Audit and Monitor File Access on File Servers
See who is accessing your sensitive files and folders on your Windows File Servers with our file access monitoring software.














File Access monitoring needs to be undertaken to ensure the safety of critical data and to meet the increasing strictness of regulatory compliance. Whatever your driver, our file access monitoring software provides a simple and effective way of keeping a track of what’s happening to your files and folders. Track, alert and report on file access and permissions. Designed to work on both Windows File Servers and NetApp filers, our file access monitoring software will report on both successful and failed access attempts.
The Lepide file access monitoring software enables you to easily audit and monitor all access attempts (failed and successful), track any changes made to files and folders, monitor when files and folders are being created/deleted, and more. All this from one platform.
Any modifications made to the file server, including attempts to access the files/folders or any changes made in their properties will be listen in a single, easy-to-read report. This will enable you to audit file access pro-actively and regularly with minimal effort.
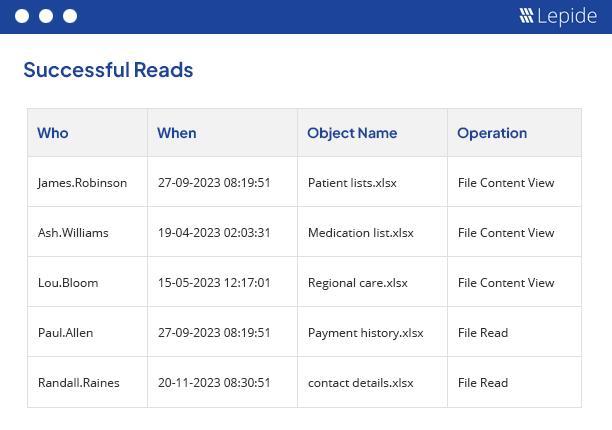
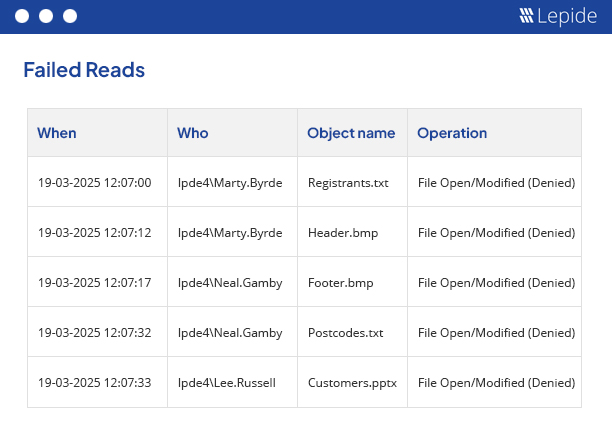
Whenever a user attempts to read a file, an access event is generated. Our solution reports on both successful events (showing who has read the file) and failed events (showing which unauthorized user is attempting to read the file). The solution produces two dedicated reports for these events.
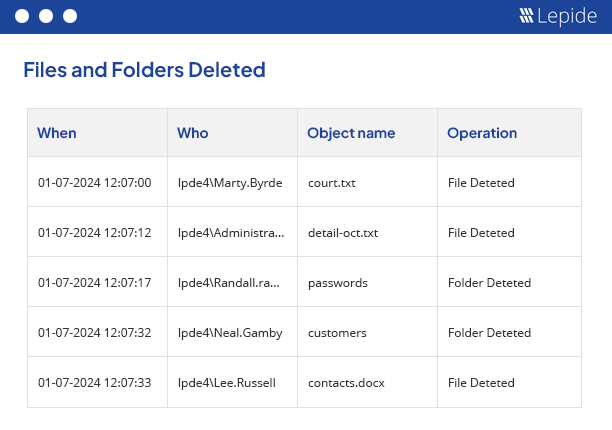
New files and folders are created all the time but you will need to be aware of any user trying to create a file in a restricted area. It is also crucial that you have a method for keeping track of deleted files and folders. Our solution logs every attempt (whether successful or failed) to create or delete both individual and shared files/folders.
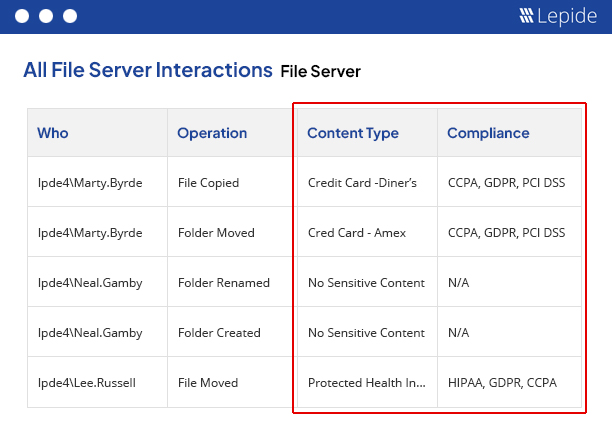
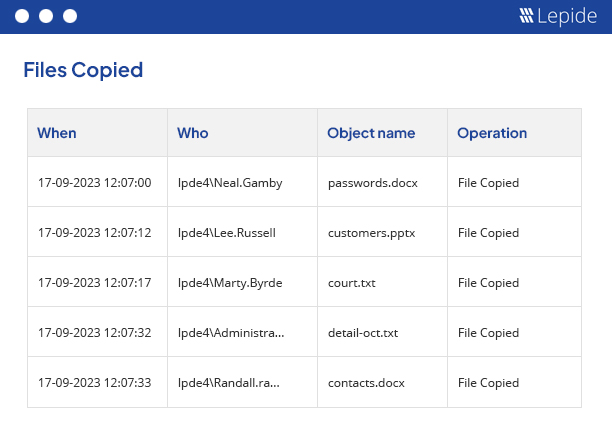
We keep track of whenever a file is renamed or moved. We also keep a record of the files that are being copied in the computer from the network location, changes being made to the file/folder permissions, Audit Settings (SACL) and ownership.
By following the guidelines outlined in this paper, your organization can establish a robust data access governance program that supports its business objectives and protects your valuable data assets.
Get the free guide now!