Last Updated on January 14, 2025 by Deepanshu Sharma
Indicators of compromise (IOCs) are events found in log files that are signs of potentially malicious activity. Cybersecurity teams can scrutinize event logs to identify data breaches, malware attacks, and other security threats. In doing so they can respond to anomalous events in a timely manner, thus limiting the damage they can cause.
Unfortunately, IOCs are not easy to detect, as the indicators can be both subtle and complex. Such events may include metadata elements, code, and content samples. It can take time to draw correlations between multiple events in order to establish a clear view of what happened, by who, and when.
The Difference Between Indicators of Compromise (IOCs) and Indicators of Attack (IOAs)
Indicators of compromise (IOCs) and indicators of attack (IOAs) are similar, in that they are both signs of potentially malicious activity. However, IOCs focus more on forensic analysis following a security incident, whereas IOAs help organizations identify the potentially malicious activity as it occurs. Security teams must continuously monitor the event logs for both IOCs and IOAs, if they are to mitigate cyber-attacks.
Examples of Indicators of Compromise
Below are some of the common activities to look out for that may indicate that a security incident has, or is, unfolding:
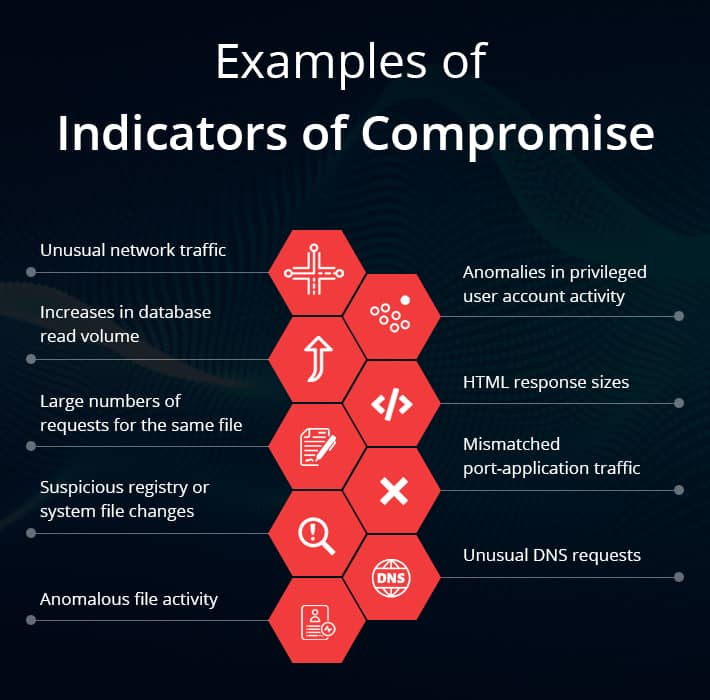
Unusual network traffic
Network traffic can be monitored by security teams for anomalous patterns to help prevent data breaches. For example, suspicious outbound network traffic might suggest that an attacker is trying to exfiltrate data.
Anomalies in privileged user account activity
Failed login attempts, out-of-hours access, access via unrecognized devices and locations, and users attempting to elevate their privileges, are just some of the IOCs and IOAs we can look out for that are associated with privileged user accounts.
Increases in database read volume
Unusual increases in your database read volume may imply that an adversary is trying to perform a database dump.
HTML response sizes
If Hypertext Markup Language (HTML) response sizes are larger than normal, this could be a sign that an attacker is trying to steal your data.
Large numbers of requests for the same file
If an attacker is trying to steal a specific file, they may try numerous different ways to obtain it. If your security team detects multiple requests for the same file, this could be an IOC/IOA.
Mismatched port-application traffic
Applications rely on ports to exchange data with a network. Certain hacking tools and even some types of malware will try to leverage obscure ports to either access the network or exfiltrate data.
Suspicious registry or system file changes
In some cases, malware will make changes to registry or system files. Establishing a baseline will help security teams monitor for such changes.
Unusual DNS requests
Adversaries will frequently make use of command-and-control (C&C) servers to exfiltrate data from a network. Domain Name System (DNS) requests that come from an unknown host could be signs of an IOC. Likewise, excessive DNS requests could be signs of a Distributed Denial of Service (DDoS) attack.
Anomalous file activity
Attackers may try to transfer a large number of files to their C&C server, or, in the case of a ransomware attack, the malicious script will try to encrypt the files on your network. A real-time file auditing solution will establish a baseline that represents typical file usage patterns. This baseline can be tested in order to identify IOCs and IOAs. It’s worth noting that some sophisticated auditing solutions can detect and respond to events that match a pre-defined threshold condition, which can help to identify ransomware attacks and other attack vectors that perform repetitive actions. For example, if x number of files are encrypted within a given time-frame, a custom script can be executed which can disable a user account, stop a specific process, change the firewall settings, or shut down the affected server.
How Lepide Can Help Detect Indicators of Compromise and Indicators of Attack
Lepide gives organizations the ability to detect anomalous user behavior when it comes to interactions and changes being made to sensitive data and critical infrastructure. Lepide establishes what normal user behavior looks like over a given learning period, and then sends real-time alerts to administrators whenever any deviations from the norm take place.
Lepide comes with hundreds of pre-defined threat models specifically designed to detect indicators of attack related to common security threats, such as ransomware, brute force attacks, and compromised user accounts. For example, if a user account were to modify the extension name of 500 files in 30 seconds, it could be an indication that the account has been hijacked for an ongoing ransomware attack. Similarly, if hundreds of account lockouts are taking place over a very short period of time, it could indicate a brute force attack.
Lepide is also able to provide forensic investigation capabilities through a detailed audit log so that administrators can perform scans for indicators of compromise. For example, Lepide analyzes the effective permissions of users and then determines, based on their data usage patterns, whether those access rights are excessive.
If you’d like to see how the Lepide Data Security Platform can help you spot indicators of compromise and indicators of attack, schedule a demo with one of our engineers.



