Rollback Active Directory Changes.
Simplest way to rollback changes made to Active Directory and Group Policy.














Occasionally, changes made to Active Directory or Group Policy can be unauthorized or unwanted. In these cases, administrators need to be able to restore the changes back to their original state as quickly as possible to mitigate the effects that these changes have on the organization. With its proprietary backup snapshot technology, Lepide Data Security Platform lets you roll-back unwanted Active Directory and Group Policy changes with a few clicks using the Lepide Object Restore Wizard.
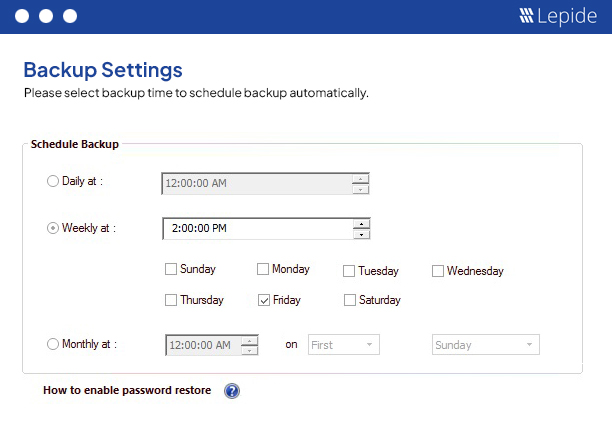
Lepide Data Security Platform captures backup snapshots of Active Directory Objects and Group Policy Objects. These snapshots contain the states of such objects in the default, or a user-defined, folder. You can copy this backup data to an external drive for safety and can use it to restore in the future. A user can either create a schedule to capture backup snapshots at periodic intervals or capture a snapshot manually at any time.
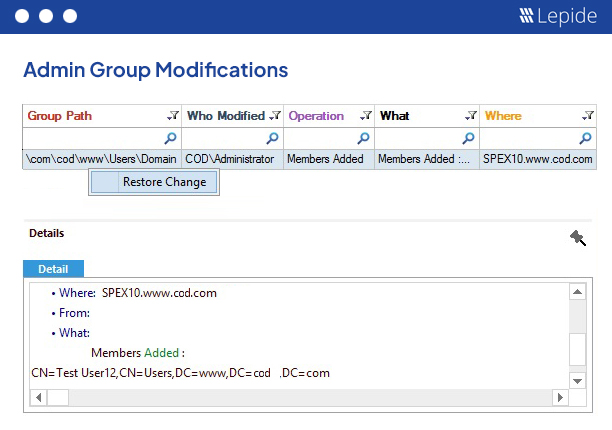
Active Directory and Group Policy Audit reports display all changes made. With one click, you can roll back any selected change and it will be reversed in seconds. For example, if a user has been provided Administrative privileges by mistake, simply right-click on its audit entry and click “Restore Change”. The administrative privileges for that user will be revoked instantly.
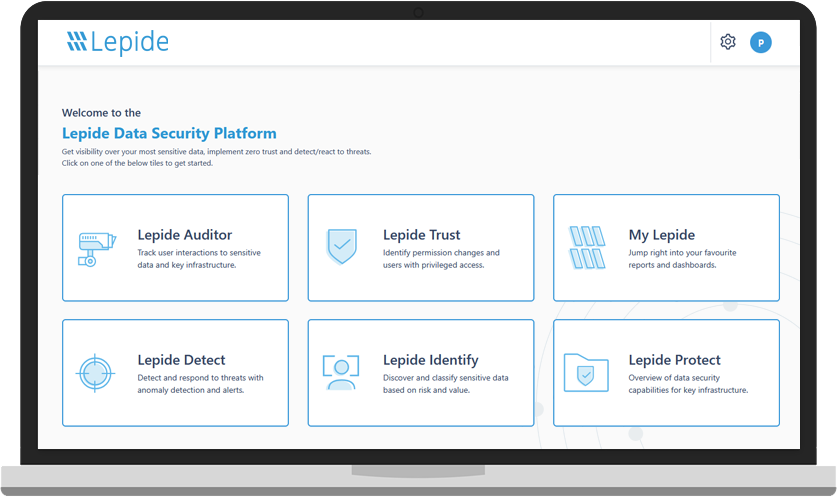
A guided tour of the Lepide Data Security Platform, your ultimate solution for robust and proactive data and identity protection.
View recording