Ransomware Detection Solution
Ransomware is a serious threat to the security of the IT environment. Ransomware can be easily detected and prevented through a combination of stringent audit policies, data governance and employee vigilance.














The only way to truly defend against ransomware is to keep software up-to-date, take regular backups, secure your network with an endpoint security solution and audit your IT environment. Here at Lepide, our focus is on providing you visibility over what’s happening with your data. Through visibility, you can speed up the detection of potential ransomware and automate your response. Detect and react quicker to ransomware using Lepide.
Get real time alerts for suspicious changes being made that could indicate a ransomware attack in progress.
Find out who has access to your data and how it was granted, so that you can ensure proper data access governance.
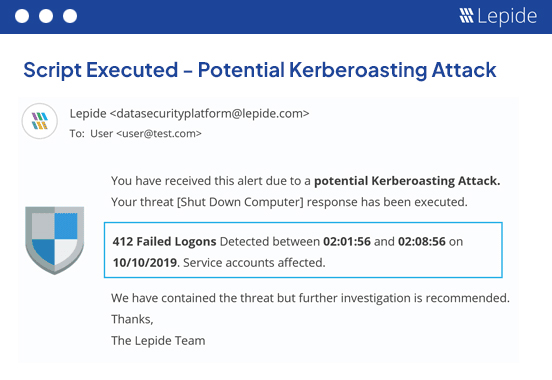
Upon detection of unwanted changes, execute automated scripts to take appropriate remediation action.
Through anomaly spotting and threshold alerting you can detect suspicious change activity that could be indicative of a ransomware attack in progress. Detect sudden permission changes or anomalous user behavior that could be a symptom of the attack.
Learn more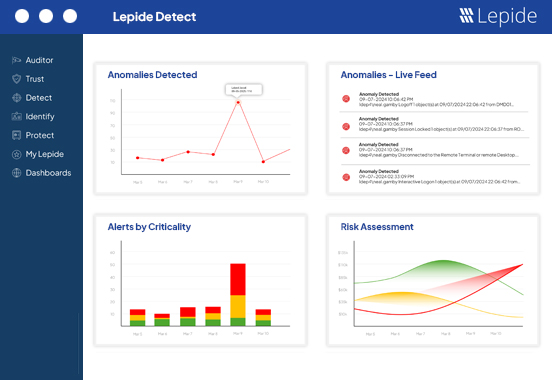
Automate your response to potential ransomware threats through real time script executions. Custom scripts can be executed when threshold conditions are met to automatically shut down potential threats before they cause more harm. For example, if 300 files are renamed by one user in 30 seconds, shut down the user account, contain the threat.
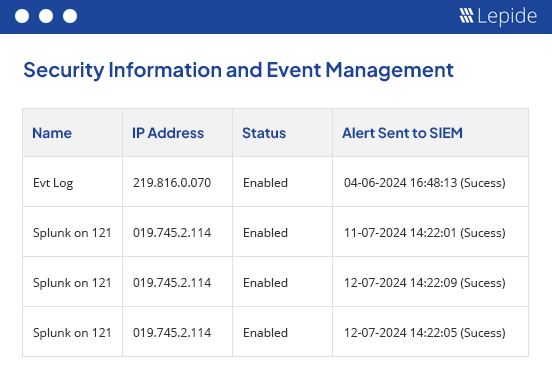
Streamline your security operations and response to threats by providing visibility over ransomware attacks. Integrate with SIEM to add full context to changes being made, with real time alerts that provide actionable information, so that you can respond more quickly and meaningfully.
By following the guidelines outlined in this paper, your organization can establish a robust data access governance program that supports its business objectives and protects your valuable data assets.
Get the free guide now!