Last Updated on May 23, 2025 by Deepanshu Sharma
Ransomware is becoming more sophisticated and effective, making it difficult to detect and prevent. The availability of cryptocurrencies, which are often used to pay ransoms, and the anonymity they provide to attackers, have also made it more attractive for malicious actors to engage in Ransomware attacks. In 2022, ransomware accounted for around 20% of all cybercrimes, according to an article by AAG.
Cybercriminals typically use social engineering tactics to trick users into downloading and opening a malicious file or link, often disguised as something harmless or desirable. Once the file is activated, ransomware can rapidly move through a network, encrypting data and making it inaccessible to users. Additionally, it can be delivered through exploit kits, which are automated tools that inject malicious code into vulnerable systems.
How Ransomware Spreads
Below are some of the main ways ransomware can enter and infect systems:
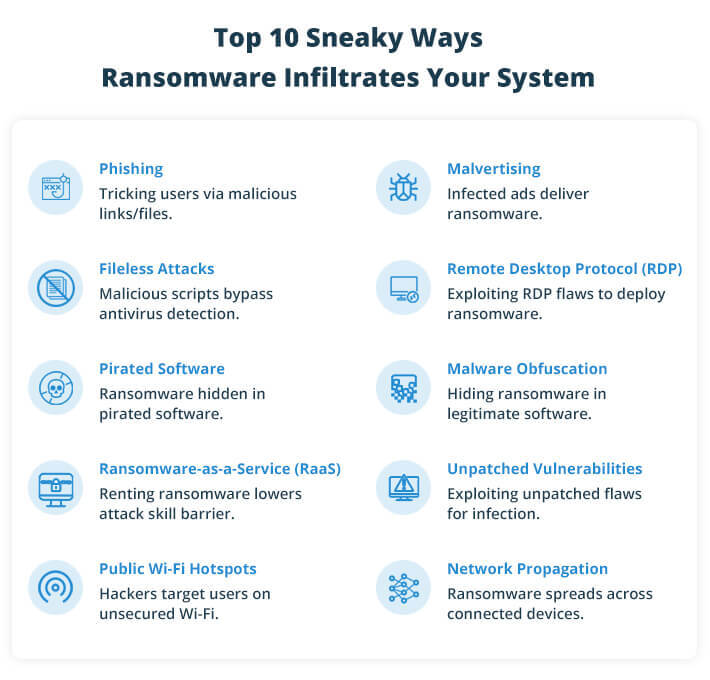
1. Social Engineering / Phishing
Phishing is the most common entry point for ransomware. Attackers trick victims into downloading harmful files, clicking on malicious links, or handing over credentials. Social media is also used to send infected links to friends, family, and acquaintances.
2. Malvertising
Attackers embed malicious code in ads, which can install ransomware when clicked. These malicious ads can appear on websites, social platforms, or other online services. During the peak of the COVID-19 pandemic, malvertising attacks surged by over 70%, according to ProPrivacy.
3. Fileless Attacks
Instead of traditional files, attackers use malicious scripts that exploit legitimate system tools to download and run ransomware. Fileless attacks evade detection by antivirus software and are becoming a preferred delivery method. WatchGuard reported a nearly 900% increase in fileless malware attacks between 2019 and 2020.
4. Remote Desktop Protocol (RDP)
RDP vulnerabilities allow attackers to gain unauthorized access to systems. Once inside, they can deploy ransomware that encrypts data and targets other systems on the network. According to Palo Alto’s 2020 Incident Response and Data Breach Report, RDP was used in 50% of ransomware incidents.
5. Pirated Software
Downloading pirated software puts users at high risk of infection. Attackers may disguise ransomware as legitimate software. BleepingComputer reported a major Ryuk ransomware attack at a European biomolecular research institute triggered by pirated software downloads.
6. Malware Obfuscation
Attackers hide malicious code in legitimate programs using techniques like encryption and obfuscation, making it harder for security solutions to detect the threat.
7. Ransomware-as-a-Service (RaaS)
RaaS allows malicious actors to rent ransomware tools, making it easier for less skilled hackers to launch attacks. RaaS often includes customization options and technical support, allowing for widespread targeting.
8. Zero-Day/Unpatched Vulnerabilities
Exploiting unpatched vulnerabilities is a common method used in ransomware attacks. For instance, Community Health Systems (CHS) faced a ransomware attack in early 2023, which exploited a zero-day vulnerability, affecting over 1 million patients, as reported by TechCrunch.
9. Public Wi-Fi Hotspots
Hackers exploit weak security in public Wi-Fi hotspots, using them to send phishing emails or launch ransomware attacks on unsuspecting users connected to the same network.
10. Network Propagation
Once ransomware infects one system, it can propagate to other devices on the same network through vulnerable software, emails, or links. This ability to replicate makes ransomware difficult to contain.
Download ebook
How to Prevent Ransomware Attacks
While no organization can be 100% immune to ransomware, certain best practices can significantly reduce the risk of infection:
- Regular Backups – Ensure that data is backed up regularly and stored offline. In case of a ransomware attack, having backups allows for quick data recovery without paying the ransom.
- User Awareness Training – Educate employees about phishing attacks and how to identify suspicious emails or links. Human error is often the weakest link in cybersecurity, so training can go a long way in preventing ransomware from infiltrating the network.
- Update and Patch Systems – Keep all software, operating systems, and security tools up to date. Vulnerabilities in outdated software are often exploited by ransomware attackers.
- Implement Multi-Factor Authentication (MFA) – Adding an extra layer of security through MFA can help prevent unauthorized access to systems, even if credentials are stolen.
- Network Segmentation – Isolate critical data and services from the rest of the network. This limits the spread of ransomware and reduces the damage if an attack occurs.
- Disable Remote Desktop Protocol (RDP) if Not Needed – RDP is a common attack vector for ransomware. If it’s not necessary for your organization, disabling it can reduce exposure to attacks.
- Employ Least Privilege Access – Restrict user permissions to only what is needed to perform their tasks. This minimizes the damage ransomware can cause by limiting access to sensitive data.
How Lepide Helps
The Lepide Data Security Platform helps to mitigate the impact of ransomware by automating responses to suspicious activities. For example, Lepide can detect and respond to mass file renaming, one of the common signs of a ransomware attack, by automatically locking user accounts or shutting down suspicious processes before the damage spreads.
If you want to know more about how Lepide Ransomware Protection Solution can help you protect against Ransomware attacks, schedule a demo with one of our engineers today.



