Last Updated on January 14, 2025 by Deepanshu Sharma
A blast radius refers to the overall impact of a potential security incident. In other words, it is an assessment of the amount of damage that could be caused were an intruder to compromise a privileged account on your network.
Naturally, if an account with admin or root-level privileges were to be compromised, the amount of damage that could be caused would be much greater as the attacker will have the ability to move laterally across your network, potentially elevating their privileged if necessary.
The blast radius is generally a lot bigger in the cloud. This is largely because companies tend to assume that cloud servers are secure by default. However, this is rarely the case. For example, a large number of data breaches have been caused by Amazon S3 storage buckets that were exposed to the public by default.
How to Determine Your Blast Radius
There’s no single formula to determine the blast radius of a security threat, as different threats will have a unique impact on your system. There are, however, some guidelines to follow when attempting to assess the amount of damage that could be caused by a given threat. As a starting point, you should consider the following:
Customer impact: This includes the overall number of customer accounts that could be affected by a given security incident.
Functionality: How the functionality of accounts and processes will be affected by a given security incident.
Location: What systems and data will be affected by a given security incident? For example, an incident may only affect a single server, or it could spread to other systems, and even other regions.
How to Reduce Your Blast Radius
As they say, it’s not the case of if, but when, a data breach will occur. And let’s face it, anything that can go wrong will go wrong. As such, it is imperative that you plan ahead to limit the amount of damage that could be caused by a security incident. Below are some tips to help you minimize the blast radius of a security threat:
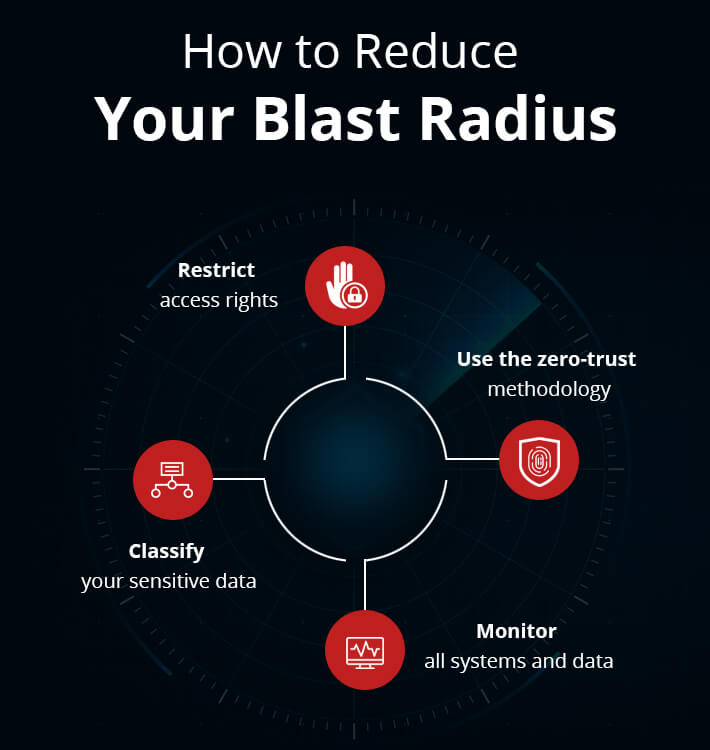
Classify your sensitive data
Use a data classification solution to automatically scan your repositories, both on-premise and cloud-based, and classify sensitive data as it is found. Knowing what sensitive data you have, and where it is located, will make it easier to assign the appropriate access controls.
Restrict access rights
Always adhere to the principle of least privilege, which ensures that accounts are granted the least privileges they need to carry out their role. Consider implementing Role-Based Access Control (RBAC) which will make it easier to establish a clear separation of duties. With RBAC, roles are set up for different purposes, each with its own set of privileges. Accounts are assigned to these roles, as and when required.
Use the zero-trust methodology
Zero-trust is a security model which assumes that adversaries already have access to your network. As such, you should never automatically trust an account, but instead, request verification anytime an account needs to access critical systems and data. This will help to prevent an adversary from moving laterally across your network.
Monitor all systems and data
You need as much visibility as possible into where your data resides, who has access to it and from where. You will also need to establish a baseline of normal activity in order to identify anomalies. Anytime sensitive data is accessed, moved, modified, shared, or removed, the security team must be informed, in real-time. You will also need to flag suspicious activity, such as failed logon attempts, unusual logon times and locations, repetitive file requests, and more. Some sophisticated real-time file auditing software is able to detect and respond to events that match a pre-defined threshold condition. For example, if x number of files are copied or encrypted within a given time frame, a custom script can be executed to prevent the potential attack from spreading.
How Lepide Can Help Reduce Your Blast Radius
The Lepide Data Security Platform enables organizations to better understand and limit the blast radius of a threat. Using Lepide, organizations can identify where their most sensitive data is located, what the data actually is, and how much of it they have. Lepide then analyses effective permissions to determine who has both direct and indirect access to that data, how it is being granted, and when access rights change. This helps organizations to understand whether their current access rights are aligned with a zero-trust model. Additionally, Lepide can suggest whether users’ permissions are “excessive” based on their data usage patterns.
If an incident does occur, Lepide can detect it in real-time using any number of pre-defined threat models, and initiate threat responses that contain the blast radius. Detailed audit trails provide excellent investigation capabilities so that you can determine what the affected user or account had access to, what they were doing with data, and more.
If you’d like to see how the Lepide Data Security Platform can help you minimize your blast radius, schedule a demo with one of our engineers.



