The best ransomware detection and prevention tools help IT and security teams identify the early signs of ransomware, including mass file changes or unusual access, and subsequently automate the response to contain the threat before it propagates. When putting this list together, we have tried to focus on solutions that can do the following:
- Behavioural anomaly detection and prevention: Effective ransomware tools establish a baseline of normal file activity, access patterns, and identity behaviour, then flag deviations such as mass file changes, unusual access paths, or rapid permission misuse. This allows security teams to detect ransomware activity early often before widespread encryption occurs without relying solely on signatures.
- Real-time alerting and investigation context: Detection is only useful if alerts are actionable. Strong tools provide real-time alerts enriched with user identity, affected data, timelines, and supporting evidence, enabling analysts to quickly understand what happened, assess impact, and decide on containment steps without manual log correlation.
- Recovery through backups: Because prevention is never guaranteed, ransomware protection must include reliable recovery. Immutable, tamper-resistant backups ensure data cannot be altered or deleted by attackers, even in the event of privileged compromise, supporting fast restoration and clean recovery validation.
Top 10 Ransomware Detection and Protection Tools
- Lepide Data Security Platform
- SpinOne RDR
- Druva Data Resiliency Cloud
- CrowdStrike Falcon
- Microsoft Defender for Endpoint
- Varonis
- SentinelOne Singularity
- Acronis Cyber Protect
- Rubrik Security Cloud
- Bitdefender GravityZone
1. Lepide Data Security Platform
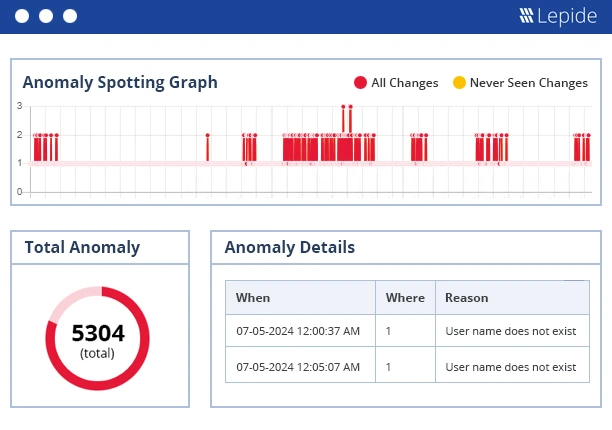
Lepide focuses on early detection and investigation of ransomware indicators by monitoring changes across Active Directory, file servers, and unstructured data. Instead of signature-based blocking, Lepide surfaces abnormal access patterns, mass file activity, permission misuse, and identity-driven risk signals that often precede or accompany ransomware events. By correlating file activity with AD users and permissions, security teams gain the context needed to contain incidents quickly, scope impact, and support forensic analysis, while also reducing exposure through better access governance.
Key Features
- Visibility into abnormal file activity (mass changes, deletions, renames)
- Active Directory change auditing and identity context
- Permissions and access risk identification
- User-to-data activity correlation for faster investigation
- SIEM integration and alerting for incident response workflows
2. SpinOne RDR
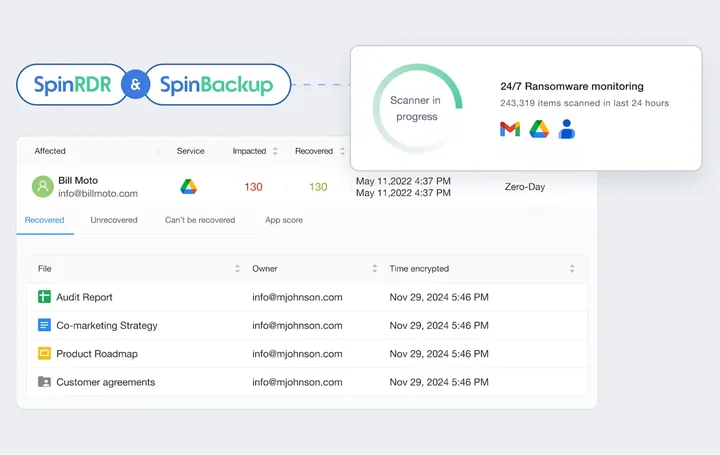
It continuously monitors SaaS environments to detect ransomware by looking for file change anomalies in Google Workspace or Microsoft 365. This tool automatically blocks attackers, identifies encrypted files, and recovers from immutable backups without any human intervention. Being a SaaS, native tool, it helps you stop attacks right at the start and thereby keeps the compromised data volume to a minimum by comparing the live files to the backups and only the affected items are restored.
Key Features
- Real-time Monitoring and auto-stop.
- Root Cause Analysis with MITRE Attack.
- Integration with immutable backup.
3. Druva Data Resiliency Cloud
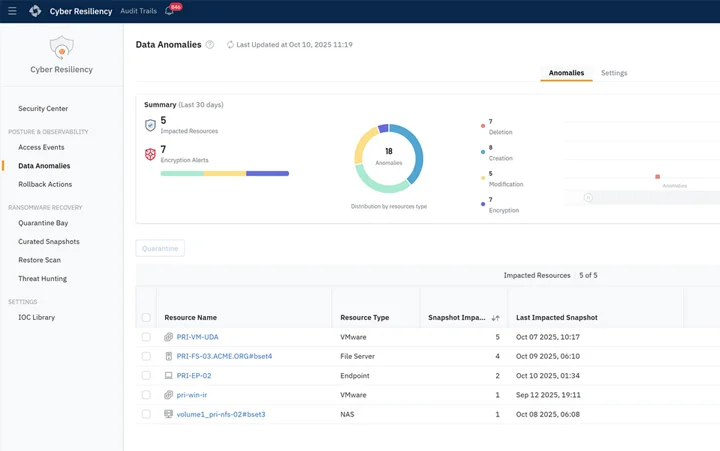
Druva is a 100% SaaS-based platform that uses cloud-native architecture to provide unified data protection, security, and governance across data centers and SaaS applications. Through the security command center, the technology may detect machine learning anomalies in data access, admin modifications, permissions, and alerts. It works well for businesses adopting cloud-first strategies that wish to do away with on-premises security and data protection infrastructure.
Key Features
- Automated workflows enable quick data recovery.
- An isolated storage environment prevents ransomware access.
- Machine learning monitors suspicious activities.
4. CrowdStrike Falcon
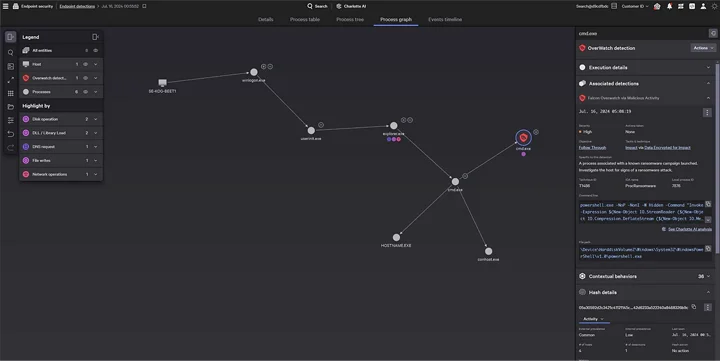
Falcon’s AI threat graph helps to block ransomware by means of behavioural EDR, where endpoint/ cloud signals are correlated for an early block. The independent rollback and the managed hunting are the two features that help to reduce the MTTR. Enterprise – grade XDR is best at hybrid environments, scoring identity risks with device context to drastically reduce false positives.
Key Features
- Behavioural Prevention and Rollback.
- Threat Hunting Integration.
- XDR across end points/ identity.
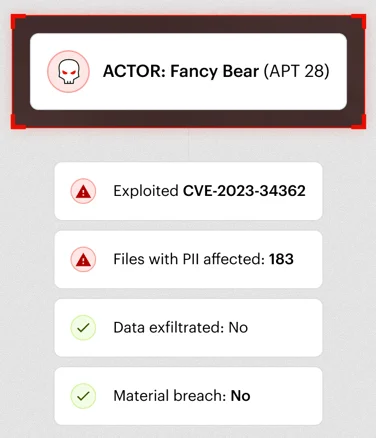
5. Microsoft Defender for Endpoint
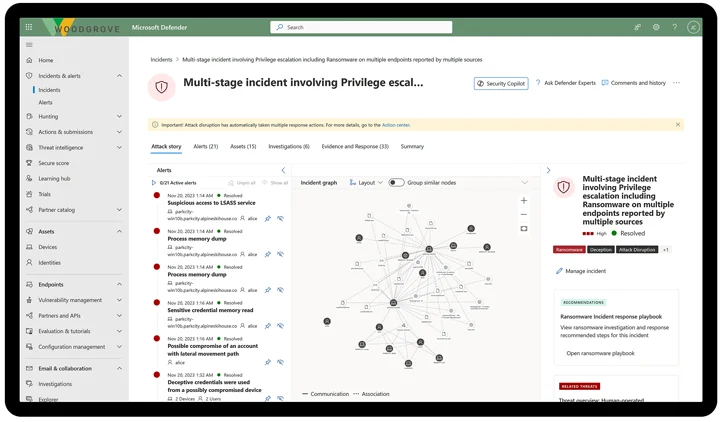
The tool from Microsoft is perfect for mid-to-large businesses that are looking for a unified endpoint security strategy integration across on-premises, cloud, and hybrid environments. The platform integrates advanced endpoint detection and response capabilities (EDR) with behavioral capabilities and threat hunting on a proactive basis. It also provides real-time attack surface reduction, automated investigation.
Key Features
- Behavioural Threat Protection.
- Automated Response and Remediation.
- Automatic Attack Disruption
6. Varonis
A data-driven security tool that works well for highly regulated sectors that already have a backup plan but require a strong reminder to prevent ransomware in advance. It keeps an eye on user behavior, accounts, and data from SaaS, cloud, and on-premises apps.
Key Features
- Data-Centric Threat Detection.
- Forensic and Investigation.
- Data Discovery and Mapping.
7. SentinelOne Singularity
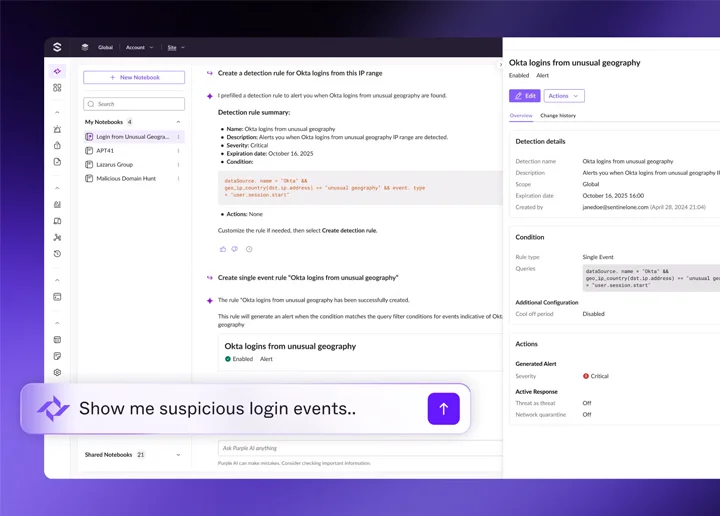
This tool utilizes artificial intelligence for fileless detection and storyline visualization, and automatically rolls back encrypted files. The ransomware scanner works as part of EDR to ensure total coverage. It stops the attacks by itself, most suitable for instant response without getting tired of analyst fatigue.
Key Features
- Storyline Attack Visualization.
- Autonomous Recovery.
- Deep learning Engine.
8. Acronis Cyber Protect
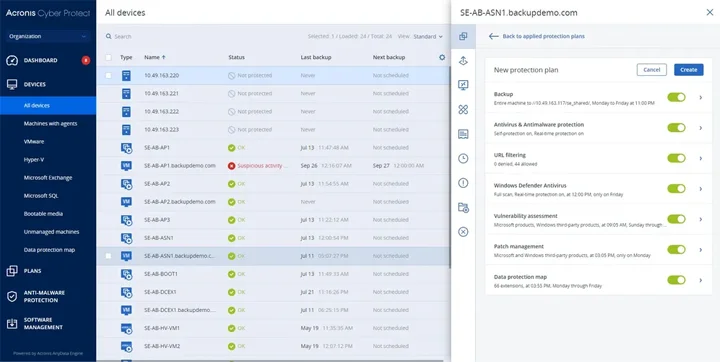
Acronis combines AI-powered threat detection, automated recovery, immutable storage, and backup. With a proactive approach to cyber resilience that stops malware attacks and facilitates speedy recovery, this technology is appropriate for companies looking for integrated cybersecurity and data protection on a single platform.
Key Features
- Forensic Backup
- One-click Recovery
- Immutable Cloud Storage
- Full Disk Encryption
9. Rubrik Security Cloud

It is a unified zero-trust data security solution that combines proactive anomaly detection methods with immutable backups, making it appropriate for mid-to-large businesses with substantial hybrid, multi-cloud data volumes. It offers end-to-end cyber resilience and is designed as a security-first platform rather than only a backup solution.
Key Features
- Sensitive Data Discovery.
- Automated Ransomware Investigation.
- Immutable Backups.
- AI-Driven Anomaly Detection.
10. Bitdefender GravityZone
GravityZone’s Ransomware Remediation is capable of decrypting files after a ransomware attack. The solution is complemented with NGAV and exploit defense. It can be used on endpoints without causing performance problems because it is sufficiently light. Effective multilayered ML block versions are available in the tool.
Key Features
- Auto-Decryption Remediation.
- Exploit Prevention
- Behavioral Analysis
Conclusion
Choose your tools according to the threat you face and the indications you collect. To identify behavioral trends early on, start by utilizing the platforms that gather endpoint identity and data access telemetry. Make sure the ones that have been cleaned are restored, stack your defenses with recovery capabilities that evolve from the ones that start the infection spread, and maintain compliance in high-stakes scenarios.
FAQs
Q1. What is a ransomware attack and how does it work?
Ans. Ransomware is a form of malware that encrypts data or disrupts access to systems, then demands payment (typically cryptocurrency) for restoration. It commonly enters environments through phishing emails, malicious links, compromised credentials, or unpatched vulnerabilities.
Q2. What are the early warning indicators of ransomware?
Ans. Early indicators often include abnormal file activity (mass renames, deletions, or encryption attempts), the appearance of ransom notes, unusual account behaviour or privilege changes, spikes in CPU or disk usage, and unexpected outbound network connections to unknown or untrusted IP addresses.
Q3. Which characteristics of ransomware tools are most important?
Ans. Effective ransomware defence requires early detection of abnormal behaviour, clear investigation context, and reliable recovery options. Real-time monitoring, identity and data activity visibility, and secure backups are all critical components of a resilient approach.
Q4. Do we need EDR for full ransomware protection?
Ans. EDR can help detect and contain ransomware at the endpoint level, but it is not sufficient on its own. It should be complemented by backup and recovery capabilities, as well as visibility into identity and data access to limit lateral movement and reduce overall impact.
Q5. Can ransomware be detected before files are encrypted?
Ans. In many cases, yes. Early stage indicators such as abnormal access patterns, mass file enumeration, unusual permission changes, or rapid identity-driven activity can appear before widespread encryption begins. Tools that monitor behaviour across identities, data access, and systems are better positioned to surface these signals early.
Q6. Why are backups alone not enough to defend against ransomware?
Ans. Backups are essential for recovery, but they do not prevent ransomware from spreading or limit operational disruption. Without visibility into how an attack occurred and which identities or data were involved, organizations risk reinfection, incomplete recovery, or restoring compromised data.
Q7. How does identity and access visibility help reduce ransomware impact?
Ans. Ransomware often exploits excessive permissions, compromised credentials, or lateral movement through directory services. Visibility into identity activity and access rights helps security teams quickly identify the source of an attack, limit its spread, and reduce the overall blast radius.



