Last Updated on May 22, 2026 by Satyendra
What is a Network Device?
In simple terms, a network device is a physical device that is used to connect other physical devices on a network. In some cases, their role is to simply forward packets of information to a destination. In other cases, it might be to serve as a translator or to block suspicious network traffic.
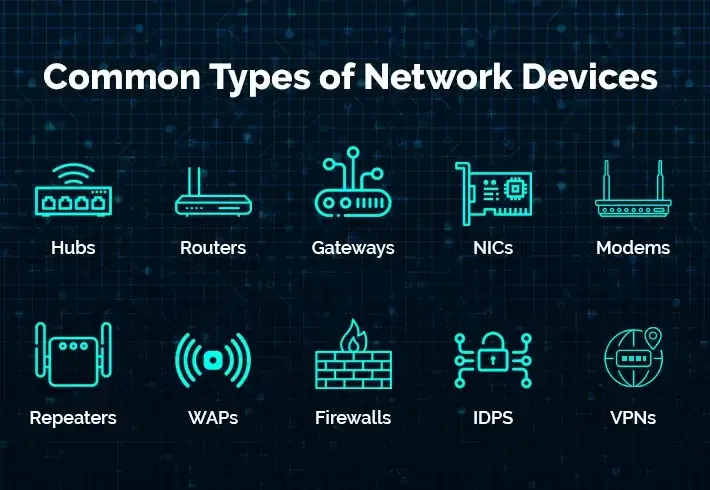
Common Types of Networking Devices and their Uses
Network devices serve as intermediaries, facilitating the transmission of data between other devices, and thus play a vital role in the functioning of a computer network. Below are some of the most common devices used in modern networks:
| Device | Primary Function | OSI Layer |
|---|---|---|
| Bridge | Connects multiple network segments into a single network | Layer 2 (Data Link) |
| Hub | Connects multiple devices by broadcasting signals to all ports | Layer 1 (Physical) |
| Router | Directs traffic between networks using IP addresses | Layer 3 (Network) |
| Gateway | Translates data between different network protocols | Layer 3+ (Network/Application) |
| NIC | Enables a computer to connect to and communicate on a network | Layer 1-2 (Physical/Data Link) |
| Modem | Converts digital data to analog signals for transmission | Layer 1 (Physical) |
| Repeater | Amplifies and rebroadcasts signals to extend network reach | Layer 1 (Physical) |
| WAP | Enables wireless devices to connect to a wired network | Layer 1-2 (Physical/Data Link) |
| Firewall | Monitors and controls network traffic based on security rules | Layer 3-7 (Network/Application) |
| IDPS | Detects and prevents network intrusions and threats | Layer 3-7 (Network/Application) |
1. Bridges: How They Connect Network Segments
Definition: A network bridge is a device that enables multiple communication networks or network segments to be combined into a single, unified network. This process is referred to as network bridging, which is distinct from routing.
While routing allows multiple networks to communicate independently while remaining separate, bridging connects two separate networks as if they were a single entity. In the Open Systems Interconnection (OSI) model, bridging occurs at the data link layer (layer 2) and is used to connect disparate networks.
When one or more of these segments are wireless, the device is considered a wireless bridge. There are several types of network bridging technologies, including simple bridging, multiport bridging, and learning or transparent bridging.
There are two models in which bridges can be set up in:
- Local bridging: where LAN connections are made using local cables.
- Remote bridging: where two connections are brought together with a wide area network (WAN).
2. Hubs: How They Broadcast Signals Across Ports
Definition: A hub, also known as an active hub or repeater hub, is a network device that connects multiple computer networking devices together, creating a single network segment. It has multiple input/output ports, where a signal introduced at any port is echoed to every other port except the original incoming port.
Operating at the physical layer, a hub works by amplifying and retransmitting incoming signals. Some hubs may also include additional connectors such as BNC or AUI, allowing connection to legacy 10BASE2 or 10BASE5 network segments.
However, hubs are now largely obsolete, having been replaced by network switches in most cases, except in older or specialized installations. In fact, the use of repeaters or hubs to connect network segments is deprecated by the IEEE 802.3 standard, as of 2011.
Hubs come in two types:
- Simple hubs: only one port for connecting a device to other networks.
- Multiple-port hubs: where users can connect to many devices, some of which expand in a modular fashion.
3. Routers: How They Direct Traffic Between Networks
Definition: Routers are devices that connect multiple packet-switched networks or subnetworks, performing two primary functions: managing traffic between networks by forwarding data packets to their intended IP addresses, and allowing multiple devices to share the same internet connection.
Typically, most routers serve as a bridge between local area networks (LANs) and wide area networks (WANs). A LAN is a group of connected devices restricted to a specific geographic area, typically requiring a single router.
On the other hand, a WAN is a large network spanning a vast geographic area, often requiring multiple routers and switches due to its distributed nature. Examples of WANs include large organizations and companies with multiple locations across the country, which require separate LANs for each location to form a cohesive network.
Routers can actually be configured as either static or dynamic:
- Static routers: have to be configured manually and will remain static until altered.
- Dynamic routers: will use data from nearby routers to inform their own routing tables.
4. Gateways: How They Translate Data Between Networks
Definition: A gateway is a device that serves as a connection between networks, translating data to enable communication between different network protocols.
Historically, gateways and routers have been separate devices, but it’s becoming more common for them to be combined into a single router. For example, home Wi-Fi routers can act as both a router and a gateway, delivering data within the network while translating it for devices on the receiving end.
A network gateway typically consists of physical components, such as Network Interface Cards (NICs) and inputs and outputs, as well as software for translating network protocols and providing gateway functions. These functions can be defined, deployed, and controlled through software, and may also be built into other devices, such as routers.
Gateways can be deployed on various layers of the OSI model, but are typically used on the network layer. They can be used in various security processes, including as a firewall or proxy server to scan and filter data, and can be used in either a unidirectional or bidirectional manner, allowing data to flow in only one direction or in both directions.
5. NICs (Network Interface Cards): How Network Interface Cards Enable Device Connectivity
Definition: A Network Interface Card (NIC), also known as an Ethernet card, LAN card, or network adaptor, is a piece of hardware that enables computers to communicate with other devices on a network. It provides a dedicated connection to the network and contains the necessary circuits to translate digital data into signals used to transfer data, such as Ethernet or Wi-Fi.
The NIC represents the computer on the network and is identified by its unique Media Access Control (MAC) address. When a user browses the internet, the NIC acts as a go-between for the computer and the network, converting digital requests to electrical signals and transmitting them to the network.
There are two types of NIC:
- Ethernet NICs: use an 8P8C socket for connecting to ethernet cables.
- WiFi NICs: connect directly to a wireless network.
The process works as follows: the computer sends a request to the NIC, which converts the request to electrical signals that travel through the internet to the web server’s network card, where the signals are translated back into data that is processed by the server. When the web server responds with a web page, the process happens again in reverse. The connection between the software on the computer and the NIC is handled by a driver, loaded into the computer’s memory and remaining resident while running. The operating system’s kernel delegates access to the driver by applications that need to connect.
6. Modems: How They Convert Digital Signals for Transmission
Definition: A modem is a crucial piece of computer hardware that converts digital data into a format suitable for transmission over analog mediums, such as phone lines or radio waves. This process involves modulating one or more carrier wave signals to encode the digital information, which is then transmitted over the medium.
The receiver, on the other hand, demodulates the received signal to recreate the original digital information. The ultimate goal of a modem is to produce a signal that can be transmitted efficiently and decoded reliably, regardless of the analog medium being used. In fact, modems can be used with a wide range of analog transmission methods, including light-emitting diodes, radio, and much more.
Modems come in three different types:
- DSL modems: often considered the slowest as they use telephone cables.
- Cable modems: faster than DSL because they transmit data over TV lines.
- Wireless modems: the fastest type of transmitter as it transfers information between the local network and an internet service provider (ISP).
7. Repeaters: How They Extend Network Signal Range
Definition: A repeater is a network device responsible for amplifying and rebroadcasting incoming signals to extend their reach and make them more usable.
Repeaters are used to increase the network’s reach, restore damaged or weak signals, and provide access to nodes that are otherwise inaccessible. They operate by magnifying the received signal to a higher frequency domain, making it more scalable, accessible, and suitable for transmission.
In wired data communication networks, repeaters are employed to extend signal propagation, while in wireless networks, they are used to expand cell size. Additionally, repeaters support a range of transmission types, including analog, digital, and light-based transmissions, making them a versatile and essential component of modern network infrastructure.
8. WAPs (Wireless Access Points): How Wireless Access Points Enable Wi-Fi Connectivity
Definition: A Wireless Access Point (WAP) is a networking device that enables wireless-capable devices to connect to a wired network.
Unlike traditional wired connections, WAPs are simple and easy to install, making it a convenient option for connecting all computers and devices in your network.
There are several reasons to use a WAP to set up a wireless network. For instance, it allows you to create a wireless network within your existing wired network, accommodating wireless devices and enhancing your overall network capability.
Additionally, WAPs or mesh extenders can be used to extend the signal range and strength of your wireless network, effectively eliminating “dead spots” and providing complete wireless coverage, which is particularly beneficial in larger office spaces or buildings. Furthermore, WAPs can be configured using a single device, making it a seamless and efficient process.
WAPs can be:
- Fat APs: or occasionally referred to as autonomous APs. These have to be configured manually with network and security settings.
- Thin APs: these allow for remote configurations using controllers. Being not manually configured means that they can be easily reconfigured and monitored.
9. Firewalls: How They Protect Networks from Unauthorized Access
Definition: A firewall is a critical network security device that acts as a sentinel, monitoring and controlling all incoming and outgoing network traffic to ensure that only authorized traffic is allowed to pass through.
Firewalls have been a crucial first line of defense in network security, serving as a barrier between trusted, internal networks and untrusted outside networks, such as the internet. Firewalls can take various forms, including hardware-based solutions, software-based solutions, and cloud-based options, which can be categorized as Software-as-a-Service (SaaS), public cloud, or private cloud (virtual).
10. IDPS: How Intrusion Detection and Prevention Systems Stop Threats
Definition: An Intrusion Detection and Prevention System (IDPS) is a critical component of network security that monitors traffic to identify and stop potential threats.
Intrusion Detection Systems (IDS) involve monitoring network traffic to identify potential threats, such as exploit attempts or imminent incidents that may compromise the network.
Intrusion Prevention Systems (IPS), on the other hand, take it a step further by not only detecting these incidents but also stopping them by dropping packets or terminating sessions. These functionalities are also integrated into Next-Generation Firewalls (NGFW), providing an additional layer of protection.
Conclusion
Securing network devices is just one piece of the puzzle. The attack surface has drastically changed over the last 5 years, with internal threats targeting Active Directory and working their way through to sensitive data stored on-premises or in cloud data stores. Schedule a demo to see how Lepide can help you start your data and identity security journey today.
Related Articles:
Frequently Asked Questions
A hub broadcasts data to all connected ports regardless of the destination, while a switch intelligently directs data only to the specific port where the destination device is connected, making switches more efficient and secure.
Use a router when connecting networks that use the same protocol (like two IP networks), and use a gateway when you need to translate between different network protocols or architectures.
A bridge connects network segments at Layer 2 (data link) using MAC addresses and treats them as one network, while a router connects separate networks at Layer 3 (network) using IP addresses and keeps them distinct.
Yes, if connecting to the internet—the modem converts signals from your ISP, while the router distributes the connection to multiple devices; however, many ISPs now provide combination modem-router devices.



