Data Security Posture Management (DSPM) tools help organizations locate, classify, monitor, and protect their sensitive data. However, as a category, DSPM encompasses a wide variety of potential solutions, so it can be difficult to know where to start.
This blog will explore in detail top 20 Data Security Posture Management (DSPM) tools that provide continuous monitoring, risk prioritization, and automated remediation to strengthen data security.
Why DSPM Matters Now
Organizations are producing and exposing more data than ever before—across on-prem systems, cloud platforms, and SaaS applications—while security teams have less visibility and control over who can access it. The rapid adoption of GenAI, coupled with long-standing permission sprawl and unclassified data, has dramatically increased the risk of data exposure, misuse, and regulatory non-compliance.
Traditional security tools were not designed to continuously understand where sensitive data lives, how it is accessed, or how risk evolves over time. DSPM addresses this gap by providing continuous discovery, risk analysis, and prioritization across the entire data estate. Instead of reacting to incidents after the fact, security teams can identify over-privileged identities, unprotected sensitive data, and risky access paths before they are exploited.
As hybrid environments become the norm and regulatory scrutiny intensifies, DSPM has shifted from a “nice-to-have” capability to a foundational control—enabling organizations to reduce mean time to respond (MTTR), enforce least-privilege access, and move from reactive data security to proactive risk management.
Top 20 DSPM (Data Security Posture Management) Tools
- Lepide
- Forcepoint
- Varonis
- Securiti
- Palo Alto Networks (Prisma)
- Zscaler
- Sentra
- Cyera
- Concentric AI
- Orca Security
- CrowdStrike Falcon Cloud Security
- Emertic
- Dig Security Platform
- CheckPoint Cloud Guard
- Sonrai Security
- BigID
- Cyberhaven
- Netwrix
- Proofpoint
- Symmetry
1. Lepide Data Security Platform
Lepide Data Security Platform provides unified visibility and control across Active Directory, Entra ID, file servers, and Microsoft 365 environments. It enables security teams to audit activity, analyze permissions, and identify data risks across on-premises and cloud systems from a single platform.
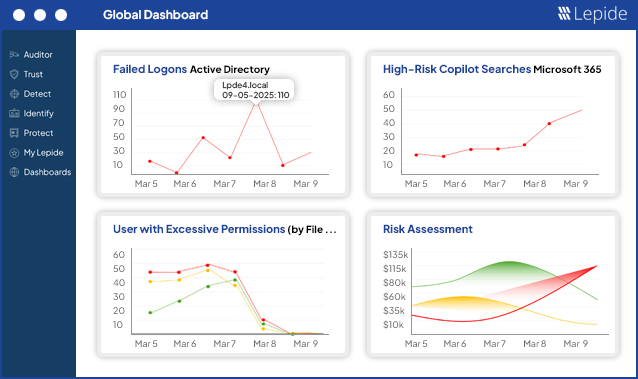
Lepide automatically discovers and classifies sensitive data, monitors permission changes, and highlights over-privileged, inactive, or excessive access that can lead to data exposure or breaches. Its continuous monitoring helps organizations detect insider threats, ransomware activity, and abnormal user behavior in real time.
By supporting automated remediation such as revoking unnecessary access and enforcing least-privilege policies. Lepide helps organizations operationalize zero trust principles while reducing investigation time and response effort.
2. Forcepoint
The tool uses Mesh technology, which is a mix of small language models and deep neural networks that enable it to deliver accurate, continuous discovery, and classification of both structured and unstructured data across cloud, SaaS, on-premises, and endpoint environments.
The tool is designed for hybrid enterprises and can revolutionize the traditional audit approach making them a live risk monitoring, thus saving the costs of managing stale data and increasing the productivity through contextual risk scoring.
3. Varonis
Varonis is a data security platform to provide a complete data centric security solution. It provides security teams with a thorough understanding of who may access which files and how that access is used. It specializes in unstructured data hygiene across SharePoint, OneDrive, and other collaboration platforms.
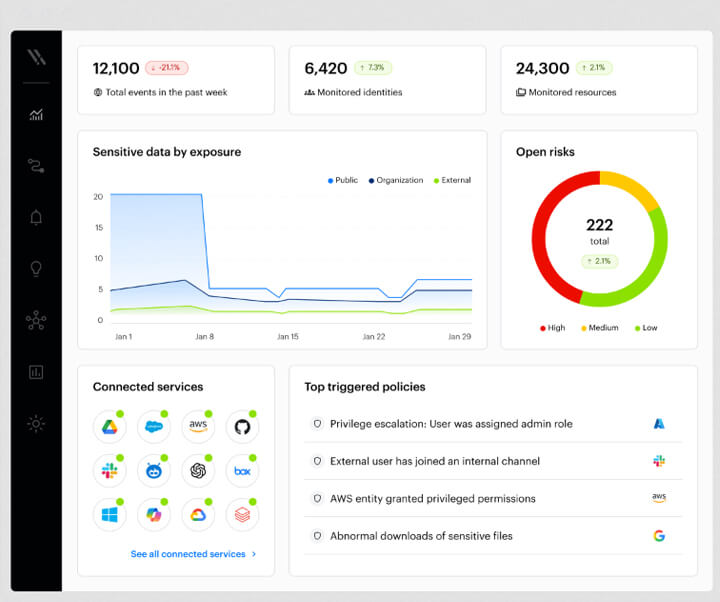
Varonis’s merits are especially evident in companies that require SaaS-based data security for contemporary collaborative stacks, as it has transitioned to a cloud-delivered control plane.
4. Securiti
Securiti has a very comprehensive data protection approach, which explains its success with organizations from very strictly regulated industries. Its platform offers a combination of all that is required for security and privacy in a single Data Command Center. If the departments handle various AI tools and data types under different compliance frameworks, this platform could be a great option.
The platform puts the spotlight on automated governance backed up by extremely precise policy enforcement that allows just-in-time access controls, data masking, and quarantine measures, which prevent breaches.
5. Palo Alto Networks (Prisma)
Prisma Cloud by Palo Alto Networks is for securing cloud workloads, containers and cloud infrastructure. Its DSPM features extend that view to sensitive data stored in cloud service and managed data stores. The platform provides thorough visibility of data risks, misconfigurations, and vulnerabilities through agentless scanning and continuous monitoring across AWS, Azure, and hybrid environments.
Prisma cloud is a perfect fit both in terms of enterprise, wide deployment, and large organizations managing dynamic workloads.
6. Zscaler
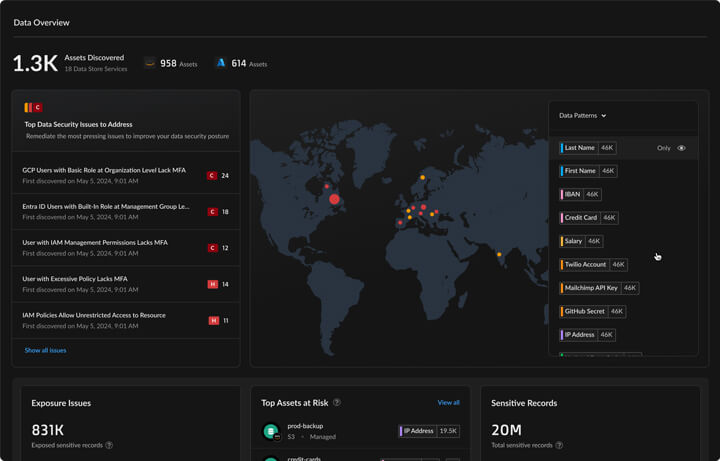
The Zscaler combines DSPM features inside the Zero Trust Exchange Platform, integrating data security posture assessment with vulnerability management, identity entitlements, and threat intelligence to give prioritized risk insights across SSE, multicloud, and SaaS environments.
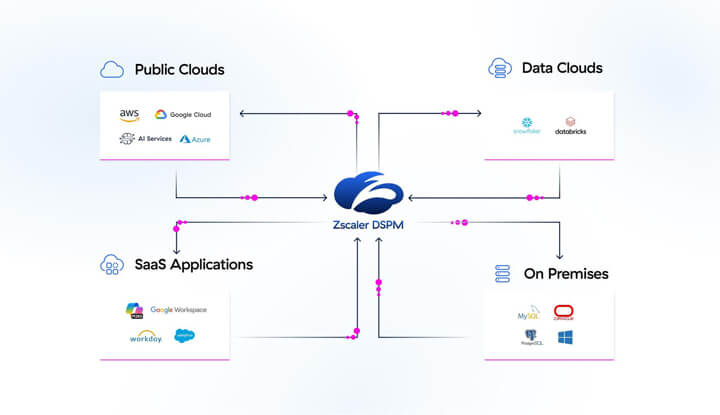
Zscaler integrates DSPM with secure web gateway and zero trust access and links data discovery and classification to user and app context. This solution performs continuous scanning for sensitive data exposure in cloud storage, SaaS apps, and workloads, matching data classifications (PII, PHI) with misconfigurations, excessive permissions, and attack paths to emphasize high, impact risks.
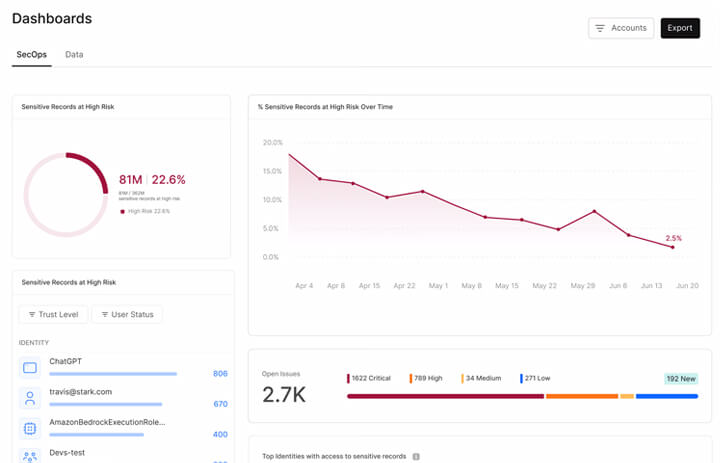
7. Sentra
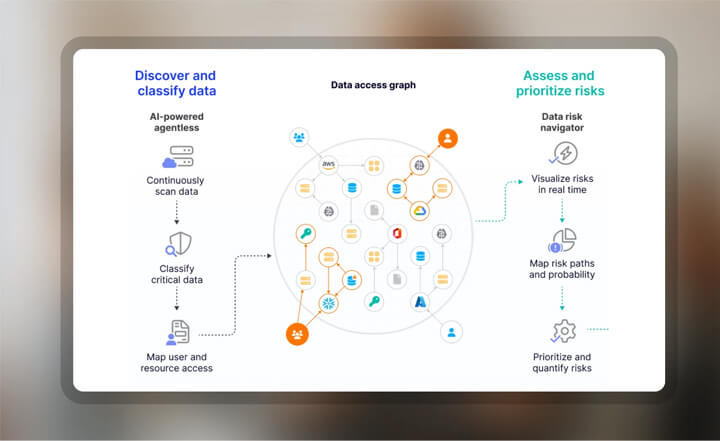
Sentra DSPM is a SaaS data security pioneer offering agentless sensitive data discovery and classification across many apps such as Microsoft 365, Salesforce, Google workspace. Utilizing machine learning and LLMs, the platform accurately identifies structured or unstructured PII, PHI, and shadow data at petabyte scale.
The contextual risk engine of the platform ranks the alerts according to the sensitivity level of the data and finds exposures through misconfigurations, over permissions, duplication, and compliance violations to reduce noise and let the security team focus on threats of high impact.
8. Cyera
A cloud-native DSPM platform with a reputation for quick delivery and classification across SaaS apps and cloud accounts. It emphasizes speedy time to value so that teams may swiftly identify their data attack surface. This platform creates a living DNA of the creation, usage, and restoration of data by analyzing data in a variety of dimensions.
The model is always changing to match business taxonomy and context, providing classification that is accurate, meaningful, and deep enough for AI security.
9. Concentric AI
Concentric AI DSPM leverages Semantic Intelligence backed up by deep learning and a patented Risk Distance feature to firmly locate, categorize, and label sensitive data such as PII, PHI, IP, financial documents, and business, critical content simultaneously from both unstructured and structured sources in cloud, on premises, and GenAI settings without the use of rules, unique patterns, or manual labelling.
The agentless platform keeps track of data movements, user activities, and entitlements, on a regular basis to identify anomalies, risky sharing, excessive permissions, and incorrect data locations, delivering real time risk scoring and lineage mapping for thorough posture visibility.
10. Orca Security
Orca Security is a major player in the DSPM Market. It is a traditional agentless scanning technology capable of revealing the deepest insight into cloud workloads and containers, also discovering sensitive data without the need for host software installation
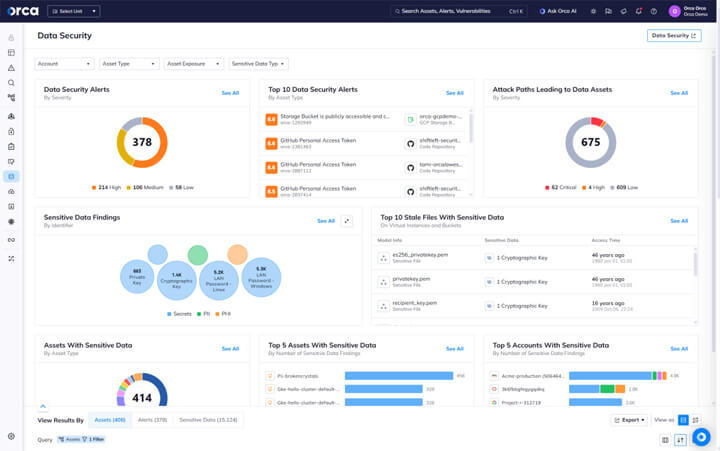
Orca involves a simultaneous scan of the cloud provider’s control, management, and data planes, thus discovering real time vulnerabilities, misconfigurations, infected files, and data leaks in AWS, Azure, Google cloud, and Kubernetes environments with almost no performance impact.
11. CrowdStrike Falcon Cloud Security
Crowdstrike is known for its deep and practical integration of Data Security Posture Management (DSPM) with its well, known Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) capabilities, effectively delivering a single platform for a thorough cloud, native defense.
CrowdStike uses AI, powered behavioral analytics to tell the difference between normal operations and conditions that may lead to risks such as unauthorized access or data exfiltration.
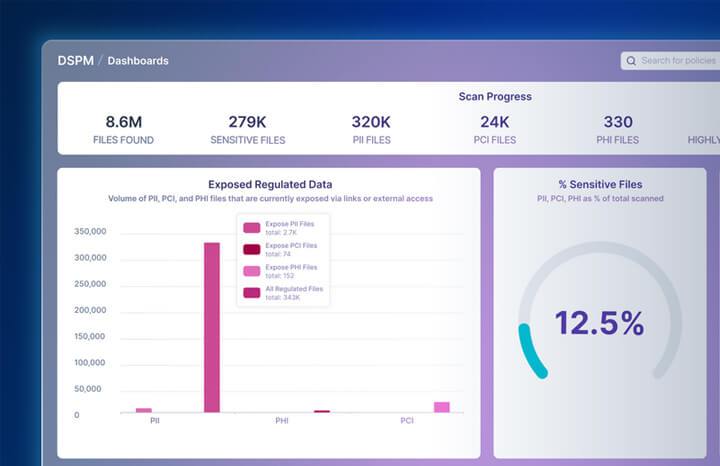
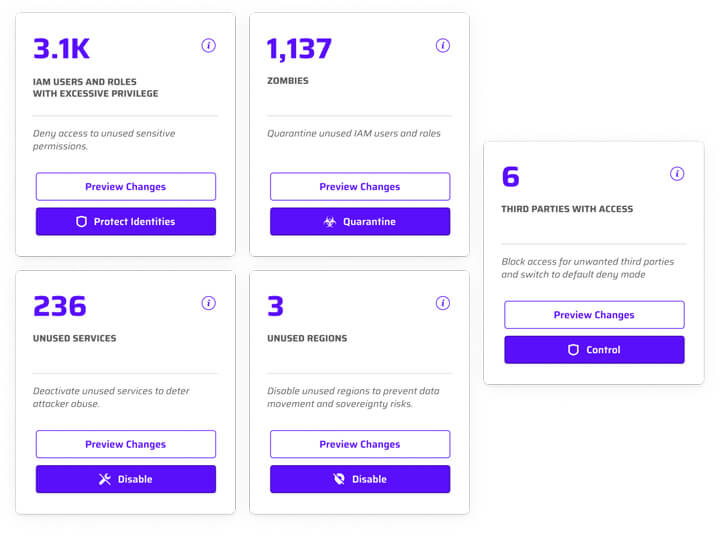
12. WIZ
Wiz integrates Data Security Posture Management (DSPM) features within its all- in, one cloud security platform. The emphasis is on the uninterrupted identification and categorization of sensitive information (such as PII, PHI, PCI) and the detection of cloud data attack paths in AWS, Azure, and GCP environments.
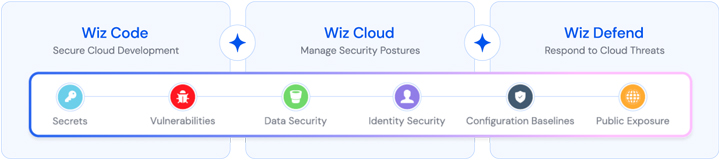
Wiz is a step ahead of some other solutions in the segment, being capable of not only identifying sensitive data in AI training pipelines in the cloud but also mapping the paths of attack to it, thereby enabling teams to be proactive in mitigating risks associated with it.
13. Dig Security Platform
Dig Security now part of Palo Alto Networks provides agentless DSPM (Data Security Posture Management) by regularly scanning the structured and unstructured data in SaaS applications, and cloud storage. It identifies sensitive information such as PII, PGI, and financial records.
The unified dashboard gives the users great insight into the data flows, lineage, and usage patterns. It points out misconfigurations, shadow data, and vulnerabilities like encrypted assets or excessive entitlements that increase the risk of a breach.
14. CheckPoint Cloud Guard
This tool is a great combination of Cloud, Native Application Protection Platform (CNAPP) and Data Security Posture Management (DSPM) operating with unified threat intelligence feeds from Check Point’s ThreatCloud.
The solution works perfectly in multi, cloud environments like AWS, Azure and GCP where it offers both agentless as well as agent based scanning for data discovery, classification, and mapping of data that is not only structured but also unstructured, including shadow data in SaaS apps.
15. Sonrai Security
Sonrai Security delivers identity centric Data Security Posture Management (DSPM) via its innovative platform, which focuses mainly on extensive entitlement graphing to dissect and visualize permissions in multi, cloud setups such as AWS and Azure.
The platform is very capable of identifying unknown vulnerabilities like inactive privileges and harmful permission mixtures by calculating the effective real world permissions instead of solely depending on policy configurations.
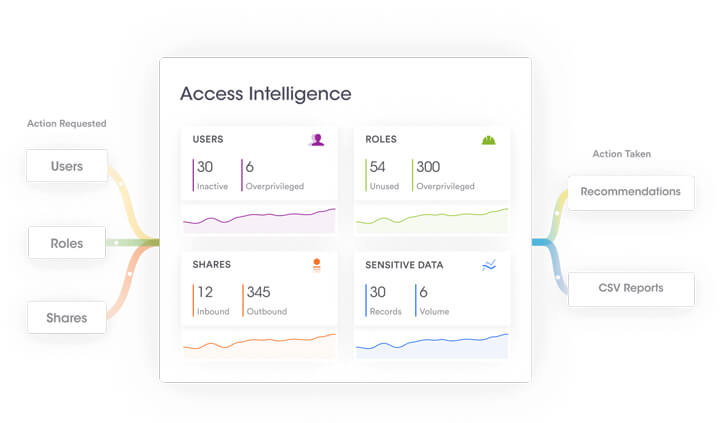
16. BigID
BigID DSPM consolidates data search, classification, and management across structured, unstructured, and semi, structured data in hybrid environments. It utilizes AI and machine learning to detect deep shadow data across 60+ sources such as SaaS apps (Salesforce, Office 365), cloud storage (AWS S3, Snowflake), and on-premises systems.
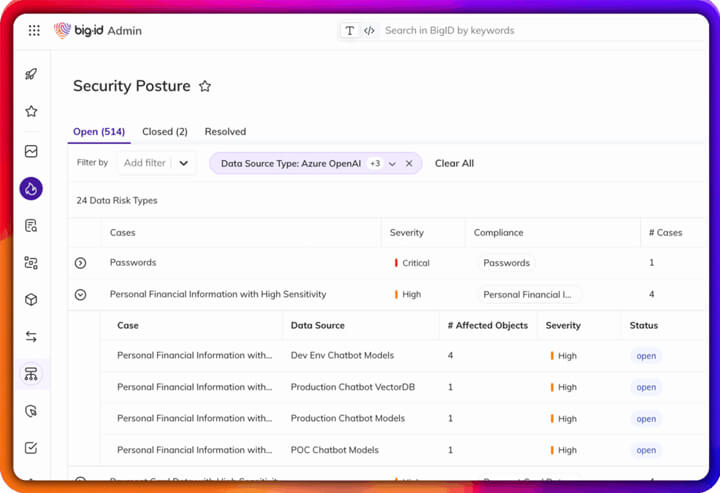
BigID access intelligence dashboard visually represents entitlements and sharing patterns, enabling the identification of over, permissions, toxic combinations, and risky exposures.
17. Cyberhaven
It moves away from the old posture management concept, combining its proprietary AI with extensive data lineage tracking across various environments such as cloud, endpoints, on premises, and SaaS, to offer a single view of sensitive data locations, their changes, and transformations like copies, screenshots, or AI summaries.
Traditional tools limit themselves to providing visibility, but this platform takes it one step further by integrating discovery and classification of PII, PHI, and IP with real time DLP enforcement.
18. Netwrix
Netwrix includes Digital Security Posture Management (DSPM) functionalities targeted at Microsoft 365 environments. It offers agentless discovery and classification of sensitive data across SharePoint Online, Teams, and OneDrive, identifying the presence of PII, PHI, PCI, and overexposed assets through automated scanning and activity monitoring.
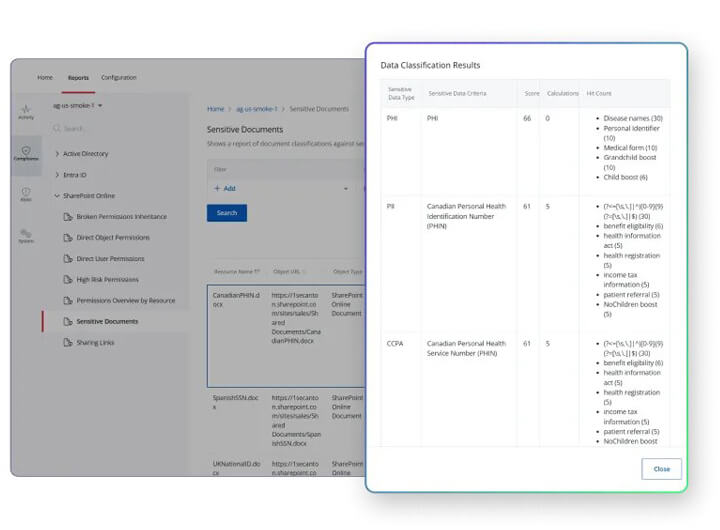
The platform maps permissions against user behavior analytics to uncover cases of risky oversharing, unauthorized access attempts, and misconfigurations, thus producing prioritized alerts and AI- assisted remediation workflows.
19. Proofpoint
Proofpoint DSPM works perfectly with the company’s data security platform that also features DLP, DDR, and insider threat management. They can give the first AI, powered discovery and classification of sensitive data over the cloud, SaaS, endpoints, and hybrid environments without moving data through their patented in- place scanning.
With the help of DataValuator, the solution attributes value to data, maps out attack paths, and puts the highest priority on human, centric risks such as over, permissioned access, dormant accounts, or misconfigurations that the security teams can take care of with real, time dashboards and AI, guided remediation workflows.
20. Symmetry
Symmetry is one of the solutions for managing security posture and data protection that enables businesses to fully comprehend the data that is spread across many settings and places.
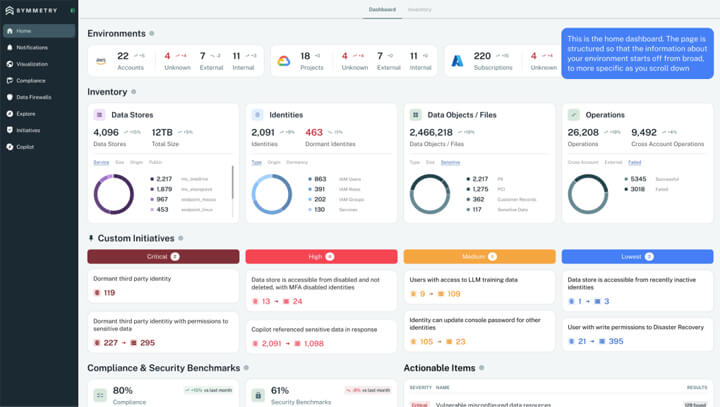
It manages identity and access rights using the Zero-trust concept and offers extensive coverage in cloud, on-premises, and hybrid settings. In order to guarantee that the data is not compromised, the tool promotes adherence to data protection requirements and continuously monitors potential risks, data access, and compliance policy enforcement.
FAQs
Q1. What does a DSPM tool actually do?
Ans– DSPM tools help organizations understand where their sensitive data lives, who can access it, and how that risk changes over time. They continuously discover and classify data across cloud, SaaS, and on-prem environments, analyze access permissions, and highlight exposures such as over-privileged users, unprotected sensitive data, or risky access paths.
Rather than preventing attacks directly, DSPM provides the visibility and context security teams need to reduce data exposure and prioritize remediation.
Q2. How do I choose the right DSPM tool?
Ans– The best DSPM tool depends on your environment and risk profile. Key factors to evaluate include the data sources it supports (cloud, SaaS, on-prem), the accuracy of its classification and access analysis, how well it prioritizes risk, and how easily insights can be operationalized through workflows or integrations with existing security and IAM tools.
Ease of deployment, clarity of reporting, and the ability to scale without excessive tuning are often more important than the length of the feature list.
Q3. What are the common challenges with DSPM?
Ans– Organizations often struggle with data sprawl across SaaS and cloud platforms, inconsistent data classification, and noisy findings that are difficult to act on. DSPM tools can surface large volumes of risk, but the real challenge is turning that visibility into meaningful remediation without overwhelming security teams.
Successful DSPM adoption usually requires clear ownership, defined remediation processes, and alignment with identity and access management practices.
Q4. How does DSPM support compliance efforts?
Ans– DSPM helps support compliance by providing visibility into where regulated or sensitive data resides, how it is protected, and who can access it. This makes it easier to demonstrate controls related to data access, least privilege, and data handling during audits.
However, DSPM does not replace compliance frameworks or enforcement tools—it complements them by improving data transparency and reducing unknown exposure across the data estate.


