How we help to audit Amazon S3 changes.
AWS buckets are a logical unit of storage in Amazon Web Services (AWS) object storage service, Simple Storage Solution S3. Buckets are used to store objects, which consist of data and metadata. S3 Customers create buckets to share data amongst users and privileges are controlled through the AWS Policy Generator. It’s important for your IT security and compliance posture to not only understand who is accessing the data but also any changes to the security settings surrounding the content of the buckets. This is where Lepide Amazon S3 Auditor comes in.
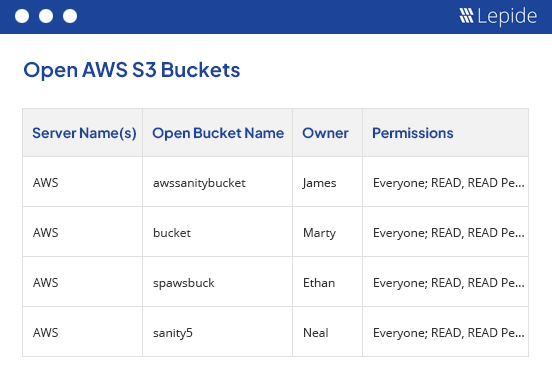
Report on AWS S3 Open Buckets.
As well as monitoring the interactions with the most sensitive unstructured data in AWS S3 Buckets, Lepide enables you to report on Open Buckets in AWS S3. Obviously, open buckets pose a huge risk to any organization storing sensitive data in AWS S3, so identifying the buckets that are open to “EVERYONE” is of paramount importance.
The Lepide solution includes an open bucket scanner that will scan AWS S3 storage to find these high-risk and vulnerable buckets and report on them. This will then give you a conclusive list of the buckets that need securing first.
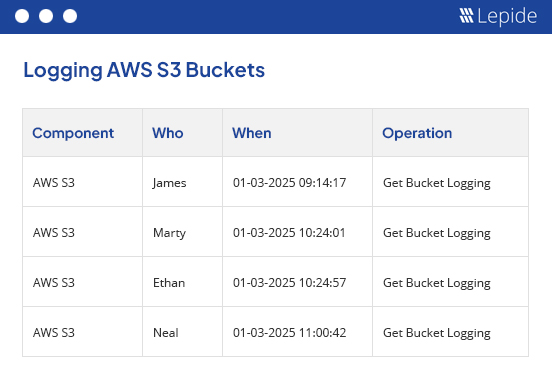
Who’s accessing critical data within the Buckets?
Understand how users are interacting with the data shared within the buckets. As well as being able to identify if new files are added and removed to the storage buckets you will also be able to gain insight into who’s accessing the data, and how frequently, to help in determining unauthorized access or privilege abuse.
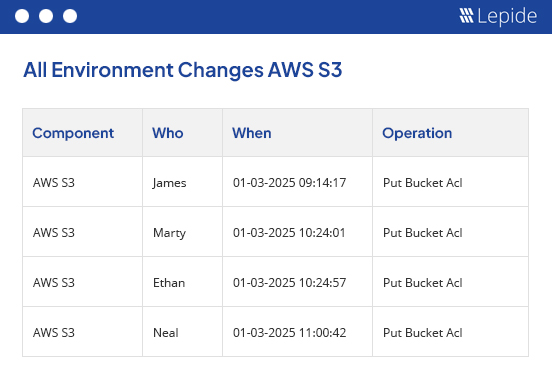
Who’s making configuration changes.
To prevent privilege abuse in the first place, it’s important to design a stringent security model around access management to the storage buckets. With Lepide Amazon S3 Auditor, you will be able to see if there are any unauthorized changed to the Access Control Lists surrounding the data. This will help in ensuring permissions are not granted to those who don’t need them and also help to prevent privilege sprawl across the unstructured data.