



























Monitor employee interactions with sensitive data
Real time alerts for anomalous user behavior
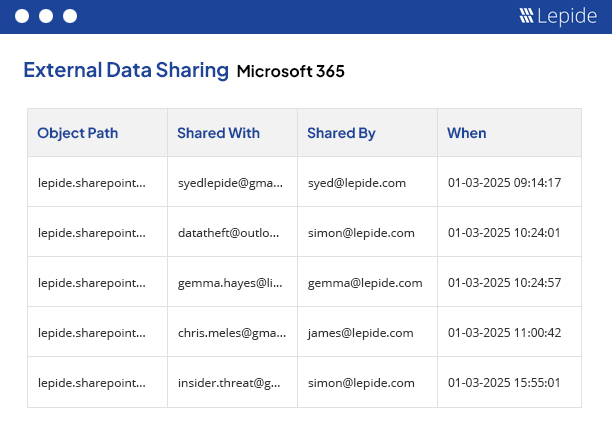
Monitor how sensitive data is being shared across MS Teams
Audit logon/logoff activity and password resets
By following the guidelines outlined in this paper, your organization can establish a robust data access governance program that supports its business objectives and protects your valuable data assets.
Get the free guide now!