



























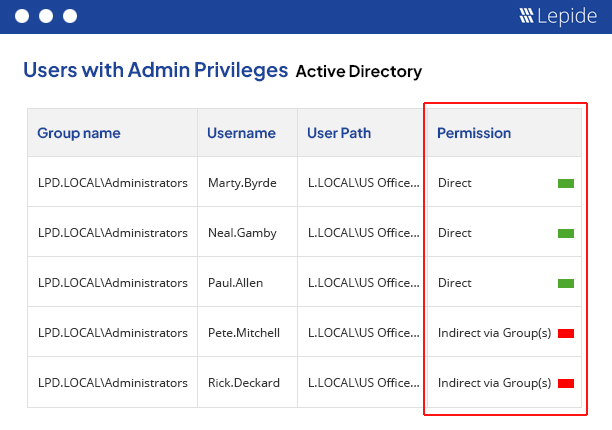
Identify over-permissioned users, inactive user accounts, and privileged access across your environment before personal, financial, customer, and operational data is exposed.
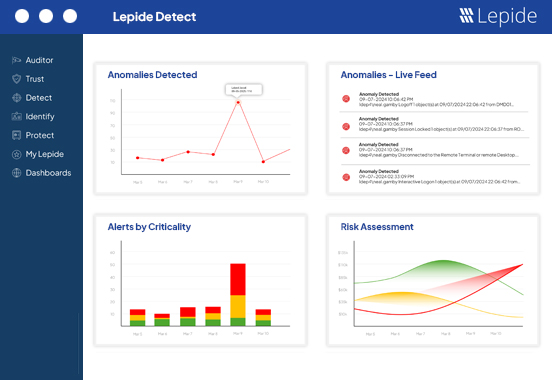
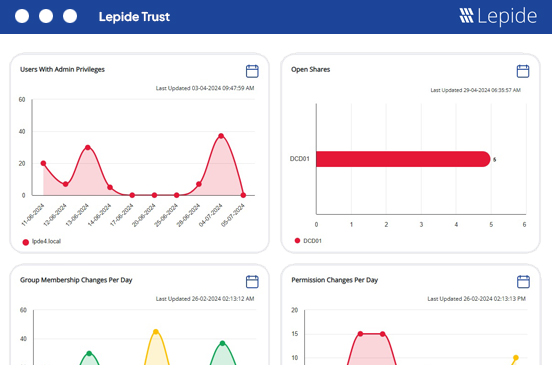
Track user behavior, permission changes, failed logons, and unusual access patterns in real time to detect threats earlier and accelerate investigations.
Monitor user activity, permission changes, and access to sensitive data across Active Directory, Microsoft 365, and hybrid environments by having clear visibility to support GDPR auditing and reporting requirements.
| GDPR requirement | Policy / section / article | How Lepide helps |
|---|---|---|
| Security of processing. | Article 32 | Monitor user activity, identify excessive permissions, and suspicious access to personal and sensitive data across hybrid environments. |
| Records of processing activities. | Article 30 | Maintain visibility into access to sensitive files, folders, and data repositories across Active Directory, Microsoft 365, and file servers. |
| Notification of a personal data breach. | Articles 33 & 34 | Detect suspicious behavior and accelerate investigations through centralized auditing and real-time alerts. |
| Integrity and confidentiality of personal data. | Article 5(1)(f) | Identify and automatically revoke excessive permissions, have visibility over inherited access, and privileged users to monitor and reduce unnecessary access to personal data. |
| Data protection by design and by default. | Article 25 | Strengthen least privilege policies and improve visibility into how sensitive data is accessed and used across hybrid environments. |
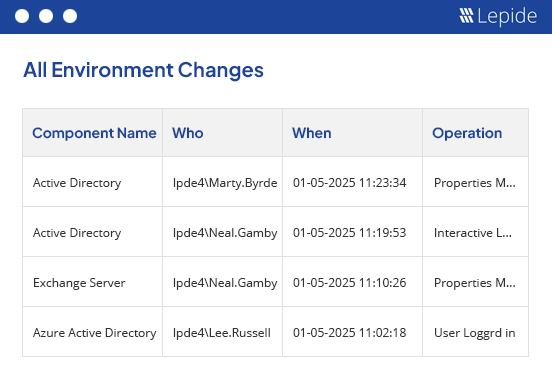
| Accountability principle. | Article 5(2) | Maintain searchable audit trails and centralized visibility into user activity, inactive users, permission changes, and access to sensitive data. |
| Access control and user accountability. | Articles 24 & 32 | Track privileged account activity, failed logons, and suspicious authentication behavior across Active Directory and Microsoft 365. |
Organizations handling personal and sensitive data must ensure that they have tools to monitor and revoke any excessive permissions. Clear visibility over their hybrid environments is essential to provide accountability and protect data. Lepide helps IT and security teams identify hidden access risks, monitor privileged users, and protect sensitive data across Active Directory, Microsoft 365, and file servers.
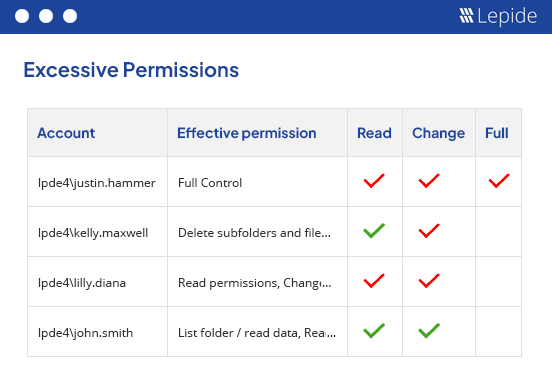
Understand exactly who can access personal, financial, customer, and operational data across your environment. Lepide helps organizations identify and automatically revoke excessive permissions, minimise unnecessary access, and strengthen least privilege policies without disrupting day-to-day operations.
Track user behavior including anomalous behavior, permission changes, failed logons, group membership changes, and unusual access patterns across Active Directory, Microsoft 365, and file servers through centralized auditing and real-time visibility.
Instantly investigate suspicious activity, privileged account misuse, and unauthorized access attempts through searchable audit trails, real-time alerts, and centralized visibility into user activity across hybrid environments.
Maintain visibility into user activity, permission changes, privileged groups, and access to sensitive data across Active Directory, Entra ID, Microsoft 365, and file servers to support GDPR auditing and accountability requirements.
Identify risky access patterns, excessive permissions, inactive user accounts, and suspicious behavior before they lead to unauthorized access or personal data breaches. Lepide helps organizations strengthen data protection controls and improve visibility into how sensitive data is accessed and used across hybrid environments.
From CISOs to SecOps teams, find out how the NIST Cybersecurity Framework is evolving and what you should be doing to achieve and maintain a compliant cybersecurity posture.
Get the free guide now!