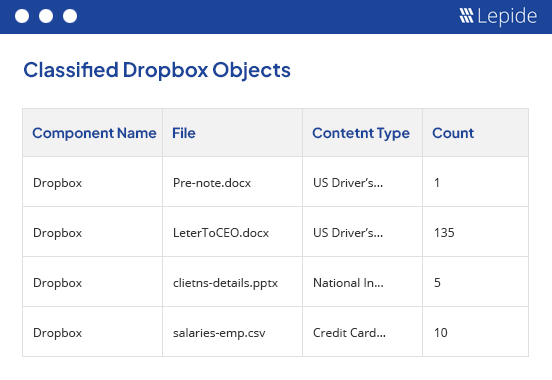
On-the-fly data discovery and classification helps you locate your most sensitive data as it is created or modified.
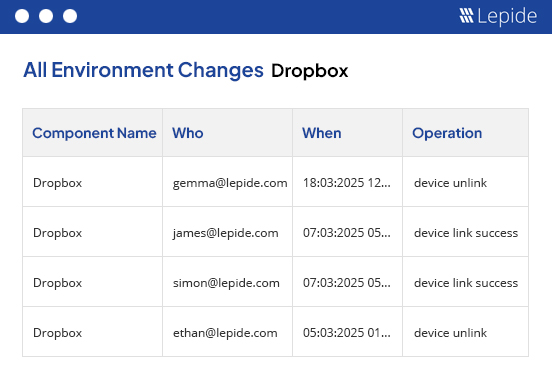
Get critical information about Dropbox link sharing, including who is sharing the links and when.
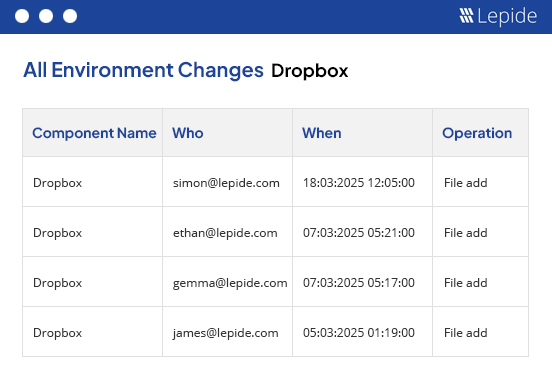
Advanced auditing, reporting, and alerting for all Dropbox file and folder copying, moving, modifying, deleting, and more.