Data access governance platforms give companies visibility over who has access to sensitive information, helps them understand how access is being used, and enables them to implement the principle of least privilege.
This blog analyzes 7 of the best data access governance tools based on features, use cases, and deployment fit to help IT security and compliance teams select the best platform for their environment.
What is Data Access Governance?
Data Access Governance (DAG) refers to the term used to describe the combination of policies, procedures, and technological measures that decide and monitor who can use sensitive data within on-premises and cloud systems. Without data access governance, permissions can spiral, leading to insider threats and difficulty maintaining a secure, compliant security posture.
Data Access Governance Tools Comparison
The table below highlights key differences between the top data access governance platforms.
1. Lepide Data Security Platform
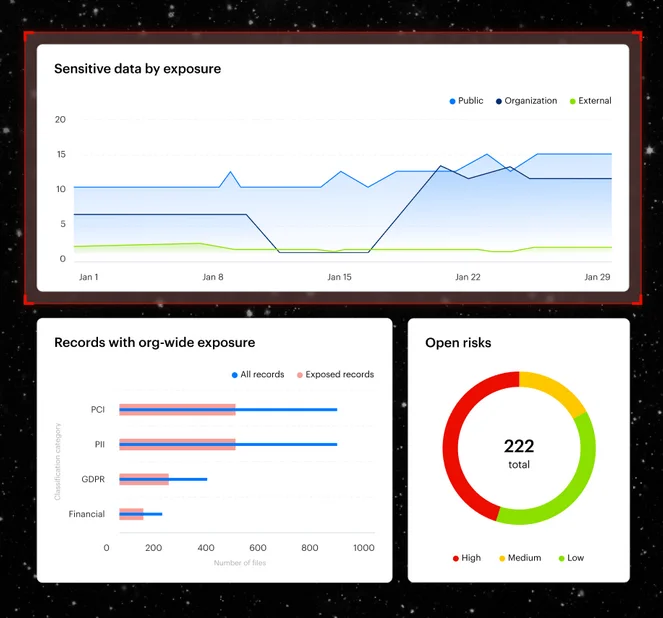
Lepide is a unified platform for directory and data security, with data access governance built into its core. It combines AI-driven behavioral monitoring, audit-ready compliance reporting, and granular permission auditing into a single, quickly deployable solution.
Key Features
- Discovers sensitive data across file servers, and Microsoft 365 with agent-based scanning.
- Real-time alerts detect risky permission changes, with automated rollback if needed.
- Supports owner‑driven access reviews, reducing workloads on IT and security teams.
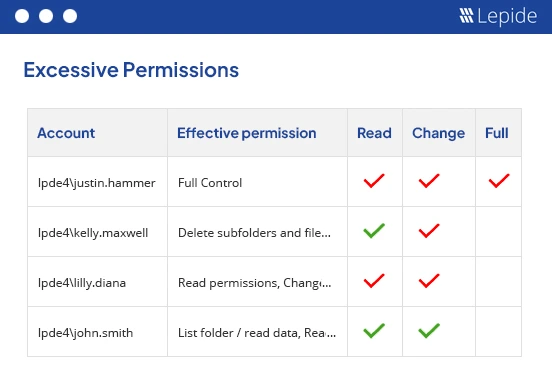
- Granular permission analysis to show true effective permissions – even in the case of complicated nested and inherited permissions.
- Unified visibility across Active Directory, file servers, and Microsoft 365.
- Generate reports related to audit- ready compliance mapped to HIPAA, GDPR, SOX frameworks.
Key Takeaways
- Unified Hybrid Coverage for Active Directory, file servers, Microsoft 365, and unstructured data.
- Cost-effective with strong ROI for mid-market and regulated enterprise sectors.
- AI-driven anomaly detection, continuous behavioral monitoring with automated response.
- Fast deployment that is operational in days and not months.
2. Varonis Data Security Platform
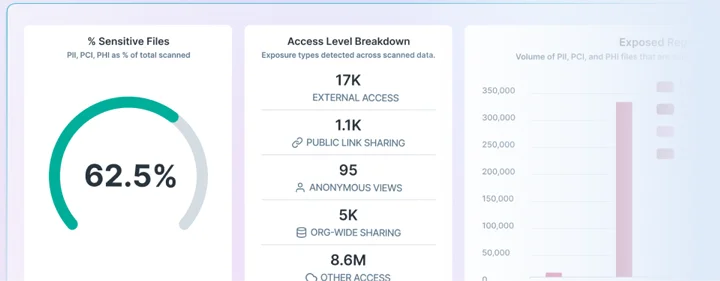
Varonis is an enterprise-level data security platform for both structured and unstructured data discovery, classification, and access control. Its technologies provide comprehensive reporting for compliance and audit requirements, automate authorization assessments, and correct excessive access.
Key Features
- Classification of data across structured and unstructured.
- Mapping the permissions deeply with full resolution of direct, inherited, and nested group access rights.
- Automate entitlement reviews to surface stale, excessive or misconfigured permissions.
- Analyze behavior continuously across files, emails, and Sharepoint.
- Compliance dashboards for GDPR, HIPAA, SOX, and PCI DSS.
- Detects insider threats and compromised accounts.
Key Takeaways
- Deep permission analytics that resolves complex nested access structures.
- Pre-built frameworks for major regulations proves to be compliance coverage.
- Best for large environments with high volume of unstructured data and complex permission changes.
- Behaviour monitoring with insider threat detection.
3. Netwrix Data Access Governance
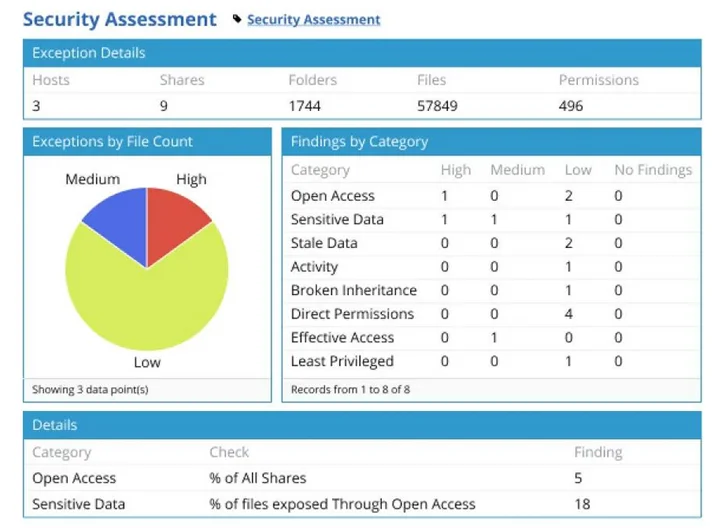
Netwrix focuses on change auditing, permission analysis, and compliance-ready reporting. It is well suited for Microsoft-centric IT environments.
Key Features
- Scans data stores and permissions across file servers and Microsoft 365.
- Implement dashboards that display overexposed sensitive data and excessive permissions.
- Analyze permissions and data stores on file servers, AD, and Microsoft 365.
- Generate compliance-ready reports using pre-made templates for PCI DSS, GDPR, SOX, and HIPAA.
- Correlate activity across user accounts, groups, and data objects.
Key Takeaways
- Hybrid coverage including on-premises Windows file servers.
- Compliance friendly templates for common frameworks.
- Strong Active Directory and Microsoft 365 focus with straightforward deployment and reporting.
- Ideal for Microsoft-focused companies looking for advanced, cross-cloud behavioral analytics that may require additional tools.
4. Forcepoint Data Security Cloud
Forcepoint Data Security Cloud delivers DAG through an integrated platform rather than a single product bringing real-time classification and cross-environment controls to govern access and usage of sensitive data.
Key Features
- AI-powered data discovery and classification.
- Classify and protect data in real-time with inline, cloud-native controls.
- Support zero-trust principles with granular access controls and continuous assessment.
- Deploy centralized coordination to establish uniform policies for SaaS, web, and private applications.
- Monitor data movement to detect and prevent exfiltration across cloud and endpoint channels.
Key Takeways
- Deep file-permission mapping might require pairing with a specialized DAG solution.
- Real‑time controls for modern, distributed workforces.
- Unified policy engine with consistent data handling across apps and channels.
- Risk‑adaptive with dynamic responses based on user and data context.
5. BigID Data Discovery and Governance
BigID is a privacy-led data discovery and governance platform that assists enterprises in enforcing least-privilege and identity data risk at scale by supporting privacy, compliance, and access monitoring.
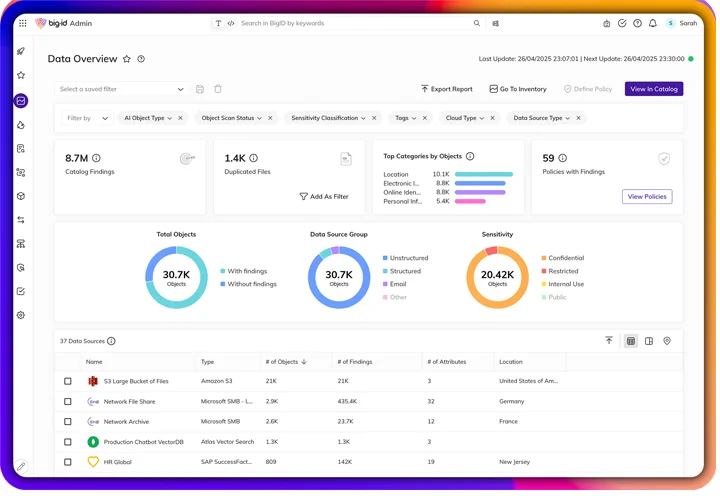
Key Features
- Advanced data discovery and classification of sensitive data across structure and unstructured data.
- Enable policy-based controls to guide least-privilege access decisions.
- Strong privacy and compliance features.
- Integrations with cloud and SaaS platforms.
- Prioritize remediation by identifying high-risk data locations and overexposure.
Key Takeaways
- DSAR automation and consent alignment streamline compliance.
- High‑fidelity detection of sensitive data across the estate.
- Better ownership and context for access decisions.
6. Securiti AI-Driven Data Governance
Securiti offers an AI-driven data governance platform across multi-cloud environments, combining discovery, consent, and access intelligence to automate least-privilege and compliance. It basically governs how users and AI systems access sensitive data.
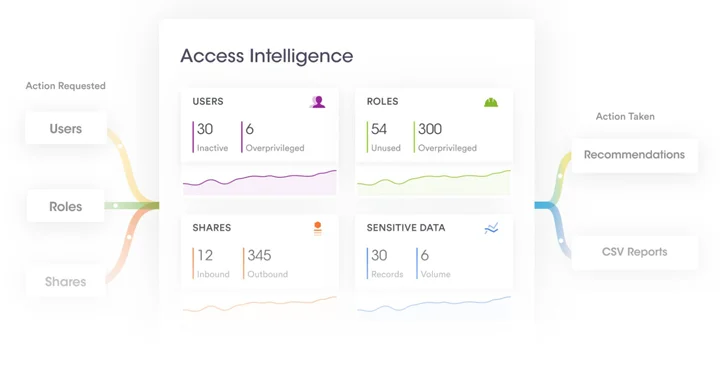
Key Features
- Discover sensitive data across IaaS, PaaS, SaaS, and on-premises.
- Recommend least-privilege with AI-assisted policies and review workflows.
- Unified data intelligence for privacy and security with centralized dashboards.
- Analyze entitlements to identify overexposure and orchestrate remediation.
Key Takeaways
- AI-assisted Least privilege with faster remediation and review cycles.
- Multi-cloud coverage having consistent governance across diverse platforms.
- Integrated workflows from discovery to enforcement.
7. Concentric AI Entitlement Analysis
Concentric AI uses machine learning to identify and protect sensitive data across cloud and collaboration tools and focuses on rapid entitlement analysis for unstructured data to detect overexposure.
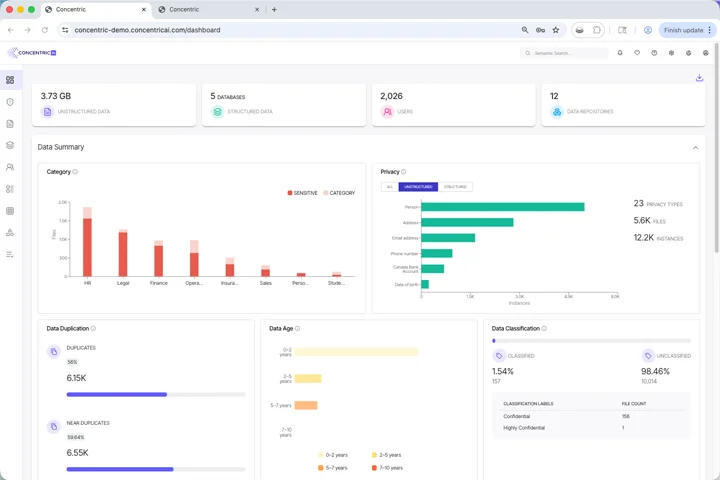
Key Features
- AI-driven content and contextual analysis.
- Automatic access recommendations.
- Accelerate reviews with prioritized insights and actionable reports.
- Analyze entitlements quickly across repositories – cloud drives and collaboration suites.
Key Takeaways
- Lightweight and scalable AI approach.
- AI-powered insights into data risk exposure.
- Finds risky sharing and permission drift.
Main Features of Data Access Governance Tools
An effective data access governance tools connects with the main features which are discussed below:
- Data Classification: The sensitive data discovery and classification across structured and unstructured data.
- Effective Permission Analysis: This includes nested groups and inheritance with access controls to ensure users only access what’s necessary for their roles.
- Compliance and Policy Enforcement: The compliance enforcement ensures data handling aligns with frameworks by applying consistent policies across environments.
- Remediation Automation: It is basically done to remove stale/ excess privileges.
- Real-time Alerting: The real-time alerting is mainly done on risky permission changes.
- Deployment Flexibility: The deployment flexibility is across on-premises, cloud, and hybrid models.
- Visibility: To identify possible insider or external risks, the risk insights offer ongoing visibility into data exposure and anomalous access behaviors.
Why Lepide is the Best Data Access Governance Platform for Your Business
Unlike many Data Access Governance (DAG) solutions that focus purely on data discovery or classification, Lepide takes a more practical approach by combining identity and data security into a single platform. Because access risk doesn’t exist in isolation, Lepide starts with Active Directory and Entra ID, where permissions are actually defined and connects that to the data those identities can access across file servers and Microsoft 365. This unified view makes it far easier to answer the questions that matter: who has access to sensitive data, how they got that access, and whether it’s appropriate. Instead of fragmented insights, you get clear, actionable visibility that reflects how environments actually operate.
Lepide also stands out for its ability to turn visibility into action quickly. Many DAG tools require significant time, expertise, and cost before delivering value, often overwhelming teams with complex dashboards and manual processes. Lepide is designed to be simple, fast to deploy, and easy to use, helping IT and security teams identify over-permissioned users, clean up access, and enforce least privilege without heavy lifting. With built-in auditing, real-time alerting, and automated remediation, organizations can reduce risk in days, not months, making Lepide a strong choice for mid-sized organizations that need enterprise-grade data security without the overhead.
Frequently Asked Questions
DAG governs data‑layer entitlements (for example, NTFS, SharePoint, OneDrive, Microsoft 365, cloud drives) and answers “who can access which data and why.” IAM manages identities, authentication, and coarse‑grained application access. In practice, the tools in this guide integrate with IAM so identity changes flow to data permissions: Lepide and Netwrix align tightly with Active Directory/Azure AD; Varonis maps effective permissions across file systems and Microsoft repositories; Securiti and BigID map identities to data across multi‑cloud; Forcepoint enforces real‑time usage policies; Concentric focuses on data‑sharing entitlements in cloud collaboration suites.
Match a vendor to your primary use case and estate: Lepide for hybrid, Microsoft‑centric environments needing fast deployment, unified permission auditing, and behavioral analytics; Varonis for large enterprises requiring deep unstructured‑data permission mapping and automated remediation at scale; Netwrix for Microsoft‑focused auditing and compliance reporting; Forcepoint for cloud‑first, real‑time policy enforcement and DLP; BigID for privacy‑led discovery, classification, and DSAR automation to inform access decisions; Securiti for AI‑driven, multi‑cloud discovery, consent, and entitlement governance; Concentric AI for rapid entitlement analysis and overexposure cleanup in cloud collaboration platforms.
Typical timelines by vendor/use case: Lepide and Concentric AI often deliver actionable visibility in days; Netwrix commonly deploys in days to a few weeks depending on scope; Forcepoint rollouts are typically staged over weeks to align policies across SaaS, web, and private apps; BigID and Securiti discovery/cataloging usually complete initial passes in weeks, with ongoing tuning; Varonis enterprise deployments can take weeks to months for large, complex file systems and automated remediation programs.
Most support agentless collection with optional agents/sensors where real‑time auditing is required. Lepide offers fast, agent‑based scanning with agentless options for certain sources; Netwrix supports agentless discovery and optional agents for deeper auditing; Varonis uses collectors/sensors depending on the repository; Forcepoint is cloud‑native and relies on endpoint agents/browser controls for DLP and policy enforcement; BigID and Securiti primarily use connectors/APIs across cloud and on‑prem sources; Concentric AI is largely API/connector‑driven for cloud and collaboration platforms.
Yes, with varying levels of automation and owner approval. Varonis provides automated remediation at scale; Lepide recommends and can execute permission changes with approval workflows; Securiti uses AI‑assisted least‑privilege recommendations and orchestrated remediation; Netwrix supports scheduled attestations and workflow‑driven cleanup; Concentric AI guides owners with recommended fixes for overexposed data; Forcepoint focuses on policy enforcement and DLP rather than file‑system permission changes. Best practice is to require data‑owner approval and test changes in phases.
Coverage varies. BigID and Securiti offer broad connectors for structured data (databases, data warehouses) alongside unstructured sources; Varonis primarily excels with unstructured repositories but offers classification across some structured stores; Lepide and Netwrix focus on unstructured data, Active Directory, and Microsoft 365; Forcepoint governs usage via policy controls rather than database‑level entitlements; Concentric AI concentrates on unstructured and collaboration data. Verify connectors for your specific databases before selection.



