Last Updated on March 16, 2026 by Ashok Kumar
Another day, another data breach incident affecting sensitive patient information. This time, the victim was the Oklahoma State University Center for Health Sciences (OSUCHS) and the target nearly 280,000 Medicaid patients in Oklahoma. The most worrying part? Nobody seems to know what exactly happened.
This incident was first made public on January 5th but, a letter OSUCHS is using to send to affected patients makes clear that it was discovered in November of 2017:
![]()
This “hacking/IT incident” is by far the largest that has been reported in 2018 on the HHS HIPAA Breach Reporting Tool website and the fourth largest breach of its kind since the beginning of 2017. This reinforces a worrying trend we are seeing that these types of incidents are becoming more frequent and affecting more people each year.
What the Notification Letter Tells us
The notification letter OSUCHS is using to inform affected patients of the breach makes it clear that someone was able to gain unauthorized access to folders containing Medicaid patient billing information. The intruder is being labelled, quite generically, as a “third-party”.
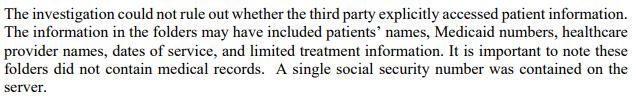
OSUCHS then took steps to remove the folders from the network and hired a third-party data security firm to look into the incident. Here’s what they concluded:
What’s really telling in the notification letter, is that no information is given as to who the third-party intruder might be. However, our experience with similar such incidents leads us to believe that the most likely explanation is an unauthorized insider as opposed to an external hacker. This is, of course, simply speculation at this point.
Countless times we have seen that organizations in the healthcare sector still do not have a tight enough grasp on their PHI. They simply do not know where it is, who has access to it or when it is copied, modified, moved or deleted. This lack of visibility means that an insider with legitimate access can take advantage of moving unseen in folders and making unauthorized changes.
What Can We Learn from This?
Whether this turns out to be an insider threat or an external hack, the lesson is still the same; know what’s happening with your PHI!
It’s simply too easy at the moment for ill-intentioned people to gain access to sensitive data and healthcare organizations don’t know enough about unauthorized events taking place in their network until after the fact.
The answer seems simple to us; better auditing and monitoring of the activity of your privileged users.
Lepide Data Security Platform provides a solution to many of the problems faced in the healthcare industry today, including HIPAA compliance and the protection of PHI. It enables you to audit, monitor and alert on critical changes taking place across files and folders (along with a myriad of other on-premises and cloud platforms). You can also track permissions and permission changes to help maintain the policy of least privilege.
To find out more about how Lepide Data Security Platform helps organizations in the healthcare industry secure PHI and meet HIPAA compliance, click here.



