Last Updated on April 15, 2026 by Satyendra
Organizations evaluating data security platforms often encounter the same challenge: gaining clear visibility into sensitive data without introducing unnecessary operational complexity.
Two platforms frequently considered in this space are Lepide Data Security Platform and Varonis Data Security Platform. Both solutions focus on helping organizations understand who has access to sensitive data, how that data is being used, and where security risks may exist.
However, the way each platform approaches these goals is slightly different. While Varonis is known for its broad data security ecosystem, Lepide focuses on delivering practical visibility, auditing, and remediation capabilities that security teams can deploy and operate efficiently.
Understanding these differences can help organizations determine which platform aligns better with their security strategy and operational constraints.
Lepide vs Varonis: Key Capability Comparison
Both Lepide and Varonis address many of the same core data security requirements. The table below highlights areas where the platforms overlap.
| Capability | Lepide Data Security Platform | Varonis Data Security Platform |
|---|---|---|
| Primary focus | Unified data security platform focused on auditing, permissions governance, threat detection, and compliance reporting across identity and data environments | Unified data security platform designed to discover sensitive data, classify it, and enforce policies to prevent breaches |
| Data activity monitoring | Tracks file activity such as file creation, access, modification, copying, and deletion across file servers and directories | Monitors and queries enterprise data activity across cloud, SaaS, and on-prem data stores |
| Permissions analysis | Analyzes permissions across identities and data stores to identify excessive access and permission changes | Analyzes permissions across identities and data stores to identify excessive access and permission changes |
| Threat detection | Detects insider threats, compromised accounts, and abnormal user activity | Detects malicious insiders, abnormal behavior patterns, and data exposure risks |
| Behavior analytics | Monitors user behavior patterns and highlights anomalies through analytics and alerts | Uses data-centric UEBA and telemetry to detect suspicious behavior |
| Automated remediation | Automates permission remediation and response workflows to reduce risk exposure | Automates policy enforcement and removes excessive permissions |
| Sensitive data discovery/classification | Provides sensitive data discovery and classification with predefined criteria sets to identify regulated data | Automatically discovers and classifies sensitive data across cloud and SaaS environments |
| Compliance support | Provides audit trails, dashboards, and compliance reports aligned with frameworks such as HIPAA, SOX, PCI DSS, and GDPR | Provides audit trails, dashboards, and compliance reports aligned with frameworks such as HIPAA, SOX, PCI DSS, and GDPR |
| Hybrid environment coverage | Covers Active Directory, file servers, Microsoft 365, Active Directory, File Server (IWindows, Nutanix,Nasuni etc) , Microsoft 365, Amazon S3, Google Workspace, and other hybrid environments | Covers multi-cloud, SaaS applications, enterprise data repositories, and collaboration platforms |
| Deployment model | On-premises, cloud, and hybrid deployments with centralized monitoring | Cloud-native data security platform with SaaS integrations |
| Pricing model | Licensed in packages (Core, Plus, Advanced) priced per user per supported platform | Licensed in packages (Core, Plus, Advanced) priced per user per supported platform |
| Platform objective | Provide visibility, auditing, permissions governance, and threat detection in a unified operational platform | Provide visibility, auditing, permissions governance, and threat detection in a unified operational platform |
Architecture Overview: How the Platforms Monitor Data
Understanding how each platform operates helps explain why organizations sometimes prefer Lepide as an alternative.
Both tools collect activity data from identity systems and data repositories, analyze user behavior, and generate alerts. The difference lies in how the platforms structure these workflows.

Lepide focuses on continuous auditing and operational visibility across identity systems and file environments. Security teams can quickly determine:
- Who accessed sensitive files
- What permissions changed
- Whether user behavior appears suspicious
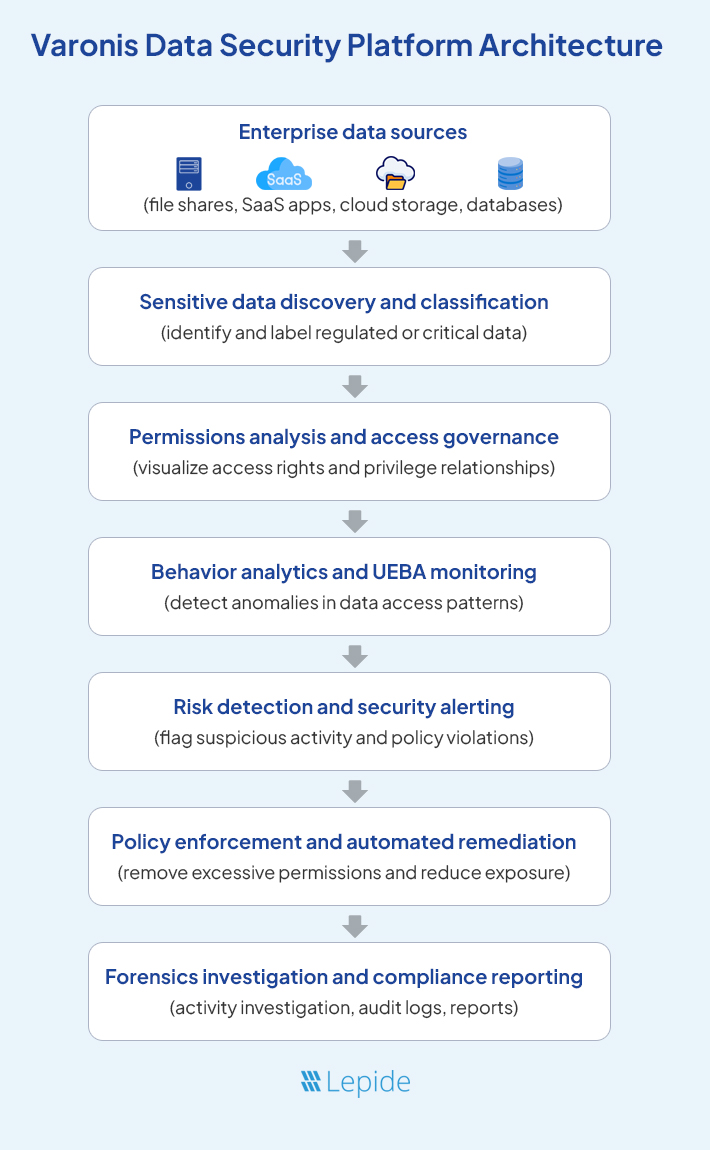
Varonis emphasizes data discovery, classification, and governance. The platform scans enterprise environments to identify sensitive data and analyze access rights before enforcing policies that reduce exposure.
This tool is powerful for organizations implementing large-scale data governance programs. However, the discovery and classification processes can add additional layers to deployment and configuration.
Visibility into Data Activity
Visibility into data access is one of the most important capabilities of a data security platform
Security teams frequently need to answer questions such as:
- Who accessed a sensitive file?
- When was the file modified?
- Which permissions changed recently?
- Is a user suddenly accessing large amounts of data?
Lepide focuses strongly on auditing these events across identity systems and data environments. Its file server auditing functionality tracks file activity including creation, access, modification, copying, and deletion.
This allows security teams to investigate suspicious behavior and identify changes that may introduce risk.
Varonis also provides deep visibility into data activity by monitoring user interactions with enterprise data repositories. Its analytics engine analyzes these events to detect abnormal behavior patterns.
Both platforms, therefore, provide strong visibility into data activity. The difference typically lies in how quickly organizations can operationalize these insights.
Why Organizations Evaluate Lepide as a Varonis Alternative
Both platforms clearly address the same core problem: protecting sensitive enterprise data.
However, their design priorities differ.
Varonis positions itself as a comprehensive data security ecosystem centered around data discovery, classification, and governance.
Lepide focuses more directly on operational visibility into identity systems, file activity, and permissions, allowing security teams to investigate and respond to risks quickly.
For many organizations, this operational focus can make Lepide an attractive alternative when evaluating solutions similar to Varonis.
1. Simpler Deployment and Lower Operational Overhead
Operational overhead refers to the time, expertise, and resources required to deploy and maintain a data security platform. Lepide is designed with a lightweight architecture and prescriptive configuration options that help organizations begin monitoring identity and data activity quickly.
In practice, teams typically:
- Deploy: Install the Lepide server and connect identity systems and data stores such as Active Directory, file servers, and Microsoft 365.
- Configure: Enable auditing, permissions analysis, and alerts using built-in configuration options.
- Monitor: Use dashboards to track excessive permissions, inactive accounts, and suspicious activity.
- Maintain: Manage monitoring and reporting from a centralized platform rather than multiple tools.
For organizations with lean security teams, this approach reduces operational effort while accelerating visibility into potential risks.
2. Cost-Effectiveness for Mid-Market and Enterprise Organizations
When evaluating Varonis, organizations must consider not only features but also long-term operational cost.
Total cost typically includes licensing, infrastructure requirements, deployment effort, and ongoing management.
Lepide’s licensing model allows organizations to align their investment with the environments they want to monitor. When assessing cost-effectiveness, teams typically evaluate:
- Licensing model: how predictable pricing scales with the environment.
- Infrastructure requirements: resources required to deploy and maintain the platform.
- Operational staffing: the expertise needed to operate the solution.
- Maintenance effort: how much tuning and rule management is required over time.
This approach allows organizations to implement strong data security controls without introducing unnecessary operational complexity.
3. Focused Auditing and Compliance-Driven Reporting
Lepide is built around targeted, high-fidelity audit trails and reports that map directly to regulatory mandates, what we call compliance-driven reporting. That means prebuilt reports and alerts aligned to HIPAA, PCI DSS, SOX, GDPR, and more, so security and compliance teams can demonstrate control maturity with less manual effort. Peer reviews regularly point to the depth and practicality of our auditing, particularly for change tracking and access monitoring across AD, file systems, and Microsoft 365.
Common frameworks and out-of-the-box coverage:
- GDPR: Data access, permission changes, data movement by user/object
- HIPAA: ePHI access patterns, anomalous read spikes, privileged user actions
- PCI DSS: File integrity monitoring, cardholder data access, policy violations
- SOX: Privileged group changes, segregation-of-duties exceptions, control attestations
- ISO 27001/NIST: Control-aligned event tracking, audit readiness dashboards
Reports and alerts feed directly into response workflows, enabling ticket generation, triggering automated remediation, and providing evidence trails for auditors without requiring additional tooling.
4. Practical Anomaly Detection and Automated Response
Large environments generate enormous volumes of activity data, making manual analysis difficult.
Lepide uses behavioral analytics and anomaly detection to identify activity that deviates from normal patterns, such as unusual file access, unexpected permission changes, or suspicious login behavior.
When anomalies occur, security teams can:
- Investigate activity through detailed audit logs
- Review contextual information about the user or system involved
- Remediate risk by adjusting permissions or disabling accounts
- Document incidents using audit-ready reports
This workflow allows organizations to move quickly from detection to investigation and response.
5. Seamless Support for Hybrid On-Premises and Cloud Environments
Most organizations operate hybrid environments that combine on-premises infrastructure with cloud services.
Typical environments include:
- Identity systems such as Active Directory or Entra ID
- File storage platforms such as Windows File Servers or NAS
- Cloud collaboration services such as Microsoft 365
Lepide provides centralized visibility across these environments, allowing security teams to monitor identity activity, file access events, and configuration changes from a single console.
This unified monitoring helps reduce blind spots and maintain consistent security policies across hybrid environments.
6. Targeted Governance Without Excessive Complexity
Varoniis includes complex governance frameworks that require significant configuration.
Lepide focuses on practical governance capabilities that help organizations enforce least-privilege access while maintaining operational simplicity. These include:
- Visibility into permissions across users and groups
- Access reviews and entitlement validation
- Monitoring of privileged accounts
- Change tracking for files, folders, and identity objects
These capabilities help organizations maintain tighter control over sensitive data without introducing unnecessary governance complexity.
If Varonis feels like too much for what you actually need, Lepide might be exactly the fit. Schedule a demo today and see the difference yourself.



