Last Updated on January 17, 2025 by Deepanshu Sharma
The Cybersecurity Maturity Model Certification (CMMC) is essentially a data security framework that was developed by the U.S. Department of Defense (DoD) and applies to Defense Industrial Base (DIB) contractors. The purpose of the CMMC is to ensure that sensitive national security information is protected from unauthorized access. It helps to set priorities for protecting DoD information and cuts red tape for small and medium-sized businesses. CMMC was introduced in 2019 and will come into effect in May 2023. Any company that wants to do business with the DoD, must comply with the CMMC.
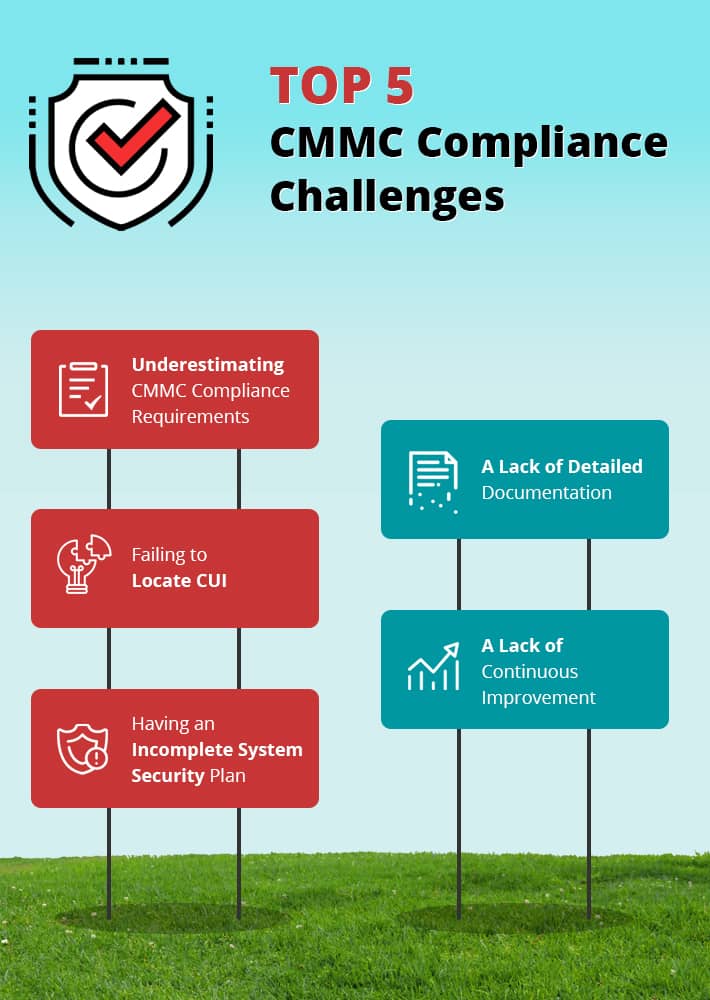
Top 5 CMMC Compliance Challenges
There is plenty of information online about the CMMC requirements, however, sometimes is it worth taking a look at some of the challenges that might arise when trying to comply, which include;
1. Underestimating CMMC Compliance Requirements
It is inevitable that any company that deals with the DOD will already have safeguards in place to protect DoD information, and those safeguards are likely to be robust and effective. However, the problem is that companies may naturally assume that they are already compliant, or at least, they will be after making a few small changes.
The reality of the situation is that CMMC compliance can take months to achieve. It requires careful planning and research into different technologies, the introduction of new processes and procedures, and of course, employees will need to be trained accordingly.
2. Failing to Locate CUI
DIB contractors are required to handle Controlled Unclassified Information (CUI), which, as the name suggests, is not classified information, but is still essentially owned by the Government, and thus needs to protect. A common problem is that companies often fail to locate or identify the CUI they store. The result is that the controls they use to protect CUI are too broad, which leads to unnecessary costs and complexities.
3. Having an Incomplete System Security Plan
A System Security Plan (SSP) is a formal, written plan that describes the infrastructure, the associated risks, and security controls in place to mitigate those risks. It also describes the boundaries of the system, as well as its relationship with other systems. This requires diagrams that clearly illustrate the topology of the network, including users, data flows, services, technologies, processes, procedures, and so on. Another issue that frequently arises is that companies often fail to include supply chain partners and other business associates in their CMMC compliance strategy. By default, very few organizations have an SSP that is comprehensive enough to meet the requirements of the CMMC.
4. A Lack of Detailed Documentation
In addition to lacking a comprehensive SSP, many companies don’t spend enough time creating detailed documentation about their system. For example, companies should provide clear documentation about the way event logs are collected, stored, and analyzed. They should also develop detailed documentation about the access controls they have in place, how those controls are reviewed, granted, and revoked, and how important configuration changes are handled.
5. A Lack of Continuous Improvement
As with other data protection regulations, compliance is not a one-time process, but a cyclical process that requires constant monitoring and improvement. Fortunately, there are real-time monitoring solutions that can help to automate the process. For example, most sophisticated real-time auditing solutions use machine learning models to detect and respond to anomalous events, which require minimal human intervention. They can also detect and respond to events that match a pre-defined threshold condition, such as when a large number of files are copied or encrypted within a given time frame. In this case, a custom script can be executed which may change the security settings, disable accounts and processes, and even shut down the affected server. Additionally, security awareness training must be ongoing and aligned with the evolving threat landscape.
How can Lepide Help with CMMC Compliance?
As mentioned above, companies often fail to identify their controlled unclassified information, and thus end up applying controls too broadly.
The Lepide Data Security Platform provides data discovery and classification that can be configured to identify specific data types, such as CUI. The platform comes with a centralized dashboard where you can review all changes to your CUI, and generate pre-defined compliance reports at the click of a button. Lepide uses advanced machine learning techniques to identify anomalous user behavior, and can also respond to threats like ransomware, brute force attacks, and more, automatically through any one of the pre-defined threat models.
If you’d like to see how the Lepide Data Security Platform can help you comply with the CMMC, schedule a demo with one of our engineers.



