Restore Deleted Active Directory Objects.
Simplest way to take regular backups of Active Directory states to restore deleted objects.
Fill in the rest of the form to
download the 20-day free trial
download the 20-day free trial
x














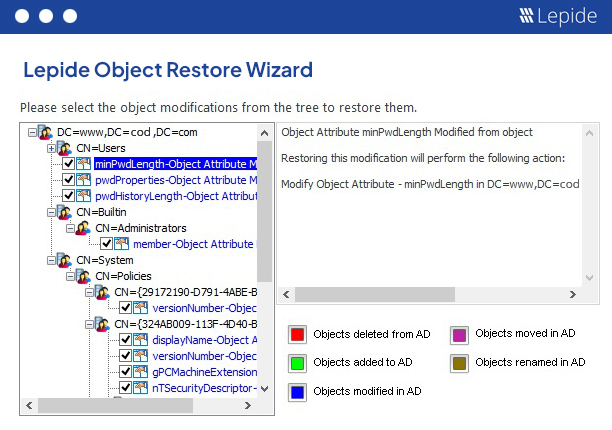
Deleted objects are moved to what is known as “Tombstone State,” and the native process to recover from it is a cumbersome and time-consuming one. The potentially serious implications of some of these changes mean that a better process is necessary. The Lepide Object Restore Wizard provides you with an easier and quicker way of restoring such objects from their tombstone state.

It is next to impossible to recover a permanently deleted object that is neither in “Tombstone” nor “Logically Deleted” state. Lepide Data Security Platform lets you restore such objects from a previously captured snapshot from when that object existed. Once you start Lepide Object Restore Wizard and select a backup snapshot, it compares the current state of Active Directory Objects to the selected snapshot and shows all changes including creation, modification, deletion and renaming of all objects. You can select the changes you want to restore and proceed with the wizard. You can also restore deleted users, along with their passwords, in the same way.
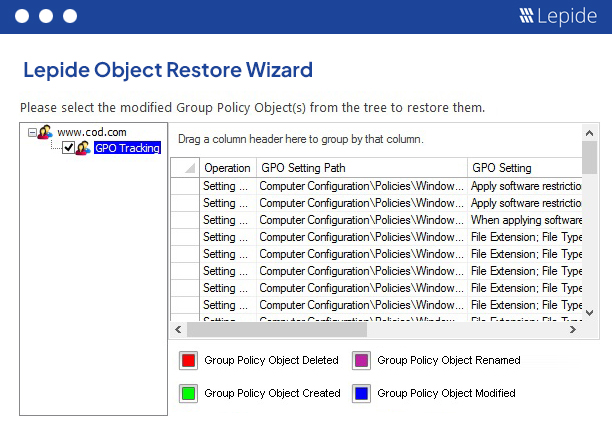
Group Policies are used to configure policies for different purposes, including IT security. Any unauthorized or suspicious change needs to be restored as soon as possible. The Lepide Object Restore Wizard compares the current state of Group Policies with the state stored in the selected snapshot and displays all changes. You can restore the entire Group Policy Object to its original state with a few clicks.
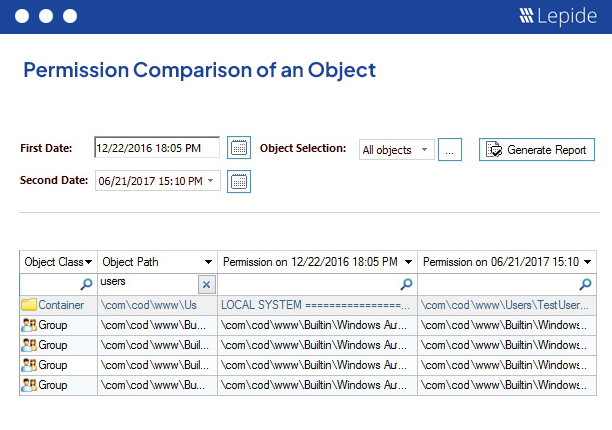
Generating a report to determine what the past state of Active Directory or Group Policy was using native method is impossible. Using backup snapshots, Lepide Data Security Platform generates numerous security reports for Active Directory and State reports for both Active Directory and Group Policy Objects. These reports provide in-depth insights on the state of objects, permissions, audit settings and object ownership as per that moment when the selected snapshot was captured.
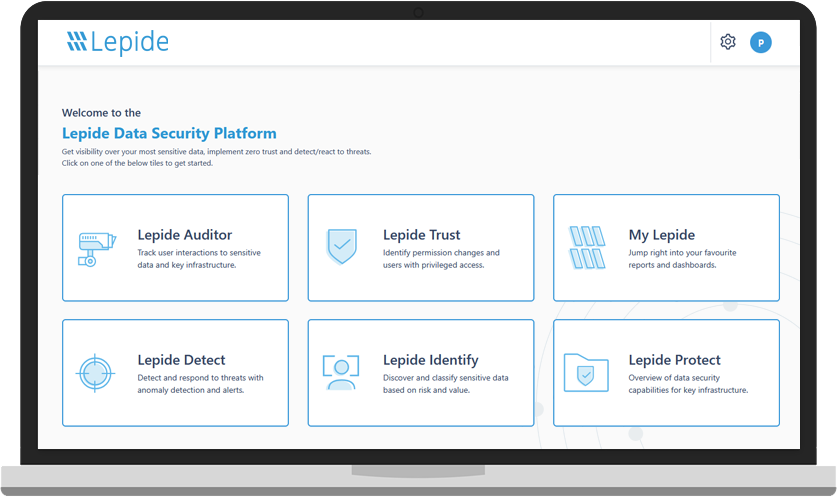
A guided tour of the Lepide Data Security Platform, your ultimate solution for robust and proactive data and identity protection.
View recording