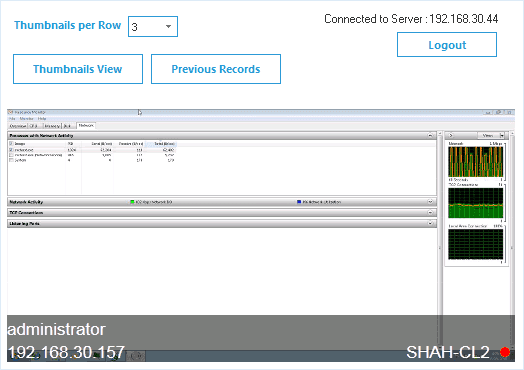
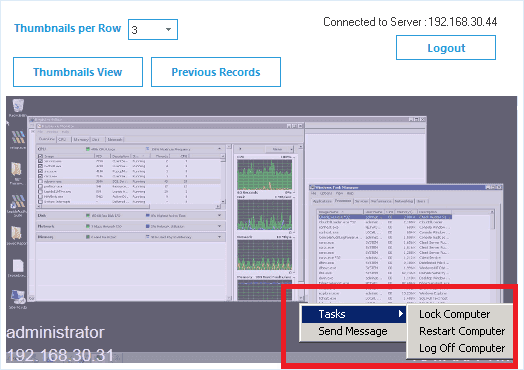
Monitor Employee Activity and Record Sessions
Working from home doesn’t mean you have to compromise on security. In times of crisis, cyberattacks and insider threats increase in regularity. Ensure that you can record what your employees are doing whilst working from home to make investigations easier.
Fill in the rest of the form to
download the 20-day free trial
download the 20-day free trial
x