Group Policy Audit Reports
The predefined audit reports to cover every change made to Group Policy Objects at granular level in real time.














Whether your main driver is compliance, securing your IT environment or simply streamlining systems management, auditing Group Policy Objects is essential. Modifying Group Policies is the first step IT Administrators take when trying to configure the IT environment. Organizations should keep a record of which Group Policy was modified, when and by whom. However, the native method for generating Group Policy audit reports is complex and time consuming. Lepide Group Policy Auditor provides over 40 pre-defined reports for Group Policy Objects. With one click, a report for any duration can be generated, filtered or customized further.
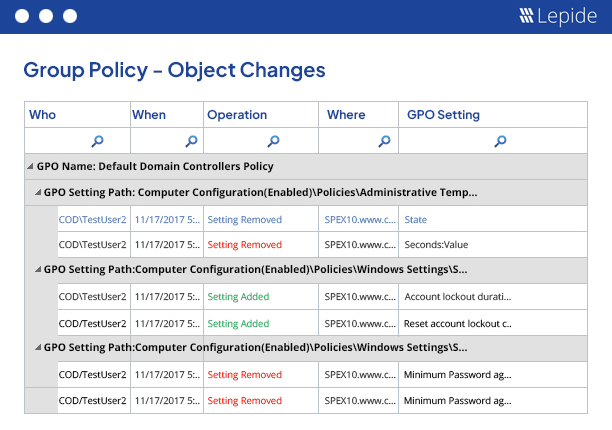
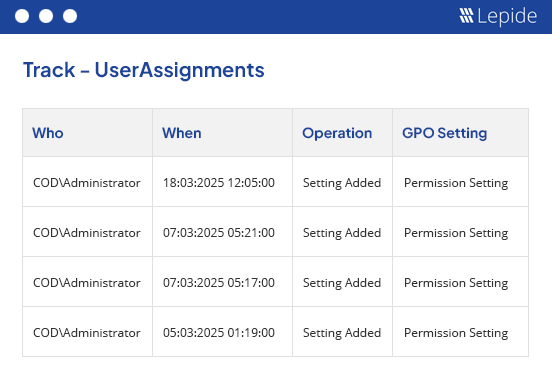
These reports come in handy when you are trying to track critical changes being made in a complex Group Policy environment. They provide you with details on each change made to any Group Policy. You can view the change, analyze it and customize the report as desired. Modification reports can be scheduled to be delivered either through email or by storing them at a shared location periodically.
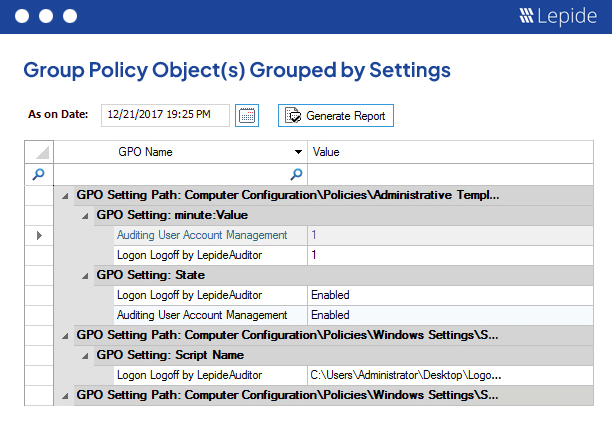
Lepide GPO Auditor captures snapshots of the state of Group Policy Objects automatically at pre-defined intervals. These snapshots can be used to completely restore the Group Policy Object at domain level or domain controller level. The solution also lets you generate state-in-time reports to check what the state of that particular Group Policy Object was at that time.
You can create a custom report by editing any of our existing Modification Reports to suit your requirements; tracking Administrative Template Policies, for example.
You can apply real-time and threshold alerts on both Group Policy Modification Reports and Custom Reports. These alerts can be delivered as an email to your inbox, as push notifications to Lepide Mobile App or as updates to LiveFeed widget located in the Radar Tab.
By following the guidelines outlined in this paper, your organization can establish a robust data access governance program that supports its business objectives and protects your valuable data assets.
Get the free guide now!