Last Updated on May 12, 2026 by Satyendra
Organizations store sensitive data across file servers, cloud platforms, and collaboration tools like Microsoft 365. Understanding where that data lives is important, but security teams also need visibility into who can access it and how that access is being used.
Many security tools focus on discovering and classifying data (DSPM) or enforcing policies to prevent data loss (DLP). While these capabilities are valuable, they often provide limited insight into how users interact with sensitive data across directories, file systems, and shared environments. Without that context, it becomes harder to detect insider threats, excessive permissions, or unusual access patterns.
This is why many organizations rely on dedicated data access monitoring platforms. These tools provide visibility into permissions, user activity, and access behavior across hybrid environments. Platforms like Lepide are often preferred in these scenarios because they bring together access monitoring, permissions visibility, and behavior analytics in a single view.
How to Choose the Best Sensitive Data Access Monitoring Platform
Choosing the right platform for sensitive data access monitoring depends on how your organization identifies, monitors, and controls access to sensitive data. While many tools claim to “protect sensitive data,” they take very different approaches, ranging from data discovery and classification (DSPM), to policy enforcement (DLP), to real-time monitoring of user activity and permissions. Understanding these differences is key to selecting the right solution.
Best for detecting insider threats and risky behavior
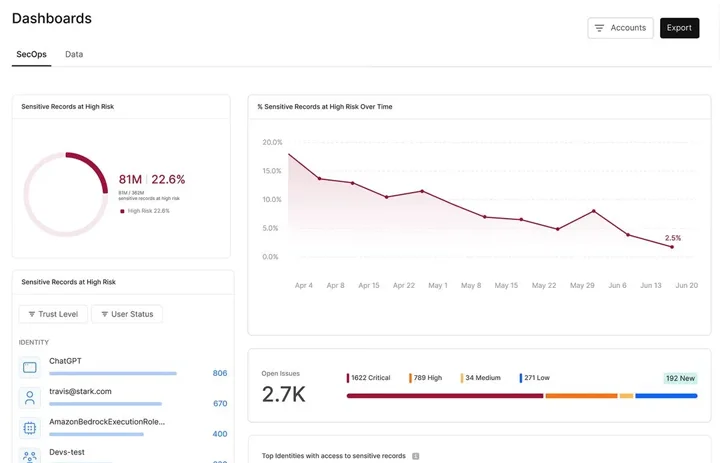
For organizations concerned about insider threats, the priority is understanding how users interact with sensitive data in real time. This includes detecting behaviors such as unusual file access, mass downloads, or activity outside normal patterns. Platforms that combine access monitoring with behavior analytics are typically preferred, as they provide visibility into both what users are doing and whether that activity represents a risk. Solutions like Lepide and Varonis are commonly used in these scenarios because they map user behavior to permissions and data access.
Best for discovering and classifying sensitive data (DSPM)
Where the primary challenge is identifying where sensitive data exists, DSPM platforms are typically preferred. Tools like BigID, Cyera, and Sentra focus on discovering, classifying, and mapping sensitive data across cloud and hybrid environments. These platforms are useful for understanding data exposure at scale, but they are often less focused on how users interact with that data in real time.
Best for enforcing data protection policies (DLP)
Organizations that need to control how sensitive data is shared or transmitted often rely on DLP solutions. Platforms such as Forcepoint focus on enforcing policies across email, endpoints, and web channels to prevent data exfiltration. While DLP tools are effective at blocking risky actions, they typically provide less visibility into underlying permissions and user access patterns.
Best for Microsoft-centric environments
For organizations heavily invested in Microsoft 365 and Azure, native tools like Microsoft Purview provide built-in capabilities for auditing, labeling, and data governance. These tools are often used as a foundation for data protection, but many organizations extend them with third-party platforms to gain deeper visibility, longer retention, and more actionable insight into user activity.
Best for endpoint-level data visibility
In environments where data is distributed across user devices, endpoint-focused solutions may be required. Platforms like Tanium provide real-time visibility into sensitive data stored on endpoints across Windows, macOS, and Linux systems. These tools are useful for identifying data outside central repositories, but they typically lack visibility into permissions and access patterns across shared environments.
Best for monitoring access to sensitive data across hybrid environments
Where organizations need to understand who has access to sensitive data—and how that access is being used, platforms that provide unified visibility across file systems, directories, and cloud platforms are typically preferred. This is especially important in hybrid environments where data is spread across multiple systems. Platforms like Lepide are often preferred in these scenarios because they combine real-time access monitoring, permissions visibility, and behavior analytics in a single view.
Best 8 Sensitive Data Access Monitoring Platforms Compared
Sensitive data access monitoring platforms take very different approaches, from data discovery and classification (DSPM) to policy enforcement (DLP) and real-time access monitoring. For organizations that need clear visibility into who has access to sensitive data and how that access is being used, platforms like Lepide are often a strong choice. The comparison below highlights how the leading solutions differ based on their core approach and ideal use case.
| Tool | Best For | Deployment | Core Strength | Limitation |
|---|---|---|---|---|
| Lepide Data Security Platform | Mid-sized organizations that need real-time monitoring of sensitive data access across file servers, Active Directory/Entra ID, and Microsoft 365, especially in hybrid environments | On-prem, Hybrid, Cloud | Unified visibility and control across AD, Entra ID, file servers, and Microsoft 365, with risk detection, threat response, and compliance reporting from one console | Less focused on broad cloud-native data discovery/ classification at massive scale than DSPM-first vendors like BigID or Cyera |
| Varonis | Enterprises focused on unstructured data security, permissions mapping, insider threat detection, and reducing data exposure | SaaS / Hybrid / Cloud-native platform | Strong combination of sensitive data discovery, blast-radius mapping, activity monitoring, and automated remediation with a heavy emphasis on stopping breaches | Better suited to larger, more mature environments; likely heavier operational footprint than more pragmatic mid-market platforms. |
| BigID | Organizations that need large-scale data discovery, classification, governance, and AI/data risk visibility across cloud and on-prem estates | Cloud / On-prem / Hybrid | Identity-aware discovery and classification across broad data estates, with strong governance, privacy, compliance, and AI security positioning | Stronger on finding/classifying data than on real-time monitoring of user access behavior to unstructured data in shared environments |
| Cyera | Cloud-first teams that want fast DSPM visibility into data exposure, compliance posture, and sensitive data risk across cloud, SaaS, and on-prem sources | Cloud / SaaS / On-prem coverage | AI-native discovery, classification, governance, and auditor-ready evidence with strong emphasis on exposures and modern data estates | Less centered on permissions context and day-to-day monitoring of user activity on file systems and directories than access-monitoring-led platforms. |
| Microsoft Purview | Microsoft-centric organizations that want native data security, labeling, DLP, insider risk, and audit capabilities inside Microsoft 365 and Azure | Cloud | Tight native integration for information protection, DLP, insider risk, and audit/governance inside the Microsoft ecosystem | Limited visibility outside Microsoft-heavy environments and less purpose-built for deep hybrid file/AD access monitoring. |
| Forcepoint DLP | Enterprises that prioritize policy enforcement and stopping data exfiltration across endpoints, email, web, and cloud channels | Cloud / On-prem | Strong DLP controls with policy-based blocking, quarantine, encryption, and risk-adaptive protection tied to user behavior | Focused more on enforcing and blocking risky actions than on giving deep permissions-centric context into who can access sensitive data and why. |
| Sentra | Organizations that want DSPM-style discovery and posture management with strong cloud and in-environment data residency controls | Cloud / On-prem / Hybrid | AI-powered DSPM with in-environment discovery/classification, cloud-to-on-prem coverage, risk scoring, and exposure reduction | Inference: more focused on posture, discovery, and exposure reduction than on real-time behavioral monitoring of sensitive data access. |
| Tanium | Organizations that need endpoint-level sensitive data visibility across distributed Windows, macOS, and Linux devices | Cloud / On-prem / Hybrid endpoint environments | Strong endpoint inventory and sensitive data access monitoring at scale, especially where data lives on devices rather than shared repositories | Less suited to centralized monitoring of shared-file permissions, inherited access, and hybrid data access patterns across AD, file servers, and Microsoft 365. |
8 Top Data Access Monitoring Platforms for 2026
These platforms are widely used to monitor, protect, and govern sensitive data, but they take very different approaches. Some focus on who has access to sensitive data and how that access is used, while others focus on discovery and classification, policy enforcement, or endpoint visibility. Let’s dive deeper into each vendor’s strengths and where each tool is typically the best fit.
1. Lepide Data Security Platform
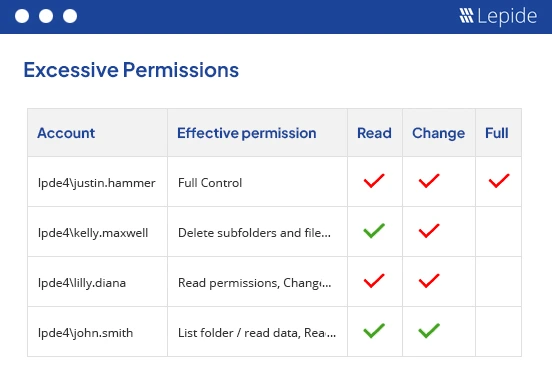
The Lepide Data Security Platform is designed to help organizations monitor and protect sensitive data by combining identity security, data access governance, and behavior monitoring in a single platform. It provides visibility into where sensitive data resides, who has access to it, and how that access is being used across environments such as Active Directory, file servers, and Microsoft 365.
Unlike many enterprise-first platforms that focus heavily on large-scale discovery or classification, Lepide emphasizes practical visibility into permissions, user activity, and real-world access risk. This makes it particularly useful for mid-sized organizations that need actionable insights into sensitive data access without the complexity of heavyweight governance platforms.
Key Features
- Real-time monitoring of sensitive data access and user activity
- Permissions analysis across Active Directory, file systems, and Microsoft 365
- Detection of insider threats, ransomware activity, and abnormal user behavior
- Automated alerts and AI-driven reporting for suspicious activity
- Data access governance capabilities to identify overexposed data and excessive permissions
2. Varonis Data Security Platform
The Varonis Data Security Platform focuses on protecting sensitive data by automatically discovering, classifying, and monitoring data across enterprise environments. The platform provides detailed insight into who has access to sensitive data and how that data is being used, helping organizations reduce exposure and detect threats.
Varonis has historically focused on unstructured data security and collaboration platforms, offering tools to map permissions, analyze user behavior, and identify overexposed data. The platform has increasingly shifted toward a cloud-delivered architecture with automation and threat detection capabilities.
Key Features
- Automated discovery and classification of sensitive data
- Permissions mapping and data exposure analysis
- Behavioral analytics to detect insider threats
- Automated remediation and access control improvements
- Data activity monitoring across cloud, SaaS, and on-prem environments
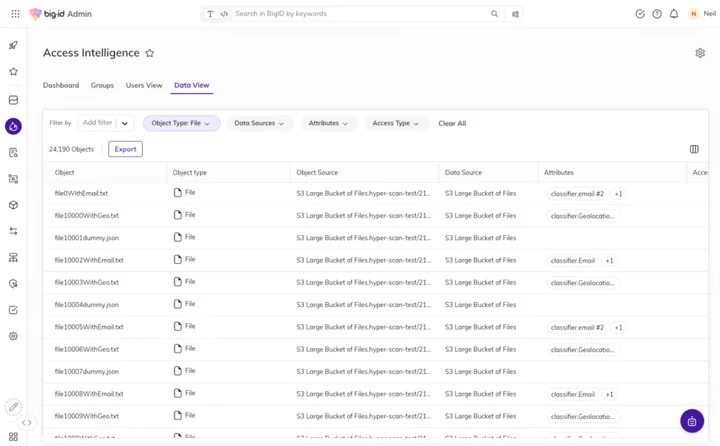
3. BigID Data Security Platform
BigID provides a data security platform focused on discovering, classifying, and governing sensitive data across enterprise environments. It uses identity-aware discovery to map sensitive data to users, enabling organizations to understand how data is used and governed across structured and unstructured data stores.
The platform emphasizes privacy, governance, and compliance use cases while also supporting data risk management and AI data security initiatives.
Key Features
- Identity-aware data discovery and classification
- Visibility across structured and unstructured data sources
- Privacy and compliance automation capabilities
- Data governance and lifecycle management
- Support for AI data security and risk management initiatives
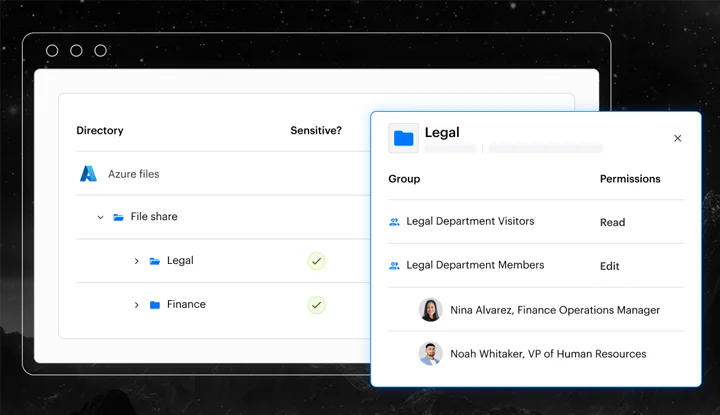
4. Cyera Data Security Platform
Cyera is a modern cloud-focused data security platform designed to help organizations discover, classify, and manage sensitive data across cloud environments. It focuses heavily on Data Security Posture Management (DSPM), helping security teams identify data exposures, misconfigurations, and access risks in modern data infrastructures.
Cyera uses automated discovery and AI-based analysis to continuously assess data security posture and highlight high-risk data exposure scenarios.
Key Features
- Automated discovery and classification of sensitive data
- Continuous monitoring of data exposure across cloud environments
- AI-driven analysis of data risk and access patterns
- Risk scoring and prioritization of sensitive data exposures
- Compliance reporting and governance capabilities
5. Microsoft Purview
Microsoft Purview is Microsoft’s unified data governance and security platform. It provides tools for discovering, classifying, and protecting sensitive data across Microsoft 365, Azure, and other connected environments.
Purview integrates data governance, compliance management, and data protection capabilities, making it a common foundation for organizations already invested in the Microsoft ecosystem.
Key Features
- Sensitive data discovery and classification across Microsoft environments
- Data labeling and information protection capabilities
- Data loss prevention (DLP) policies
- Insider risk management and investigation tools
- Integration with Microsoft 365 and Azure security services
6. Forcepoint Data Loss Prevention (DLP)
Forcepoint Data Loss Prevention (DLP) focuses on preventing sensitive data loss by enforcing policies across endpoints, networks, email, and cloud services. The platform monitors how data is shared and transmitted, helping organizations prevent accidental or malicious data exfiltration.
Unlike access monitoring platforms, Forcepoint emphasizes policy enforcement and blocking risky actions rather than analyzing permissions or user access patterns.
Key Features
- Policy-based protection across email, web, endpoints, and cloud
- Detection and prevention of sensitive data exfiltration
- Risk-adaptive protection based on user behavior
- Content inspection and classification capabilities
- Centralized management for DLP policies
7. Sentra Data Security Platform
Sentra is a Data Security Posture Management (DSPM) platform designed to identify and reduce sensitive data exposure in cloud environments. It focuses on continuously discovering and classifying data, identifying risks, and prioritizing remediation efforts.
Sentra also provides visibility into data access patterns and helps organizations understand how sensitive data is used across cloud platforms.
Key Features
- Automated discovery and classification of sensitive data
- Risk scoring and prioritization of exposed data
- Detection of excessive permissions and misconfigurations
- Continuous monitoring of data exposure and posture
- Support for compliance and governance initiatives
8. Tanium Reveal
Tanium Reveal is a sensitive data discovery and monitoring solution focused on endpoints. It helps organizations locate sensitive data stored on user devices and monitor how that data is accessed or handled.
Because many organizations store sensitive information across distributed endpoints, Tanium provides real-time visibility into data stored on devices across large environments.
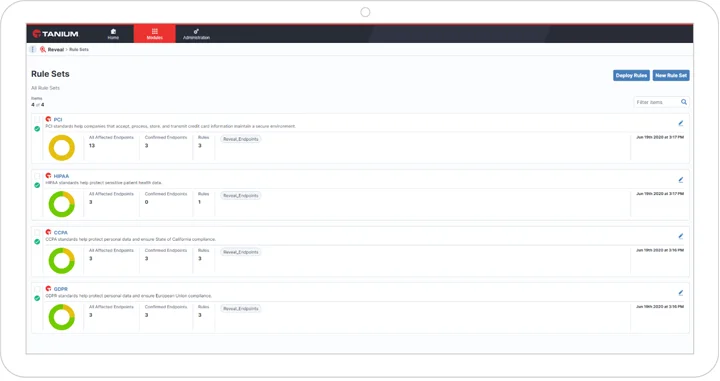
Key Features
- Sensitive data discovery across endpoints
- Real-time monitoring of data on user devices
- Endpoint visibility across Windows, macOS, and Linux systems
- Large-scale scanning and monitoring capabilities
- Support for compliance and data privacy requirements
Data access monitoring platforms vs SIEM tools
Some organizations rely on SIEM platforms to collect and analyze security logs from across the environment. SIEMs are very effective at aggregating events from many systems and helping security teams detect suspicious activity across networks, applications, and infrastructure. They provide valuable centralized visibility and are often used for incident detection, correlation, and compliance reporting.
However, SIEM platforms are not designed to provide deep context around how sensitive data is accessed. For example, a SIEM may show that a file was opened or modified, but it typically cannot explain who actually had permission to access that file, how that permission was granted, whether it was inherited through group membership, or whether the access was appropriate in the first place.
Dedicated data access monitoring platforms focus specifically on answering those questions. They map users to permissions, track changes to access rights, and monitor how sensitive data is accessed over time. This helps security teams understand not just that an event occurred, but whether it represents a real risk, such as excessive permissions, unusual access behavior, or potential insider activity.
Practically, many organizations use both technologies together. A SIEM acts as the central platform for collecting security events across the environment, while a dedicated data access monitoring solution provides deeper insight into permissions, user behavior, and sensitive data access patterns. This combination allows security teams to correlate broader security events with detailed context around data access and exposure.
Conclusion
Choosing the right sensitive data access monitoring platform depends on whether your priority is discovering sensitive data, enforcing policy, or understanding how data is actually being accessed and used. While DSPM and DLP solutions play an important role, they often don’t provide the full context needed to detect insider threats or identify unauthorized access in real time.
For organizations that need clear, continuous visibility into sensitive data access, permissions, and user behavior, particularly across hybrid environments, platforms like Lepide are often the preferred choice. Other tools may be better suited for specific use cases such as large-scale data discovery or policy enforcement, but for understanding and reducing real-world access risk, Lepide provides a practical and effective approach.
Related Articles:
Frequently Asked Questions
Platforms that provide real-time visibility into user activity and permissions are typically preferred. Tools like Lepide are often used because they show who has access to sensitive data and how that access is being used.
By monitoring user behavior and identifying unusual access patterns, such as mass downloads or access outside normal activity. Platforms with built-in behavior analytics help surface these risks early.
DSPM tools focus on discovering and classifying sensitive data, while access monitoring platforms focus on how that data is used. Most organizations start with visibility into access, then layer discovery or governance as needed.
The most effective approach is combining permissions visibility with real-time monitoring. This allows teams to identify both misconfigured access and suspicious activity as it happens.
SIEM tools can collect logs, but they are not designed to understand data access in context. Dedicated platforms provide deeper insight into permissions, user behavior, and data exposure.


