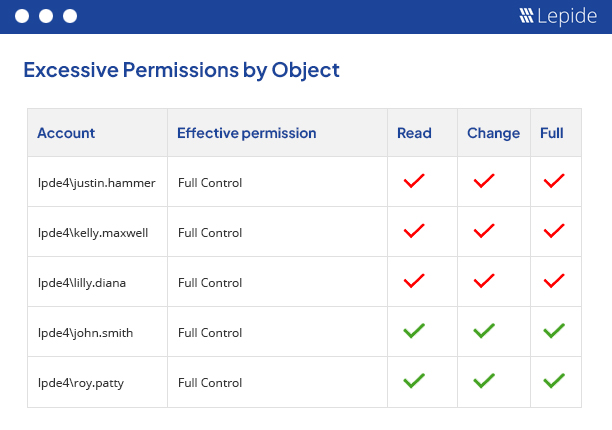
Identify over-permissioned users, dormant accounts, and privileged access before they expose sensitive financial and operational data across your environment.
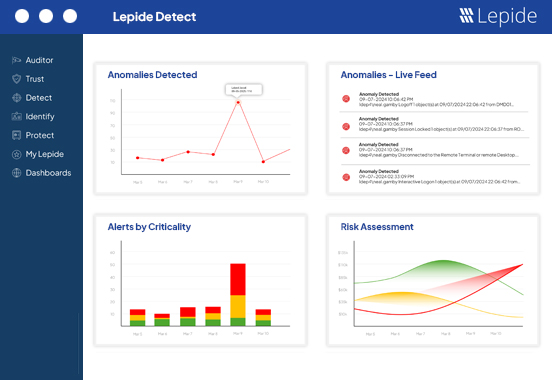
Track user behavior, permission changes, failed logons, and unusual access patterns in real time to detect threats earlier and accelerate investigations.
Understand how access is inherited across Active Directory, Microsoft 365, file servers, and hybrid environments so you can reduce unnecessary access and limit risk.
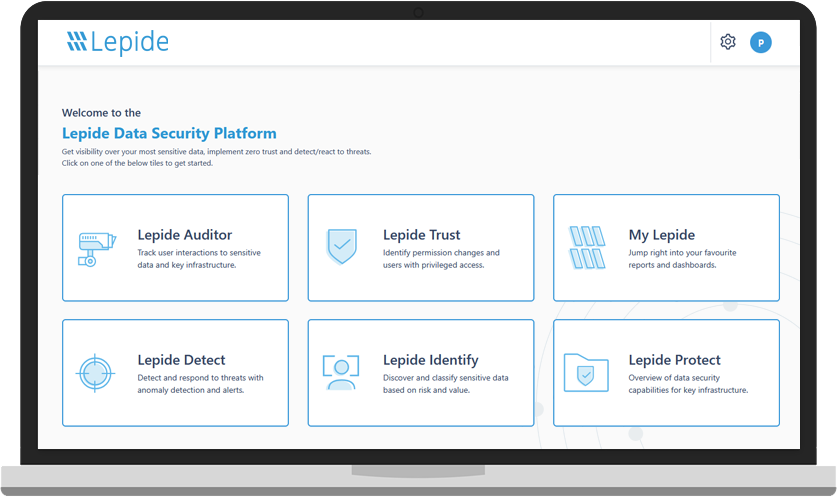
Financial institutions often struggle with excessive permissions, privileged account exposure, fragmented visibility, and increasing pressure to strengthen security controls across hybrid environments. Lepide helps security and IT teams uncover hidden access risks, monitor suspicious activity, and protect sensitive financial data across Active Directory, Microsoft 365, and file servers.
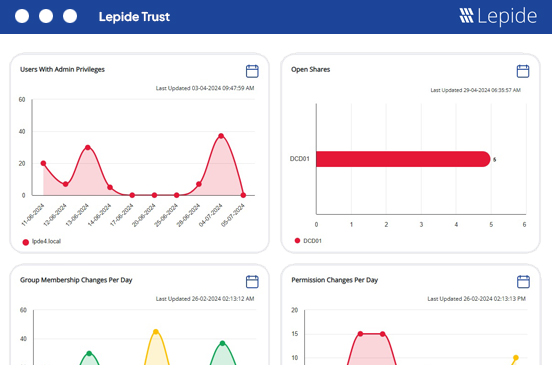
Financial organizations manage large numbers of privileged users, third-party accounts, and inherited permissions that create hidden security risk. Lepide helps you identify excessive access, monitor privileged groups, and detect risky changes before they lead to data exposure or compliance issues.
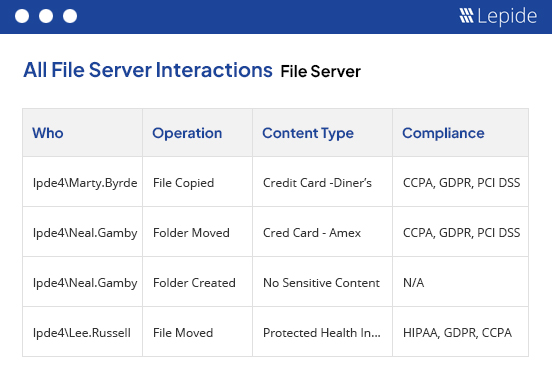
Monitor user behavior, failed logons, permission changes, and unusual access patterns across Active Directory, Microsoft 365, and file servers through centralized auditing and real-time visibility. Lepide helps security teams investigate threats faster while reducing operational overhead.
Understand exactly who can access sensitive financial data and how permissions are inherited across your environment. Lepide helps financial institutions reduce unnecessary access, improve identity hygiene, and enforce least privilege policies without disrupting operations.
Generate audit-ready reports for SOX, PCI DSS, GDPR, GLBA, and other regulatory requirements while maintaining visibility into user activity, permission changes, and access to sensitive financial data.

“Lepide saved money and time. Their sales rep answered my questions quickly and our examiners really like the solution. The solution itself is really easy to use, manage and configure for our requirements. I’d give it a solid 9/10.”
Reduce your threat surface by identifying over-exposed data, spotting misconfigurations, and auditing changes with
Lepide Auditor 🠂 Access GovernanceSee who has access to sensitive data, spot users with excessive permissions and govern access to data with
Lepide Trust 🠂 Threat DetectionDetect and react to threats with AI-led anomaly detection, alerts, threat models, and automated threat response with
Lepide Detect 🠂Identify where your most sensitive unstructured data is located, and classify data at the point of creation with
Lepide Identify 🠂 Permissions ManagementRemove excessive permissions to implement zero trust with
Lepide Protect 🠂 AI SOC AnalystA powerful, always-on member of your security team that transforms security visibility into actionable AI-driven insight.
Lepide AI 🠂A guided tour of the Lepide Data Security Platform, your ultimate solution for robust and proactive data and identity protection.
View recording