Last Updated on January 2, 2025 by Satyendra
Have you ever received a SOC audit request and wondered where on earth to start? Maybe you’re even performed SOC audits in the past, but you weren’t thrilled with the results. Either way, it’s always a good idea to brush up on the requirements for SOC audits and how best to prepare for them.
In this blog, we will go through what is required from SOC 1, SOC 2 and SOC 3, whether your organization needs a SOC audit and a checklist for preparing for one.
What is a SOC Audit?
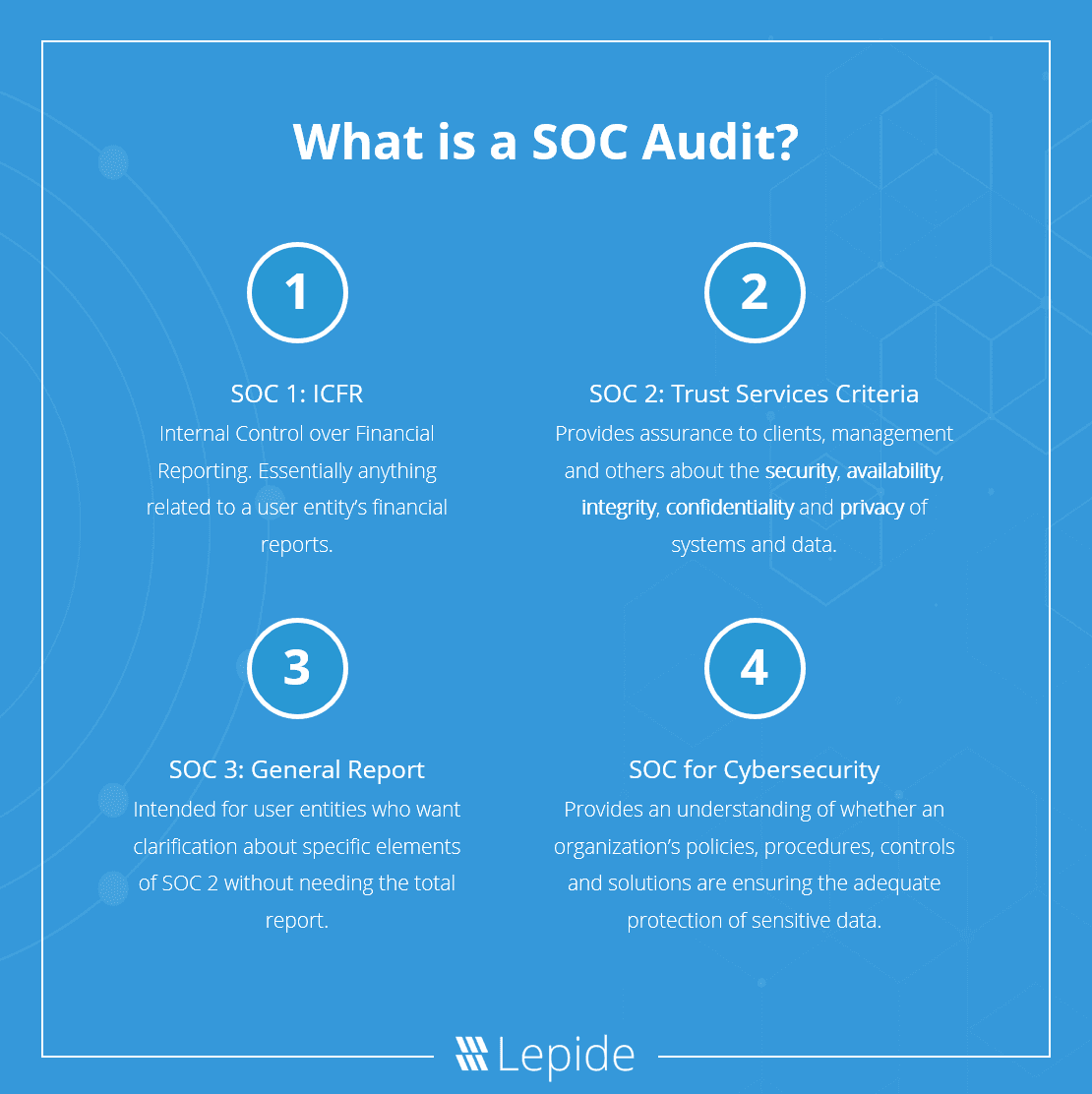
Service organizations bear multiple responsibilities concerning different aspects of the business to clients. SOC (System and Organization Controls) audits are designed to help fulfill specific client or user entity requests which may come in the form of SOC 1, SOC 2 or SOC 3.
Specifically, SOC for cybersecurity is a reporting framework to help organizations provide relevant information about the effectiveness of their cybersecurity policies and procedures. CPAs can report on this kind of information to meet the cybersecurity needs of a wide range of stakeholders.
What is SOC 1 (SSAE 18): ICFR?
The SOC 1 (SSAE 18) audit relates to Internal Control over Financial Reporting (ICFR) as it relates to the Standards for Attestation Engagements 18. Essentially, anything related to a user entity’s financial reports will be included in a SOC 1 audit.
There are two separate reports available for a SOC 1 audit:
- The Type 1 report will show you whether your auditor believes that your systems are suitably designed to achieve the desired objectives on that date.
- The Type 2 report expands upon the Type 1 report, focusing on proving that your security controls are effective over a specific time period.
What is SOC 2: Trust Services Criteria?
If your organization outsources technological and data-related services (including data hosting, colocation, data processing or SaaS), then a SOC 2 audit is likely to be used. The SOC 2 report is designed to provide assurance to the organization’s clients, management and user entities about five key trust services criteria:
- Security: Ensuring that the information and systems are protected against unauthorized access, breaches, data leakage, and anything else that could affect the integrity, confidentiality and privacy of information.
- Availability: Ensuring that information and systems are available for use and meeting the entity’s objectives.
- Integrity: System processing is valid, accurate and timely enough to meet the entity’s objectives.
- Confidentiality: Information that is deemed to be confidential is protected appropriately.
- Privacy: Personal information is collected, used, retained, disclosed and disposed of appropriately.Genera
SOC 2 audits can take place at a specific time and date or can be carried out over a period of time. A SOC 2 audit report typically includes opinions, assertions, detailed descriptions of the services or systems, details of the security controls and the results of testing.
What is SOC 3: Trust Services Criteria for General Use Report?
The SOC 3 report essentially provides information to user entities who need clarification about certain sections of the SOC 2 report, but do not need the whole SOC 2 report. SOC 3 reports are similar to SOC 2 but are intended for a general audience that wish to understand the trust service principles.
What is SOC for Cybersecurity?
SOC for Cybersecurity is the newest addition made by the AICPA (American Institute of Certified Public Accountants). SOC for Cybersecurity examinations determine how a CPA can report on the cybersecurity risk management program of service organizations.
The report will provide an understanding of whether an organization’s policies, procedures, controls and solutions are adequately ensuring the protection of sensitive data.
Preparing for a SOC Audit Step by Step
Now that you have a basic understanding of the different types of SOC audit available and the reports you may need, you can start to prepare. Preparing for a SOC audit can be broken down into five quick steps:
- Choosing the report
- Defining the scope of the audit
- Understanding regulatory compliance
- Defining policies
- Perform a risk assessment
1. Choosing the report
Depending on the objectives of your SOC audit, you will want to ensure that you choose the correct report for your requirements and the requirements of your customers. Commonly, SOC 1 is the most widely used report, but SOC 2, SOC 3 and SOC for Cybersecurity provide significant value.
If you want to determine something specific about your financial controls, then a SOC 1 report would be the most appropriate. If a user entity has raised concerns about the security of their data, then you will most likely require a SOC for Cybersecurity audit.
2. Defining the scope of the audit
There are a number of questions you need to be asking internally to determine the scope of the SOC audit. Some of those questions could include what services you need the audit for, what systems will be involved, what locations those services are provided from and who the report is intended for.
Service organizations that specialize in a particular service will find that their scope is fairly defined. Complications may arise for organizations that offer a wide variety of services over numerous locations using multiple systems. In these cases, it is often found that organization produce separate SOC reports for each of the services they provide.
3. Understanding regulatory compliance
In addition to SOC reports, service organizations may well be required to demonstrate adherence to one or multiple compliance requirements. Depending on the industry, type of organization and location, you may be bound by PCI DSS, HIPAA, GLBA or any number of compliance mandates that require reports.
Organizations should consider deploying technology that allows you to produce compliance-ready reports for these mandates, as well as for SOC, from a single vendor to save money and improve the efficiency of reporting.
4. Defining policies
Ensuring that you have a well defined and written set of policies and procedures for compliance with SOC audits. Written policies are what SOC audits will refer to when conducting your audit, and written policies will also be helpful internally when referring to standards and expectations for compliance.
5. Perform a risk assessment
It’s time to determine internally whether you are prepared for your SOC audit. Performing a risk assessment will help you identify areas that you may want to address before your SOC audit, including where security controls should be tightened and whether there are any immediate threats to data security.
You can attempt to perform a risk assessment internally if you have the adequate people and technologies in place. However, most organizations find it easier to outsource their risk assessments to third party data security specialists.
How Lepide Can Help You Prepare for Your SOC Audit
Lepide have a proven methodology for helping organizations prepare for their SOC audits by helping to understand how effective your current security controls are and generating pre-defined reports that help to speed up and improve the accuracy of audits.
Lepide can help you understand if you are compliant with any compliance regulation that applies directly to your business. If you would like to see how Lepide can help you prepare for your SOC audit, contact one of our experts today.



