How Lepide helps in the Microsoft Teams Auditing.
The collaboration that MS Teams provides creates unique security challenges that many solutions cannot cope with. Lepide enables you to get real visibility over how your users are engaging with Teams and when sensitive data is being shared, to help you respond to threats and prevent breaches.
Understand how your sensitive data Is being shared in Teams.
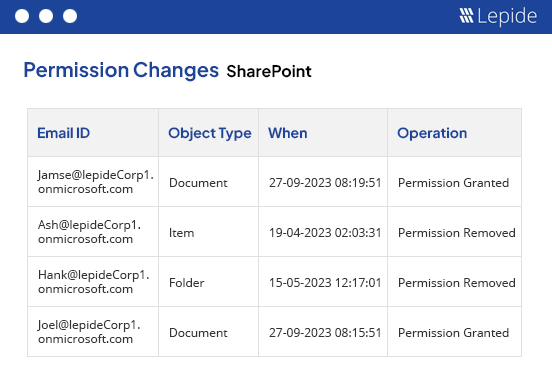
Whenever sensitive data is shared on Teams, you need to be able to see which users are now able to access that information and remediate access if required.
Get real time alerts when sensitive data is being shared via particular channels or directly in chats. Generate reports on which users now have access to that sensitive data and address excessive permissions.
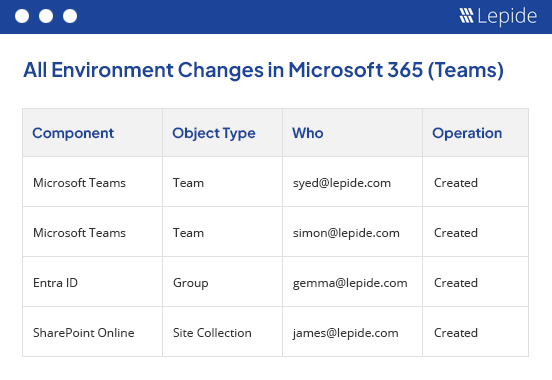
Uncover how your employees are using Teams.
Get real time information on how and when your users are accessing Microsoft Teams, including when sessions are started, when new teams are created, new channels are created, and more.
Receive this information in real time alerts or through pre-defined reports to detect and react to inappropriate usage faster.
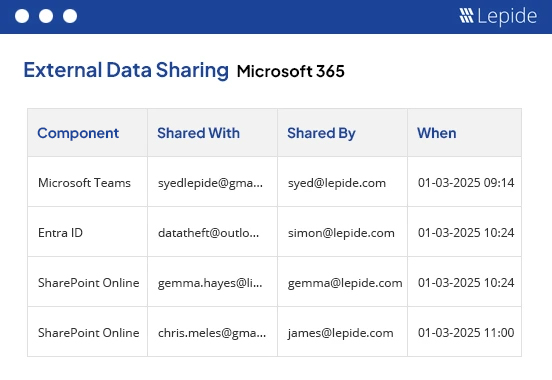
See when data is shared externally.
Lepide can now show you when data is being shared externally on MS Teams, whether through public/private channels or individual chats. This gives you the ability to identify and alert in real time when your most sensitive data is being shared outside your organization, helping you to detect incidents that could lead to potential data breaches.