Last Updated on May 23, 2025 by Deepanshu Sharma
Ransomware attacks often manifest with little to no warning, making them very difficult to defend against. Typically, a ransomware attack begins with an email attachment that is opened by a user, which subsequently triggers the malicious program to start encrypting files. However, despite the difficulty in thwarting these attacks, there are certain vulnerabilities and events that can be monitored, which can at least prevent them from spreading once they occur.
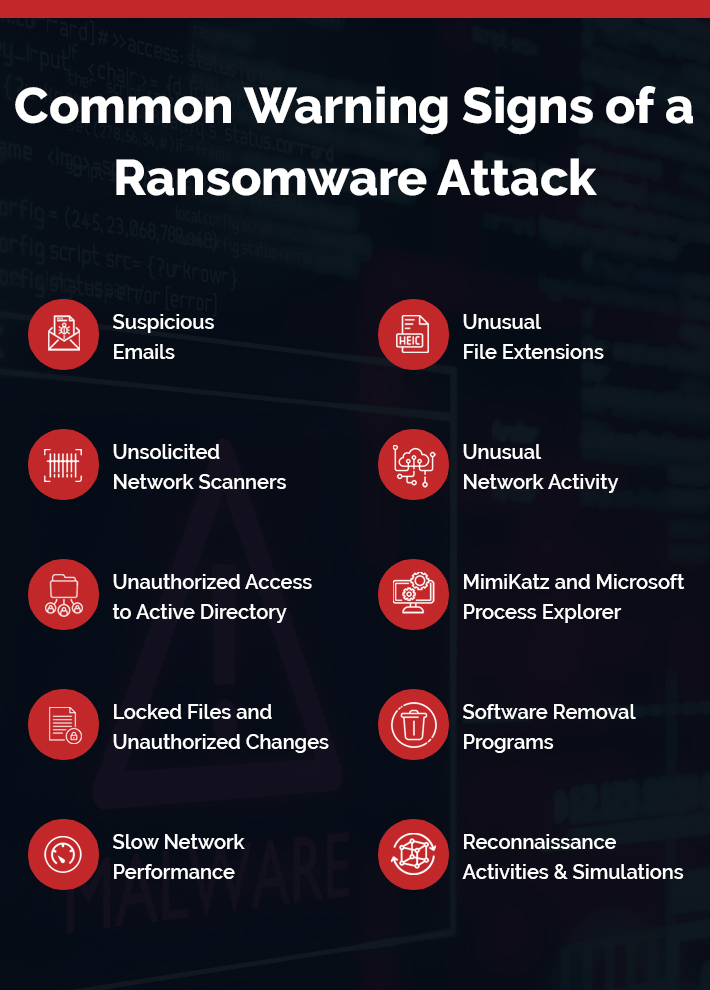
How do You Know if You Have Ransomware: Common Warning Signs
Below are the 10 most notable signs to watch out for that indicate a ransomware infection:
1. Suspicious Emails
Ransomware attacks often start with a phishing email, which has become a pervasive tactic in recent years. Phishing emails typically pose as genuine communications from reputable companies, that come with malicious attachments or links. Once unsuspecting users click on these attachments or links, hackers can gain a foothold within the network, allowing them to spread laterally and wreak havoc. However, by providing employees with comprehensive training, organizations can empower their personnel to recognize and detect these phishing scams, thereby triggering an early warning system that protects against potential attacks.
2. Unusual File Extensions
Files bearing unfamiliar extensions that seem to have been altered without authorisation are a telltale sign of a potential ransomware infection. This is often the result of the ransomware’s malicious activity, which involves modifying the file extensions of your valuable data, rendering it inaccessible without the decryption key, which is held by the attackers.
3. Unsolicited Network Scanners
While network scanners can be legitimate tools, they can also be used by hackers to infiltrate your system. This is particularly true if it’s installed on a server or lacks a clear purpose in your organization. Cybercriminals may exploit a vulnerability on a single computer to launch a ransomware attack, and then use the network scanner as a tool to gain access to other parts of your network. If your IT team is unable to identify a legitimate reason for a network scanner’s presence, it’s essential to conduct a thorough investigation and verify the scanner’s authenticity with your IT team.
4. Unusual Network Activity
Unusual network activity is an important sign of a potential ransomware attack. If you notice a high volume of outgoing traffic or suspicious connections, it’s possible that malware is communicating with command and control servers to receive instructions or transmit stolen data. Ransomware, in particular, often uses this strategy to receive instructions and updates from its creators. By monitoring your network activity with specialized tools, you can detect these unusual patterns and potentially catch the attack before it’s too late.
5. Unauthorized Access to Active Directory
When a hacker gains access to a company’s network, they will often attempt to exploit vulnerabilities in the Active Directory (AD) to gain domain-level access. To achieve this, they may use tools such as BloodHound, AD Find, and others. BloodHound, in particular, uses a tool called SharpHound, which can be delivered through various means, including a command-line executable or PowerShell script. The goal of SharpHound is to gather information about AD users, groups, and computers, as well as map pathways to escalate privileges to domain administrator-level access. Notably, notorious ransomware variants such as Ryuk have been used to exploit vulnerabilities in AD servers, with attackers leveraging the Microsoft Remote Desktop Protocol (RDP) to gain access. In one instance, Ryuk was used to insert ransomware into an AD logon script, which then infected every user who logged into the affected AD server.
6. MimiKatz and Microsoft Process Explorer
MimiKatz is a widely used open-source credential gathering tool, which is often used to extract passwords and login information. When paired with Microsoft Process Explorer, a legitimate tool that can dump sensitive Windows data, the potential for security breaches is heightened. Fortunately, penetration testing can help identify vulnerabilities and prevent attackers from exploiting MimiKatz. However, hackers may also employ more subtle methods to steal credentials, such as Cobalt Strike, which uses stealthy tactics to evade detection and mimic common tools like Gmail and Bing. This platform leaves an almost undetectable trail on infected systems, making it crucial for organizations to stay vigilant in their cybersecurity efforts.
7. Locked Files and Unauthorized Changes
One of the most notable signs of ransomware is the inability to access your files. Additionally, if you notice unauthorized changes to your files, such as unusual file extensions or modified file names, it could be a sign that your computer has been compromised by ransomware.
8. Software Removal Programs
Were an adversary to gain administrative access to your network, they will likely try to disable or remove any security software that will alert your security teams of their presence. They often use legitimate software removal tools, such as GMER, Process Hacker, IOBit Uninstaller or PC Hunter, to achieve this. A logging solution can detect the presence of these tools on the network, triggering a potential security threat. If these tools are detected, it is crucial to launch a thorough investigation.
9. Slow Network Performance
If your network’s performance suddenly takes a nosedive, it may be a sign of a ransomware infection. Since ransomware attacks encrypt a large number of files, they can also significantly affect your computer’s processing power. In some cases, the ransomware strain can be so resource-intensive that it can bring even the fastest machines to a grinding halt.
10. Reconnaissance Activities & Simulations
Adversaries will often conduct a series of reconnaissance missions before striking, running small-scale simulations of a ransomware attack to test their strategy and identify vulnerabilities in a target’s network or endpoints. Doing so will help them identify areas where they can improve their tactics and potentially exploit weaknesses in the system. These simulations may involve a limited attack on a small number of network devices, allowing the hackers to gauge their chances of success and, if necessary, adapt their approach to bypass security measures and achieve their goal.
Related Articles:
How Lepide Helps
While complete ransomware protection is impossible, identifying and closing security gaps can significantly reduce the risk of falling victim. The Lepide Data Security Platform can help you identify the early warning signs of a ransomware attack in the following ways:
Real-Time Threshold Alerting: Lepide’s solution detects ransomware attacks in real-time, allowing you to detect failed file reads and file renames, identify changes in user behavior, and receive alerts and trigger automate responses. For example, if X number of files have been renamed within Y seconds, a custom script can be executed which can disable a specific account or process, change the firewall settings, or shut down the affected server.
Identifying Inactive Users: Inactive users are often overlooked and become prime targets for cyber criminals. Lepide’s solution provides a report on inactive users, helping you reduce the number of potential accounts that can be compromised by ransomware.
Identifying Users with Excessive Permissions: Users with unnecessary access to sensitive data can enable the lateral spread of ransomware. Lepide’s solution identifies users with excessive permissions.
Detecting and Mitigating Open Shares: Open shares can be accessed by most users, making them vulnerable to ransomware attacks. Lepide’s solution provides a list of all open shares, enabling you to reduce the attack surface.
Maximizing Visibility and Response: The Lepide Data Security Platform allows you to generate detailed audit reports that provide valuable insights into your organization’s data security. These reports enable you to extract critical information for incident response.
If you’d like to see how the Lepide Data Security Platform can help to detect and respond to ransomware attacks, schedule a demo with one of our engineers.



