To check user login history in Windows Active Directory, enable Audit Logon Events via Group Policy, then search for Event IDs 4624, 4625, 4634, 4647, and 4648 in Windows Event Viewer.
Quick Summary
- Enable “Audit Logon Events” and “Audit Account Logon Events” in Group Policy Management Console
- Configure the GPO path: Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Audit Policy
- Search Event ID 4624 (successful logon) and 4648 (explicit credentials) for user logins
- Search Event ID 4625 for failed logon attempts
- Search Event IDs 4634 and 4647 for logoff events
Key Terms
Active Directory user login history refers to the record of when users authenticate to domain-joined computers and resources, including successful logins, failed attempts, and logoff events.
Logon Event IDs are specific Windows Security log identifiers (such as 4624, 4625, 4648) that categorize different types of authentication events.
Group Policy auditing is the process of configuring Windows Group Policy Objects (GPOs) to track and log security events across domain computers.
Prerequisites
Before starting, ensure you have:
- Domain Admin privileges or equivalent permissions
- Access to Group Policy Management Console (GPMC
- Access to Windows Event Viewer on domain controllers
- These steps apply to Windows Server 2016, 2019, and 2022
IT administrators often need to know who logged on to their computers and when for security and compliance reasons. Although you can use the native auditing methods supplied through Windows to track user account logon and logoff events, you may end up having to sift through thousands of records to reach the required log. Once you’ve found the required log, getting the required information for compliance and security reports is not an easy process.
Below are the steps to check Active Directory user login history using logon Event IDs.
- Enable Auditing for User Logon/Logoff Events
- Search Relevant Event IDs such as 4624, 4648 etc. in Event Viewer
Step 1- Enable Auditing for User Logon/Logoff Events
You can do this through two GPO settings:
1. Audit Logon Events: This setting generates events for starting and ending logon sessions. These events happen on the machine where you log in.
2. Audit Account Logon Events: This setting generates events on the computer that validates logons. When a domain controller authenticates a domain user account, events are generated and stored on that domain controller.
Below are the steps to enable auditing of user Logon/Logoff events:
- Open the “Group Policy Management” console by running the “gpmc.msc” command.
- If you want to configure auditing for the entire domain, right-click on the domain and click “Create a GPO in this domain, and Link it here…”.
- Create a new GPO dialog box that appears on the screen. Enter a new GPO name.
- Go to the new GPO, right-click on it, and select “Edit” from the context menu.
- “Group Policy Management Editor” window appears on the screen.
- In the navigation pane, go to “Computer Configuration” ➔ “Policies” ➔ “Windows Settings” ➔ “Security Settings” ➔ “Local Policies” ➔ “Audit Policy”.
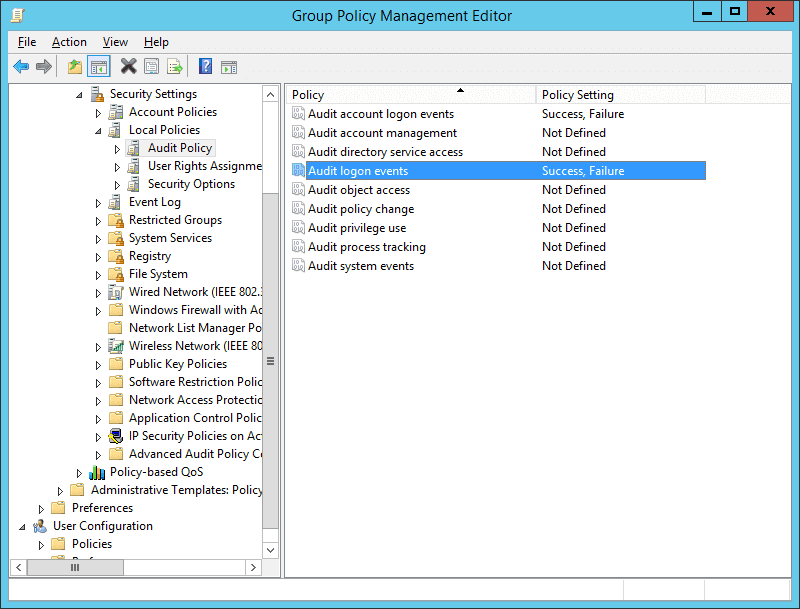
Figure: Configuring audit logon events policy - In the right pane, double-click the “Audit logon events” policy to open its properties window.
- Select the “Success” and “Failure” checkboxes, and click “OK”.
- Similarly, you have to enable “Success” and “Failure” for “Audit Account Logon Events”.
- Close “Group Policy Management Editor”.
- Now, you have to configure this new Group Policy Object (containing this audit policy) on all Active Directory objects including all users and groups. Perform the following steps.
- In In “Group Policy Management Console”, select the new GPO (containing the above change).
- In the “Security Filtering” section in the right panel, click “Add” to access the “Select User, Computer or Group” dialog box.
- Type “Everyone”. Click “Check Names” to validate this entry. Click “OK” to add it and apply it to all objects.
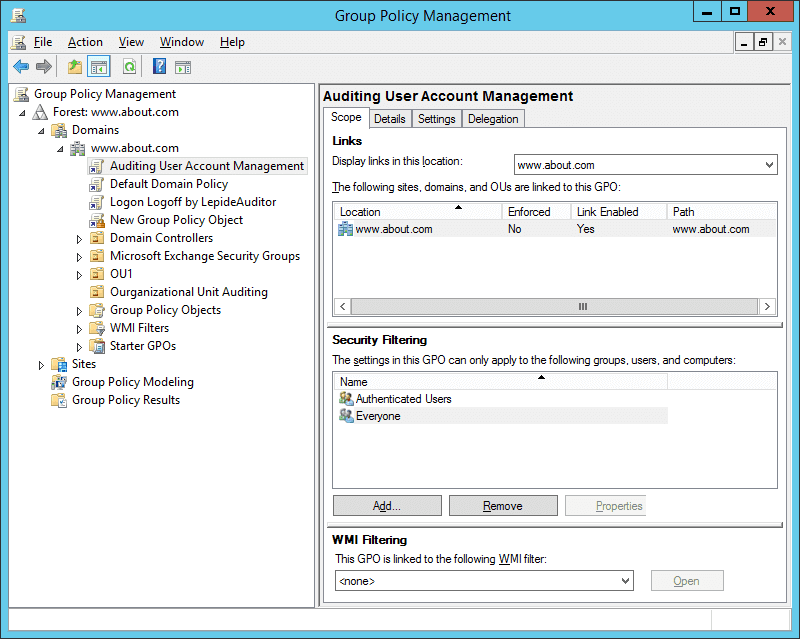
Figure : Applied the Group Policy Object to everyone - Close “Group Policy Management Console”.
- Now, run the following command to update GPO.
- gpupdate /force
Step 2- Search Relevant Logon Event IDs in Windows Event Viewer
After you have configured log on auditing, whenever users logon into network systems, the event logs will be generated and stored. To find out the details, you have to use Windows Event Viewer. Follow the below steps to view logon audit events:
- Go to Start ➔ Type “Event Viewer” and click enter to open the “Event Viewer” window.
- In the left navigation pane of “Event Viewer”, open “Security” logs in “Windows Logs”.
- You will have to look for the following event IDs for the purposes mentioned herein below.
For user logon, you have to search for 4624 and 4648 logon event IDs. For failed logon, you have to search for 4625. For logoff events, you have to search for 4634 and 4647.
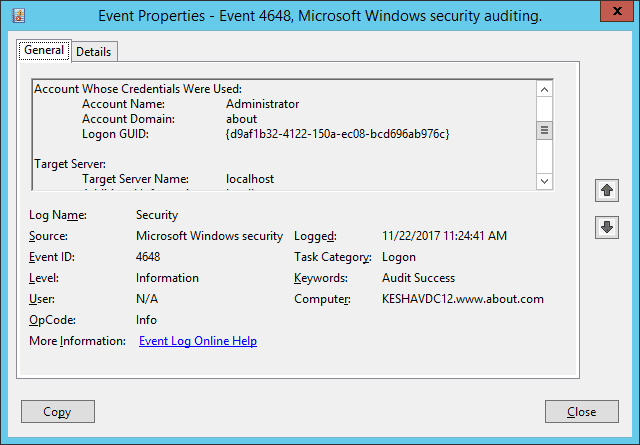
In this article, we are searching for logon event IDs 4624 and 4648. The following screenshot shows Windows Event ID 4648 for the user logon attempted using explicit credentials.
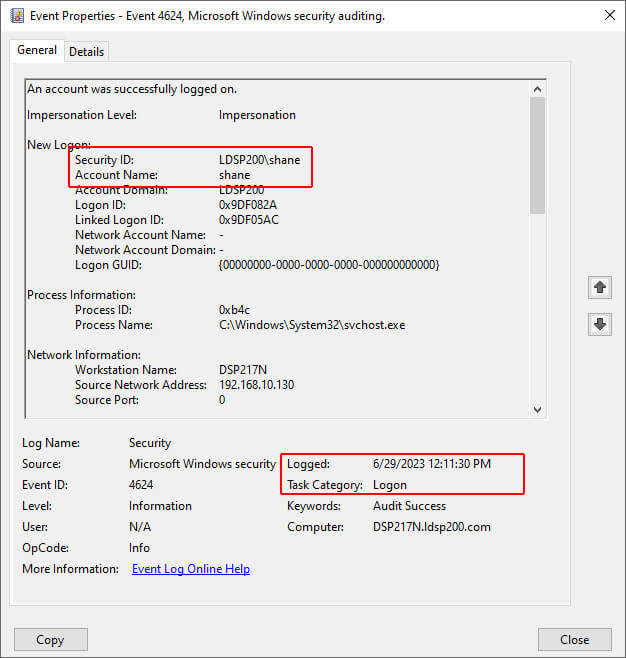
The following screenshot of Windows Event ID 4624 shows the session start time is displayed as Logged. In the Event Properties given below, a user, Shane, had logged in on 6/29/2023 at 12:11:30 PM.
Check User Login History with Lepide’s Free Tool for AD Auditing
Using Lepide Change Reporter for AD, you can easily monitor AD users’ login history by tracking their logon and logoff activities in real-time. The solution collects log on information from all added domain controllers automatically. Its report contains details on logon or logoff events, including when users logged in, from which computer, and when. You get accurate and instant reports on the login details of users in the network. The following screenshot shows a successful user logon report event captured by Lepide’s free tool::
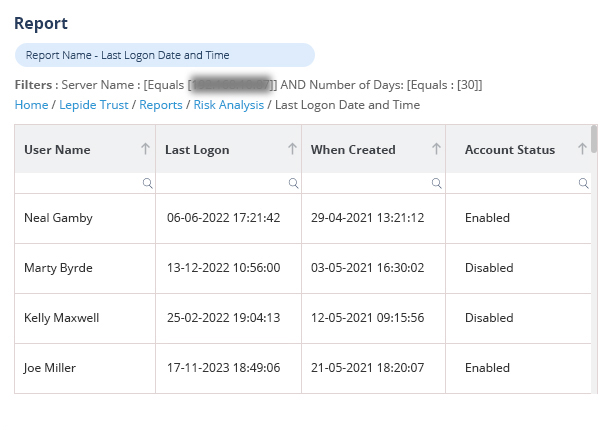
Lepide Change Reporter provides following reports related to logon/logoff:
Frequently Asked Questions
What Event ID shows successful login in Active Directory?
How do I enable login auditing in Active Directory?
Where are login logs stored in Windows?
What is the difference between Event ID 4634 and 4647?
Conclusion
In this article, the steps to audit the user logon and logoff events through native auditing are explained. However, much noise is generated for the logon or logoff events that make it complicated for the IT administrators to have a real-time view. The easiest and more efficient way to audit the same with Lepide’s Active Directory Auditing Free Tool has also been explained.

