Last Updated on May 4, 2026 by Satyendra
User access reviews are one of those things every organization knows it should do, but almost nobody enjoys doing. The reason is simple. Manual access reviews are painful. Teams export permissions into spreadsheets, send approval emails, chase managers for confirmations, and then scramble to produce evidence when auditors show up.
User Access Review (UAR) software fixes that problem by automating access certification, identifying excessive permissions, and maintaining a verifiable audit trail. These platforms help organizations enforce least privilege, reduce insider threat risk, and stay compliant with regulations like SOX, HIPAA, GDPR, and SOC 2.
How to Choose the Best User Access Review Tool for Your Business
Reviewers are often asked to approve access they don’t fully understand, so decisions become routine instead of thoughtful. Over time, permissions pile up and risk quietly increases. The right tool brings clarity, context, and focus back into the process. It helps teams make decisions that actually reduce exposure, not just complete reviews.
- Best for organizations that need broad access coverage: If a tool cannot see the systems your users actually interact with, it becomes little more than an expensive guessing machine. Access review platforms should integrate with identity sources such as Active Directory, Microsoft Entra ID, SaaS applications, databases, cloud platforms, and on-premises systems. Reviews are only meaningful when they cover the full identity surface of the organization rather than a limited subset of systems.
- Best for teams that need clear visibility into user entitlements: Access reviews often fail because reviewers are asked to approve permissions they do not fully understand. Effective tools provide clear mapping between users, groups, roles, and the resources those permissions affect. This visibility helps reviewers understand what access actually enables a user to do, allowing them to make informed decisions instead of approving access blindly.
- Best for organizations that prioritize risk-aware access decisions: A strong user access review platform should highlight risky permissions and privileged access rather than presenting a flat list of entitlements. Features such as risk scoring, detection of dormant accounts, segregation-of-duties conflicts, and identification of toxic permission combinations allow security teams to focus on the access relationships that pose the greatest risk.
- Best for businesses that require flexible review workflows: Different organizations structure access reviews differently. Some rely on managers, while others involve application owners, compliance teams, or data owners. The best platforms support multiple review models, customizable review schedules, escalation rules, and automated routing to ensure the right stakeholders evaluate the access they understand best.
- Best for compliance-driven environments that require audit evidence: User access reviews are often performed to meet regulatory obligations such as SOX, HIPAA, PCI DSS, or ISO 27001. The platform should therefore provide detailed reporting that shows who reviewed access, when decisions were made, and what remediation actions followed. Clear documentation ensures organizations can demonstrate compliance during audits.
- Best for organizations with specific deployment requirements: Identity environments vary widely across organizations. Some rely entirely on cloud infrastructure, while others operate hybrid or fully on-premises environments. Selecting a tool that supports the organization’s deployment model ensures the platform can scale with evolving infrastructure without requiring significant architectural changes.
Quick Comparison of the Top User Access Review Tools
Before exploring each platform in detail, the table below provides a quick side-by-side comparison of the leading user access review tools. It highlights their ideal use cases, deployment models, strengths, and potential limitations to help security and IT teams quickly narrow down the solutions that best fit their environment.
| Tool | Best For | Deployment | Core Strength | Limitation |
|---|---|---|---|---|
| Lepide Data Security Platform | Mid-sized organizations that need visibility into permissions and sensitive data | Hybrid (on-prem + cloud data sources) | Deep permissions visibility and risk context | Focused more on data access governance than full IGA |
| Microsoft Entra ID Governance | Microsoft-centric organizations | Cloud (SaaS within Microsoft Entra / Azure) | Native governance for Microsoft ecosystem | Limited value outside Microsoft identity stack |
| SailPoint Identity Security Cloud | Large enterprises with mature IAM programs | Cloud (SaaS) and On-prem option via IdentityIQ | Deep certification and governance at scale | Can be heavy for smaller teams |
| One Identity Manager | Complex enterprises with formal governance needs | Hybrid (on-prem and cloud environments) | Strong attestation and SoD support | More suited to mature programs than lightweight teams |
| Saviynt Identity Cloud | Cloud-heavy enterprises and converged identity programs | Cloud-native (SaaS) | Broad identity governance, including non-human identities | More platform than point solution |
| Okta Identity Governance | Okta-centered environments | Cloud (SaaS) | Clean reviewer experience and access certification in Okta | Strongest when Okta is the identity hub |
| Netwrix Directory Management | Organizations needing directory-focused visibility and reporting | On-prem and Hybrid | Reporting-heavy access review and compliance support | Less expensive than full IGA suites |
Top 7 User Access Review Platforms
Below are seven of the most widely used user access review tools that help security and IT teams automate access governance and eliminate risky permission sprawl.
1. Lepide Data Security Platform
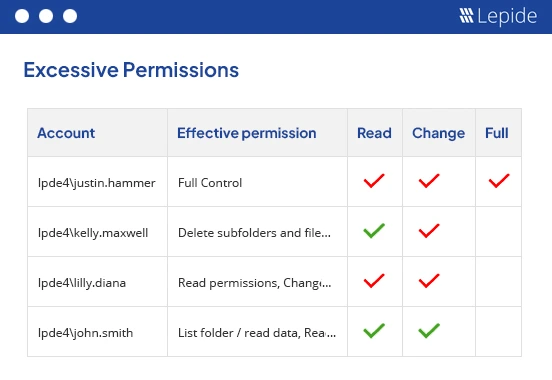
Lepide Data Security Platform is a strong fit for mid-sized organizations that want user access reviews to be practical, auditable, and tied to real permissions risk. Lepide describes its platform as helping with user access reviews by identifying users with excessive permissions, monitoring for anomalous behavior, and producing reports that help teams act quickly.
Where Lepide stands out is in the context. Instead of treating reviews like a box-ticking exercise, it helps teams understand who has risky access and why that access matters. Lepide also emphasizes continuous entitlement review practices, which makes it a good option for organizations that want review and cleanup to be part of normal operations, not an annual panic ritual.
Key Features
- Automated user access review support
- Detection of excessive and risky permissions
- Continuous entitlement review practices
- Alerts and reports for suspicious access behavior
- Strong fit for hybrid environments with identity and file access concerns
2. Microsoft Entra ID Governance
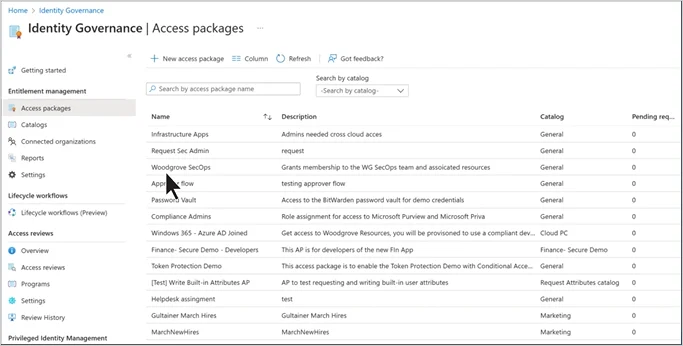
Microsoft Entra ID Governance includes native access reviews for groups, applications, Azure resources, and Microsoft Entra roles. Microsoft documents recurring review schedules, reviewer notifications, and the ability for reviewers to approve or deny access using a built-in interface.
This is the obvious choice for organizations already standardized on Microsoft 365 and Entra ID. It is especially useful for group membership and guest access reviews, and Microsoft also supports review recommendations to help decision-makers make faster calls.
Key Features
- Reviews for groups, applications, and roles
- Recurring review campaigns
- Reviewer notifications and recommendations
- Guest access review support
- Built-in approval and denial workflow
- Auto-remediation options for access changes
3. SailPoint Identity Security Cloud
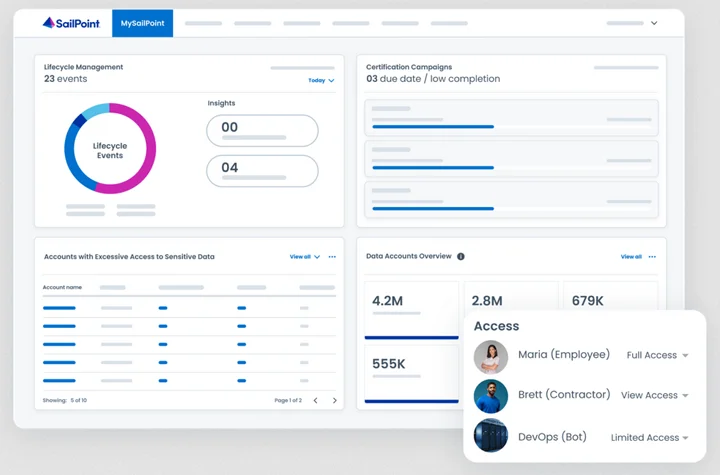
SailPoint Identity Security Cloud offers access certification across data center, cloud, and mobile systems. SailPoint says certifiers can review users’ access to roles, access profiles, entitlements, and apps, and use AI-generated recommendations to decide whether access should stay or go.
This is a mature enterprise option for organizations with complex IAM programs and lots of business applications. It is built for structured certification campaigns, policy control, and audit support at scale.
Key Features
- Access certifications across cloud and on-prem systems
- Review of roles, access profiles, entitlements, and apps
- AI-generated review recommendations
- Certification campaigns for managers and system owners
- Compliance reporting for auditors
- Risk-aware governance workflows
4. One Identity Manager
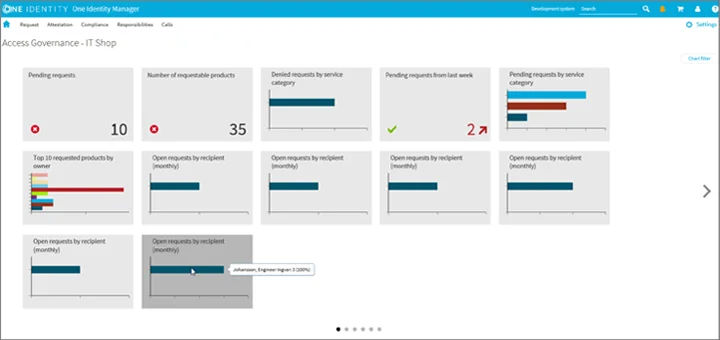
One Identity Manager supports identity and access attestation, letting managers or compliance owners certify entitlements, requests, or exception approvals on a scheduled or on-demand basis. The product is positioned to govern and secure users and data across on-premises, hybrid, and cloud environments.
It is a strong enterprise choice for organizations that need formal certification workflows, recertification, and integration into broader IAM and compliance operations. One Identity also documents access certification campaigns and segregation of duties rule management, which reinforces its fit for complex environments.
Key Features
- Attestation and recertification workflows
- Scheduled or on-demand certification campaigns
- Review of entitlements, requests, and exception approvals
- Risk-aware attestation support
- Hybrid deployment coverage
- SoD rule handling
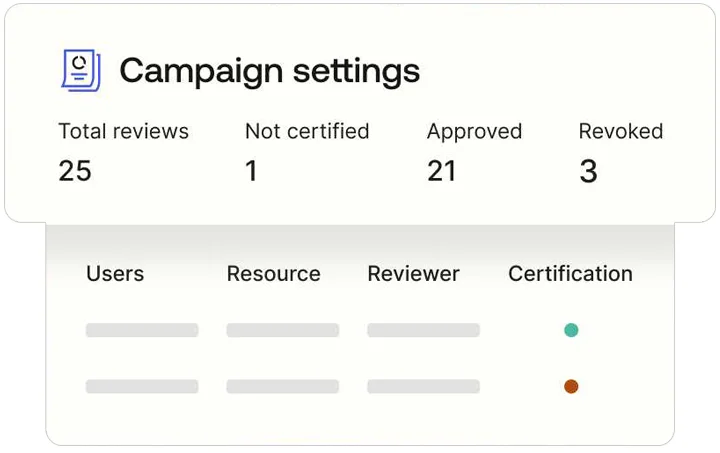
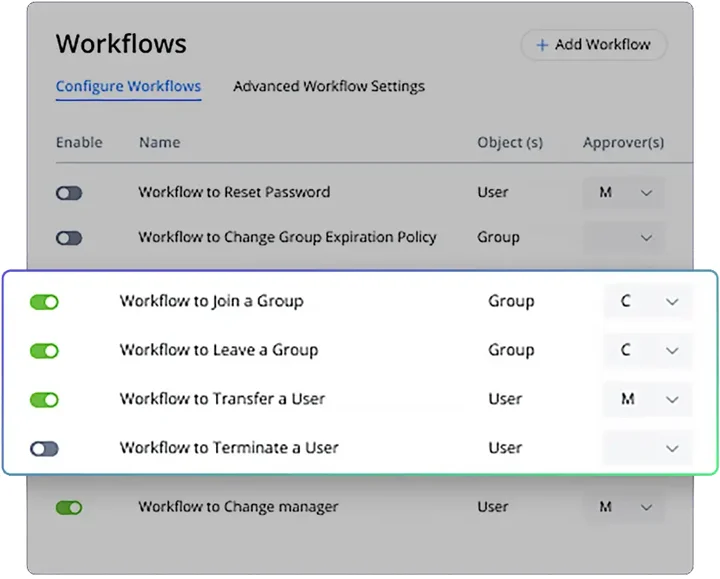
5. Saviynt Identity Cloud
Saviynt Identity Cloud is a converged identity platform that includes identity governance and access certification capabilities. Saviynt says its platform governs all identities, including non-human identities, and its certification materials describe access review and attestation capabilities as part of the core offering.
Saviynt also emphasizes intelligent certifications and access review workflows designed to help managers and resource owners make faster decisions while maintaining least privilege. That makes it a credible option for cloud-heavy enterprises that want access reviews tied to broader identity control.
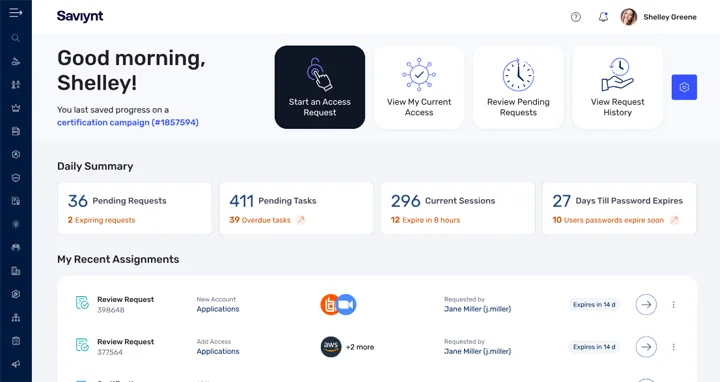
Key Features
- Identity access certifications and attestation
- Access reviews across cloud and enterprise apps
- Least-privilege support
- Risk and intelligence-driven review assistance
- Coverage for human and non-human identities
- Broad identity governance platform capabilities
6. Okta Identity Governance
Okta Identity Governance supports user access reviews and access certification campaigns for groups and applications in the Okta environment. Okta’s documentation says security access reviews provide a unified view of user access, help identify over-privilege, and let teams act without needing to drag the help desk into every decision. Human progress, at last.
This is a natural fit for organizations already standardized on Okta for workforce identity and lifecycle processes. It works best when the app landscape is centered on Okta-connected resources.
Key Features
- Access review campaigns for groups and applications
- Security access reviews with unified access view
- AI-generated summaries for reviewers
- Workflow support through Okta Identity Governance
- Good fit for Okta-centered environments
- Streamlined reviewer experience
7. Netwrix Directory Management
Netwrix Directory Management includes access review and compliance capabilities that help organizations automate access reviews, route decisions to the right owners, and produce audit-ready reports. Netwrix says it gives teams visibility into who has access, why they have it, and when it expires.
Netwrix is especially useful for teams that want strong reporting and visibility around directory and infrastructure access, even if they are not running a full-scale IGA program. Its reporting and compliance focus make it practical for periodic access review processes.
Key Features
- Automated access reviews
- Owner-based review routing
- Audit-ready reporting
- Least-privilege support
- Visibility into directory access
- Compliance-oriented dashboards and reports
Conclusion
The best user access review tool is the one that fits your identity environment, your review model, your compliance obligations, and your ability to actually operate it without turning your team into part-time spreadsheet janitors. The attached draft makes that point clearly by emphasizing coverage, visibility, workflow flexibility, automation, reporting, and deployment fit as the real decision criteria.
If you are Microsoft-heavy, Entra ID Governance is the obvious native route. If you need a deeper permissions context, Lepide stands out. If you need enterprise-grade identity governance at scale, SailPoint, Saviynt, and One Identity are the heavy-duty choices. If your world runs on Okta, use the tool that belongs to that ecosystem. If your priority is reporting and directory control, Netwrix is practical and focused. That is the real shortlist, not the glossy one.
Frequently Asked Questions
It is software that automates the process of collecting access data, routing review tasks, capturing approval or denial decisions, and producing audit-ready evidence for compliance and governance programs.
That depends on your risk and regulatory requirements. Microsoft supports weekly, monthly, quarterly, or annual recurring reviews, and many organizations use quarterly reviews for privileged or sensitive access.
Lepide’s definition is useful here. A user entitlement review is broader and examines a user’s access rights across resources, while a user access review is narrower and focuses on access to a specific system or resource.
Because manual review cycles are slow, repetitive, and easy to rubber-stamp. Automation helps teams keep reviews consistent, produce clearer evidence, and reduce privilege creep before it becomes a security problem.
Lepide is a strong fit when the goal is to combine access review workflows with deeper visibility into excessive permissions and risky access patterns, especially in hybrid environments.
It helps identify excessive or outdated permissions, reduces privilege creep, and makes it easier to revoke access that no longer belongs there. That lowers the chance that a stale account or over-provisioned user becomes a security problem.
Because service accounts, bots, API keys, and machine identities can hold powerful access too, and many legacy review processes barely account for them. Veza calls out NHI governance as a core part of modern identity security, which is a pretty strong hint that the rest of the market should stop ignoring it.


