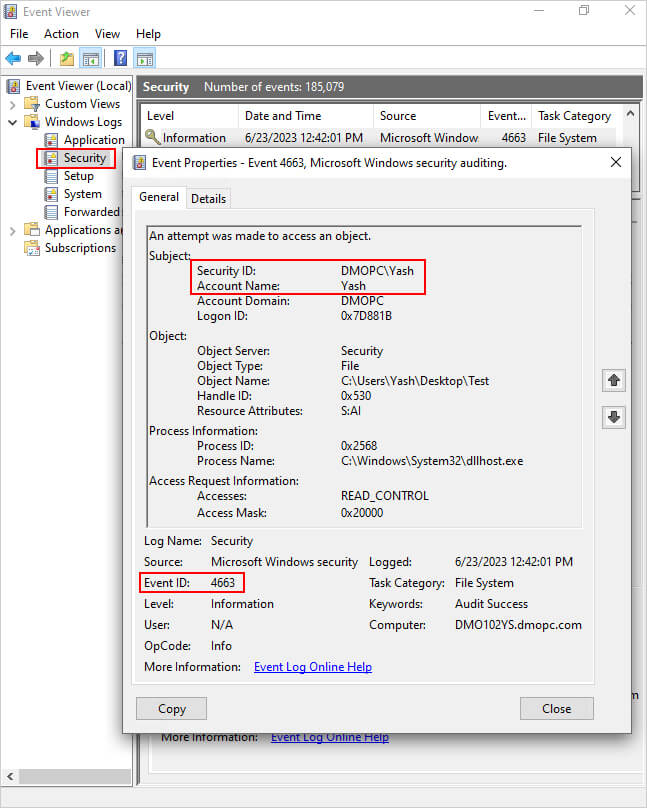
- Open Event Viewer, and search the Security Windows Logs for:
- Event ID 4663
- Task Category: File System or Removable Storage
The Account Name and Security ID will show you who changed the file’s/folder’s owner or permissions.
Audit Permission Changes Using Lepide Auditor for File Server
Lepide Auditor for File Server gives you an easy way to detect, monitor, and report on file and folder permission changes by running the All Permission Modifications Report:
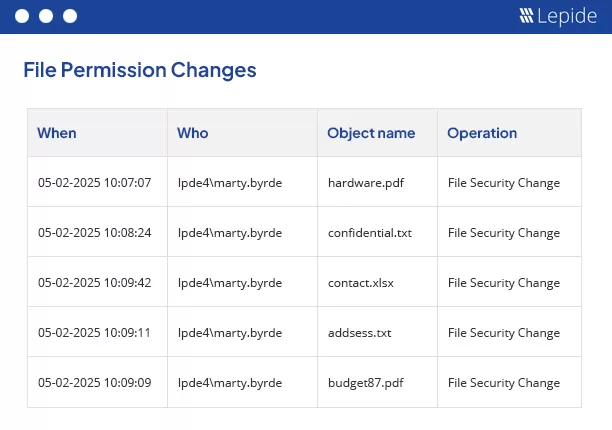
The report shows detailed information on the permission changes including what was changed, who made the change and when it was made.
To run the report:
- From the States & Behavior screen, select the All Permission Modifications Report
- Select a date range, and click Generate Report
- The report is generated and can be grouped, filtered, saved and exported