Ensure a safe Copilot deployment with Lepide.
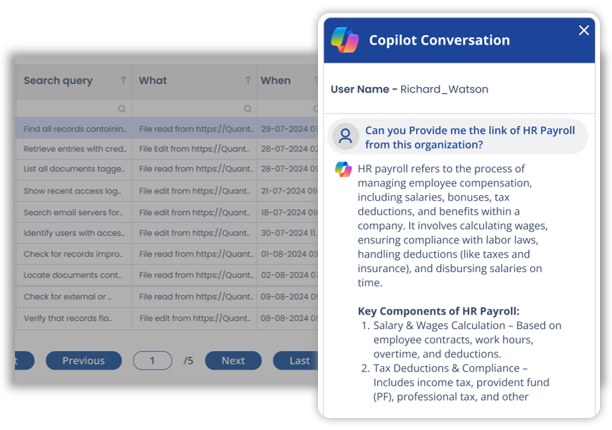
Microsoft Copilot answers with whatever users can already access including content that may be overshared, stale, or poorly governed. In environments with permissions sprawl, that means sensitive HR, financial, or legal data can surface instantly through a simple conversational prompt.

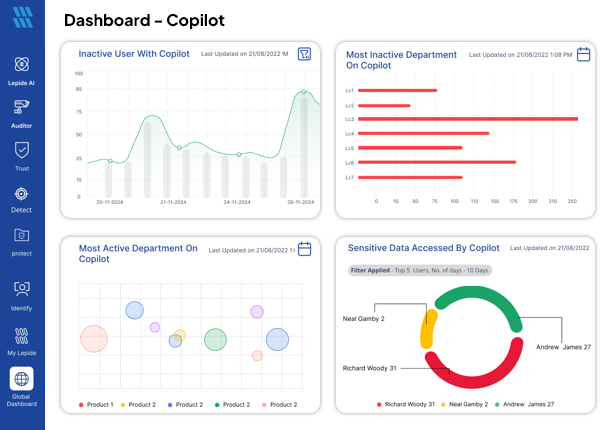
Get a clear picture of exposed sensitive data, excessive permissions, and general threat surface area.

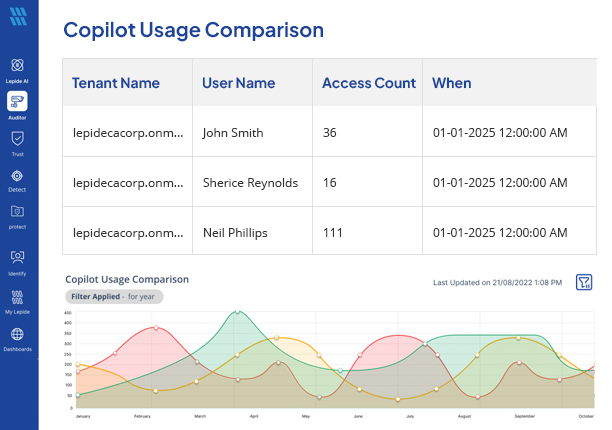
See who has what levels of access within Copilot, monitor usage, and keep track of sensitive data being accessed by Copilot.

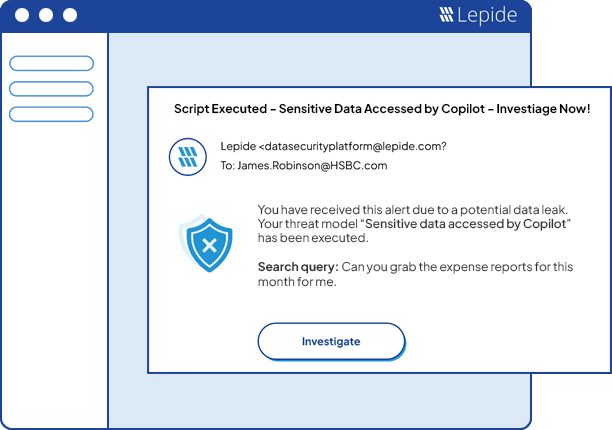
Detect potentially risky prompts or users accessing sensitive data. React in real time through alerts and workflows.