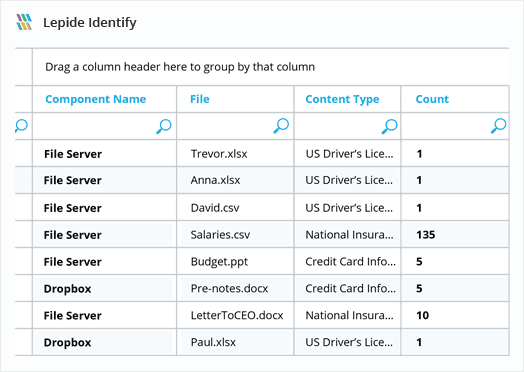
Data Classification Software
Get greater visibility over the content of your files with Lepide Data Classification Software. It automatically scans and classifies data related to PII, PHI, PCI, IP, and other regulations.
Fill in the rest of the form to
download the 20-day free trial
download the 20-day free trial
x