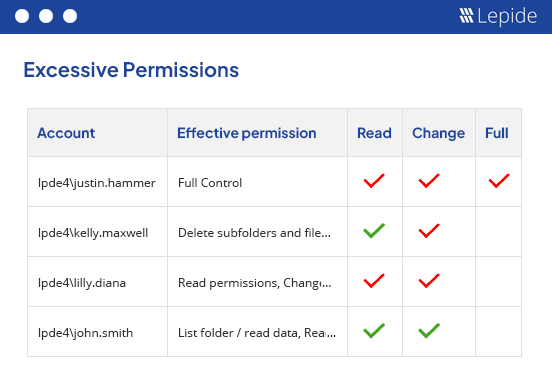
Identify excessive permissions, inactive users, and privileged users before they expose sensitive student or research data.
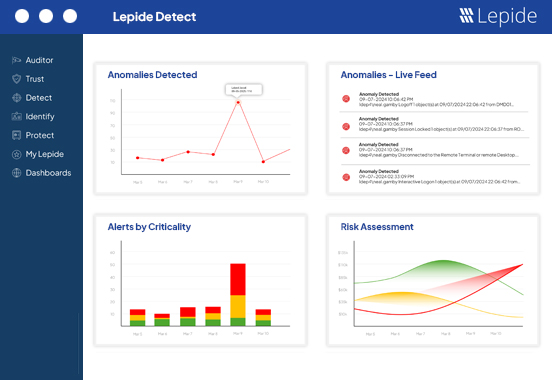
Monitor user activity, detect suspicious behavior, and limit lateral movement to reduce the impact of ransomware.
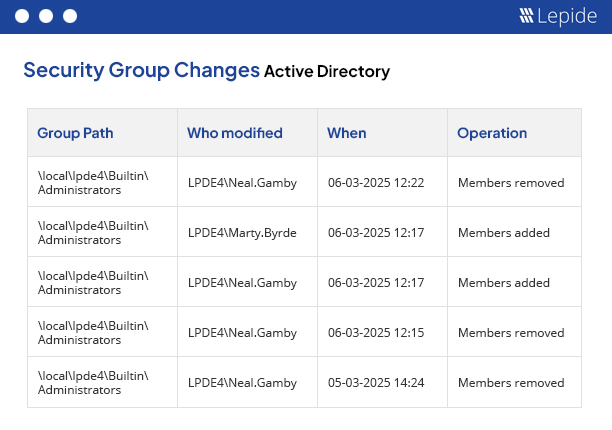
Detect changes to groups, permissions, and privileged accounts so that you can enforce least privilege faster.
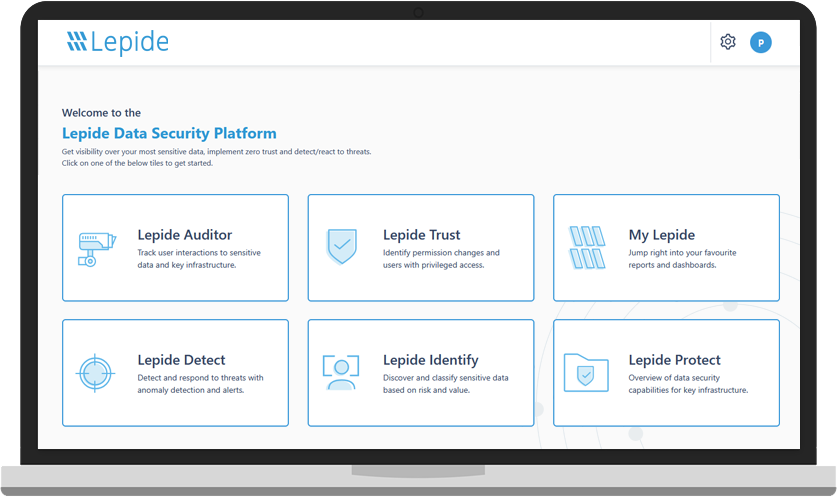
Universities, colleges, and schools often struggle with excessive permissions, dormant accounts, decentralized IT environments, and limited visibility into who can access sensitive data. Lepide helps security and IT teams uncover hidden access risks, monitor user activity, and reduce ransomware exposure across hybrid environments.
Educational institutions are frequent ransomware targets due to sprawling Active Directory environments, excessive permissions, and limited visibility into user activity. Lepide helps you detect suspicious behavior, monitor privileged accounts, and identify risky changes before attackers can move laterally across your environment.
See exactly how users inherit access to sensitive files, folders, and Microsoft 365 data across your environment. Lepide helps you identify over-permissioned users, reduce unnecessary access, and strengthen least privilege policies without disrupting day-to-day operations.
Generate audit-ready reports for FERPA, GDPR, PCI DSS, and other regulatory requirements in minutes. Track permission changes, monitor access to sensitive data, and provide clear evidence during audits and investigations without relying on manual processes.
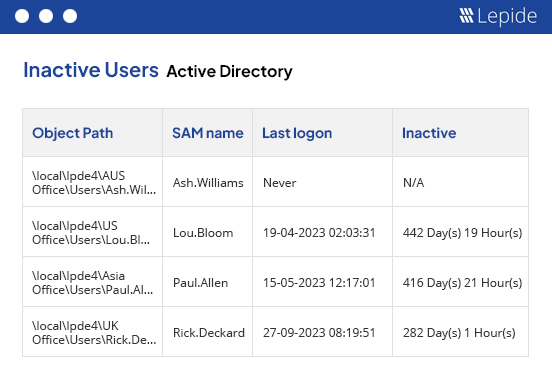
Educational environments often contain inactive student, faculty, contractor, and service accounts that create hidden security risk. Lepide helps you identify dormant accounts, privileged users, and stale permissions so you can reduce your attack surface and improve identity hygiene.
“Lepide reduced the risk of data breaches and ransomware attacks. The solution gives me complete visibility over what is happening on my network with respect to access of network resources.”

Reduce your threat surface by identifying over-exposed data, spotting misconfigurations, and auditing changes with
Lepide Auditor 🠂 Access GovernanceSee who has access to sensitive data, spot users with excessive permissions and govern access to data with
Lepide Trust 🠂 Threat DetectionDetect and react to threats with AI-led anomaly detection, alerts, threat models, and automated threat response with
Lepide Detect 🠂Identify where your most sensitive unstructured data is located, and classify data at the point of creation with
Lepide Identify 🠂 Permissions ManagementRemove excessive permissions to implement zero trust with
Lepide Protect 🠂 AI SOC AnalystA powerful, always-on member of your security team that transforms security visibility into actionable AI-driven insight.
Lepide AI 🠂A guided tour of the Lepide Data Security Platform, your ultimate solution for robust and proactive data and identity protection.
View recording