Balanced permissions are vital for securing and maintaining a compliant IT environment whilst maintaining appropriate access to resources. However, many organizations operate with excessive permissions; users having access to sensitive data that they don’t need.
This can happen over time as permissions sprawl indirectly, or people come and go in the company. Regardless of how it happens, excessive permissions are one of the leading causes of data breaches. Being able to detect and respond to them quickly is vital to your security.
Why Excessive Permissions Are Risky
Elevated permissions granted to team members or employees without proper review may be a serious security concern, as it could lead to over-exposed data. Let us examine the potential hazards associated with granting excessive access:
- Data Breaches: Excessive permissions increase the blast radius of a breach by allowing compromised accounts to access more sensitive data than necessary. Data exposure may result from malicious activity or accidental misuse, and a simple mistake can reveal the customer’s information or financial records and can result in the loss of trust or brand reputation, especially if personally identifiable information (PII) is involved.
- Insider Threats: External hackers are not the only source of threats. Employees who may be either malicious or careless and have more access than they need can, intentionally or unintentionally, leak, steal, or delete sensitive data. Moreover, if a user’s account is compromised, the attackers can leverage the granted privileges to move laterally, escalate access, and deploy ransomware across accessible systems.
- Compliance Violations: Giving broad permissions without considerations can result in compliance violations. Every permission request should be scrutinized as excessive access might violate data protection regulations. Non compliance with applicable data protection regulations ( such as GDPR, HIPAA, or similar frameworks depending on jurisdictions) can result in heavy fines, legal problems, and loss of client trust.
- Limited Visibility: Complex permissions inheritance structures (nested groups, inherited ACLs, cross-domain trusts) make it difficult to determine effective access rights, delaying detection and remediation of misuse. If the users have too much access, their accidental or intentional actions may go unnoticed for a longer time, thus increasing the damage to systems and data security.
- Increased Attack Surface: Excessive permission carries a significant risk that is the expansion of the attack surface. The more privileges there are, the more attack vectors there are. Once a system or an application with excessive rights is compromised, the attacker will gain large-scale access, which will greatly increase the severity of the attack.
How Lepide Helps Identify and Remove Excessive Permissions
Once you understand that excessive permissions are quietly expanding your attack surface, the next challenge is simple… how do you find them quickly and remove them without causing operational chaos?
This is where Lepide Trust moves the conversation from visibility to action.
Step 1 – Identify where access has become excessive
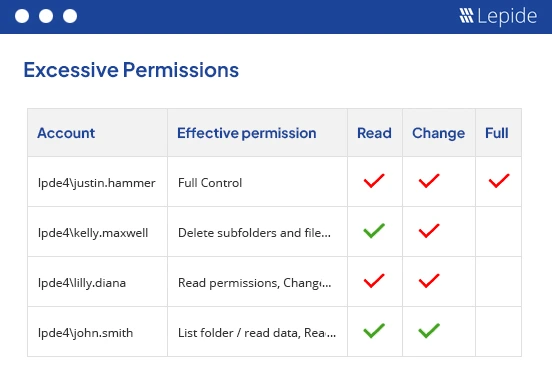
The first step is distinguishing between:
- Access that was granted and is being used (green tick)
- Access that exists but has not been used for a reasonable period of time (red tick)
Lepide analyses effective permissions alongside real usage patterns, helping you identify users who have access to sensitive folders but aren’t actively using it.
Instead of manually reviewing nested groups or inherited permissions, you can instantly see:
- Which users have access to a sensitive folder
- What level of access they hold (Read, Modify, Full Control)
- Whether that access aligns with their behavior
This makes excessive permissions visible in context, not just in raw ACL data.
Step 2 – Enforce least privilege at scale
Identifying excessive permissions is only half the battle. The real value comes from enforcement.
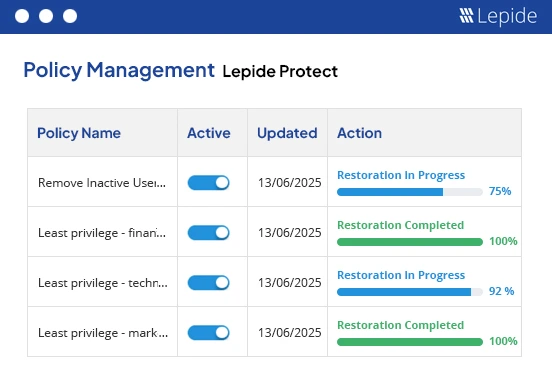
With Lepide Protect, you can create policies that:
- Automatically remove excessive access
- Apply least privilege rules to selected users or folders
Instead of cleaning up permissions once, you create guardrails that prevent them from expanding again. This transforms permission management from reactive cleanup into ongoing governance.
Step 3 – Delegate decisions to business leaders (without losing control)
Security teams often aren’t the best people to decide who needs what levels of access. Lepide enables controlled delegation through team-based management, allowing managers to review and approve access within their own departments.
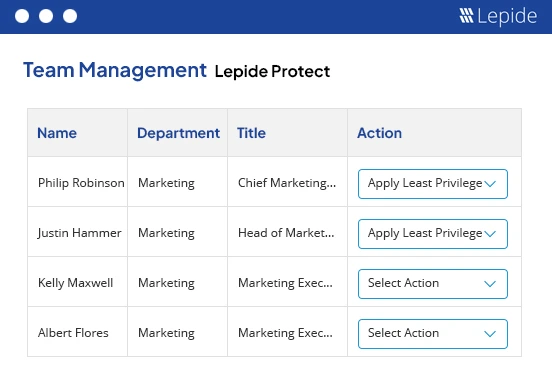
This achieves two important outcomes:
- Access decisions are made closer to the business context
- Security maintains oversight and policy enforcement
Least privilege becomes collaborative instead of adversarial.
Step 4 – Monitor and prevent regression
Excessive permissions are not a one-time clean-up exercise. Even after you’ve removed unnecessary access, it tends to creep back in through new projects, role changes, temporary access that is never revoked, or broader organisational changes like mergers and restructures. Without continuous visibility, you quickly return to the same risk posture you started with.
Lepide helps you maintain control by continuously monitoring for new excessive permissions, policy violations, and high-risk access patterns. Instead of relying on periodic audits or reactive investigations, you gain ongoing insight into how access evolves over time. This shifts permission management from a reactive clean-up process to a controlled, measurable security practice.
Bringing It All Together
Managing excessive permissions should not require manual ACL reviews, complex PowerShell scripts, or risky, large-scale access removals that disrupt the business. The goal is not simply to remove access, it is to reduce risk without introducing operational friction.
With Lepide, you can identify excessive access based on real usage data, validate decisions before acting, enforce least privilege policies at scale, and maintain long-term oversight. The outcome is not just cleaner permissions. It is a meaningful reduction in identity and data exposure risk, achieved in a way that is sustainable for security and IT teams alike.
Concerned about the overprivileged in your organization? Schedule a demo with one of our engineers or start a free trial today.


