Last Updated on May 23, 2025 by Deepanshu Sharma
With the rise of digital transformation, the prevalence of ransomware attacks has come to the forefront of cybersecurity concerns. Ransomware attackers use various methods to infiltrate networks and encrypt data, holding it hostage for a ransom payment. These attack vectors are becoming increasingly sophisticated, using social engineering tactics and exploiting vulnerabilities to gain access to systems. Understanding the different types of ransomware attack vectors is crucial for organizations to develop effective prevention and response strategies.
What is an Attack Vector?
An attack vector is a method or pathway that cybercriminals use to infiltrate a network, system, or device to carry out malicious activities. Attack vectors can range from exploiting vulnerabilities in software and hardware to manipulating human behavior through social engineering tactics. Once these vectors are successfully used, attackers can execute harmful actions like data theft, ransomware deployment, or even complete system control.
Understanding attack vectors is critical to protecting your organization against threats like ransomware. By identifying how attackers gain access to your environment, you can implement targeted security measures to reduce risk.
Top Ransomware Attack Vectors
Let’s explore some of the most common ransomware attack vectors that organizations should be aware of.
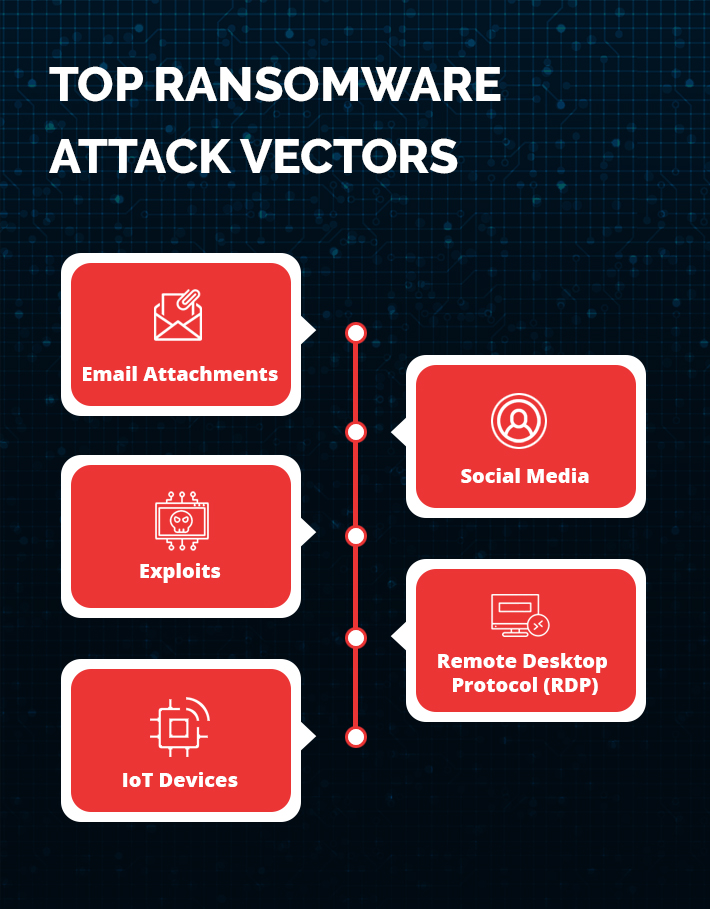
1. Email Attachments
Attackers send malicious software disguised as attachments or links in emails. They trick users into opening the attachment that leads to downloading the malware on their device. The 2017 WannaCry ransomware attack, which targeted a vulnerability in Microsoft Windows operating systems, first arrived in the form a phishing email that contained a malicious attachment.
Mitigation: Exercise caution when receiving emails from unfamiliar senders. Be wary of unexpected requests and examine file names carefully. Refrain from opening any EXE files, approach ZIPs and RARs with caution, and be prudent when opening Office Documents.
2. Social Media
Attackers spread ransomware programs via social media by disguising them as attractive content. Once users click on the embedded links, they are redirected to download the ransomware. The Locky ransomware attack targeted Facebook users in 2016 and spread rapidly through other social media platforms. Cybercriminals spread the ransomware through fake messages with malicious attachments that appeared to be sent by friends.
Mitigation: When using social media, be careful about clicking on suspicious links or downloading unknown attachments. It is important to always verify the sender of a message and to avoid interacting with messages from unknown sources.
3. Exploits
Exploits are vulnerabilities in software or operating systems that attackers leverage to install ransomware on the compromised system. In 2021, multiple hacking groups launched attacks against Microsoft Exchange email servers using zero-day vulnerabilities. Another example is the North Korean government-backed threat actors who exploited a zero-day vulnerability in Google Chrome to target US organizations from the media, high-tech, and financial sectors.
Mitigation: Ensure that updates/patches are installed as soon as they become available. Consider using an automated patch-management solution.
4. Remote Desktop Protocol (RDP)
Attackers’ brute-force passwords or use stolen credentials to access remote desktop services like Microsoft Remote Desktop or TeamViewer to install ransomware on victims’ devices. According to the 2020 Unit 42 Incident Response and Data Breach Report, remote desktop protocol (RDP) services were the initial attack vector in 50% of ransomware deployment cases. RDP services have been a popular attack vector for years, particularly for use in small enterprises where phishing emails may not be as successful. The Ryuk ransomware variant commonly uses compromised user credentials to log into enterprise systems using the Remote Desktop Protocol (RDP).
Mitigation: Firstly, it is important to enforce strong passwords and use two-factor authentication for all remote access. Additionally, regularly patching and updating the operating system and all software related to RDP can prevent vulnerabilities from being exploited by attackers. Moreover, limiting the number of RDP ports exposed to the internet can narrow the attack surface and lessen the ability for attackers to find weak spots. It is also recommended to use Virtual Private Networks (VPNs) to secure RDP connections as they encrypt all communication between endpoints.
5. IoT Devices
Attackers exploit vulnerabilities in IoT (Internet of Things) devices such as smart thermostats, lighting systems, and security cameras to install ransomware on the connected network. LockerGoga is a ransomware variant that was first discovered in January 2019, which targets industrial control systems (ICS) and IoT devices. The attack has been linked to several high-profile incidents, including an attack on Norsk Hydro, one of the world’s largest aluminum producers.
Mitigation: To protect IoT devices from ransomware it is important is to install security software on all devices that enable real-time monitoring of threats. You will also need to keep all IoT software up to date, as manufacturers regularly release security updates and patches to fix vulnerabilities.
How to Avoid Becoming a Victim of Ransomware
To avoid falling prey to ransomware attacks, it’s essential to adopt a proactive, multi-layered defense strategy. Here are some key preventive measures:
- Regular Software Updates and Patch Management: Cybercriminals often exploit vulnerabilities in outdated software to deliver ransomware. According to a recent study, over 60% of ransomware attacks are caused by unpatched software vulnerabilities. Regularly updating and patching your systems reduces this risk.
- Strengthen Email Security: Phishing is still the most common ransomware delivery method, accounting for more than 90% of successful attacks. Educating employees on how to recognize phishing emails and using advanced email filtering tools are essential for blocking malicious emails.
- Implement Multi-Factor Authentication (MFA): Weak or stolen credentials are a significant attack vector. MFA adds an extra layer of security by requiring users to verify their identity through multiple methods, significantly lowering the risk of credential-based attacks.
- Backup Critical Data Regularly: Backing up your data is the best defense against ransomware, as it allows you to restore your systems without paying the ransom. Ensure that backups are frequent, encrypted, and stored in isolated environments to prevent ransomware from corrupting them.
- User Education and Training: Educating employees about the dangers of ransomware and how to identify suspicious behavior is vital. Studies have shown that organizations with comprehensive security training programs are 70% less likely to experience a ransomware breach.
- Use Threat Detection and Response Tools: Leveraging advanced threat detection solutions, like Endpoint Detection and Response (EDR) or Security Information and Event Management (SIEM) tools, helps identify and mitigate potential threats in real-time.
How Lepide Helps Protect Against Ransomware
The Lepide Data Security Platform provides the visibility you need to detect and respond to ransomware attacks in real-time. Using the “threshold alerting” feature, specific threshold conditions can be set to trigger alerts and automatic responses, preventing the attack from spreading. For instance, if a certain number of files are encrypted or renamed within a given time frame, a custom script can be executed to halt a process, disable a user account, adjust the firewall settings, or shut down the affected systems. Real-time notifications are sent each time changes are made to important files, folders, and security settings, while an easy-to-use dashboard allows for reviewing access permissions to determine who should have access to what resources.
If you’d like to see how the Lepide Data Security Platform can help you defend against ransomware attacks, schedule a demo with one of our engineers.


