How We Simplify IT Operations
LepideAuditor helps simplify the daily tasks of the IT team by automating what would otherwise be time-consuming and manual tasks.
Start My 15-Day Free Trial
- Home |
- LepideAuditor |
- IT Operations
IT Operations
LepideAuditor helps you overcome many of the limitations associated with manually auditing changes to key data and infrastructure. IT teams in large organizations can quickly find themselves overwhelmed with helpdesk calls for menial tasks; wasting time, money and resources. LepideAuditor helps to automate the troubleshooting of user management issues, whilst also helping IT teams maintain consistent access to systems and data.

How We Help in Streamlining IT Operation
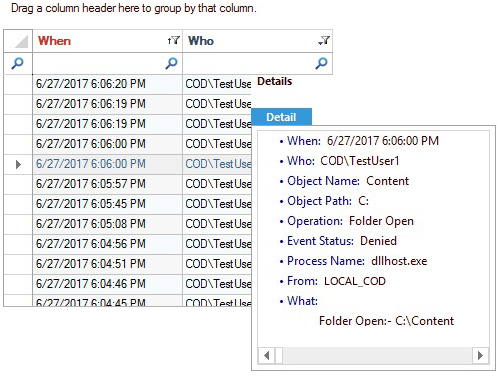
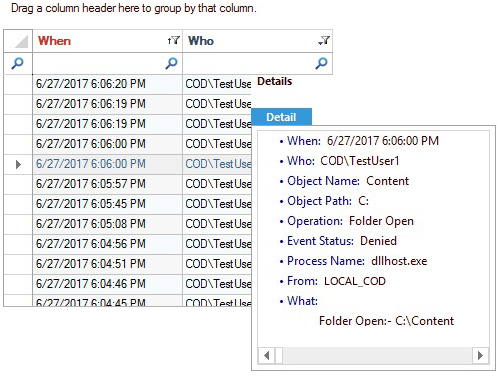
Maintain Access to Systems and Data
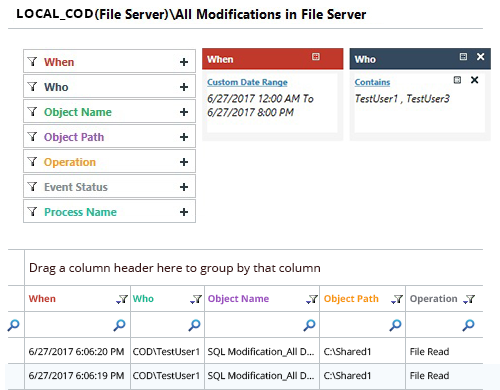
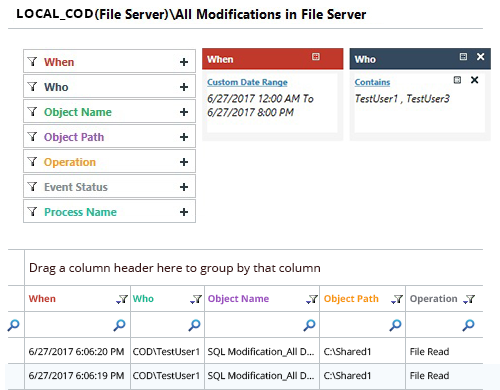
- Determine who is accessing your data to spot whether unauthorised activities are taking place that could result in downtime
- Help ensure the integrity of Exchange Server through auditing who is accessing your mailboxes and reading critical emails
- Get notified of any permission changes taking place in Active Directory, File Server and Exchange Server
- Determine who is actually logging onto and off of your critical systems; including failed logon attempts
- Restore unwanted changes in a matter of clicks, helping you to reverse any potentially damaging changes that have taken place
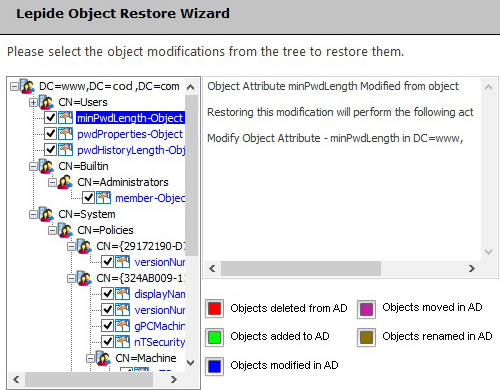
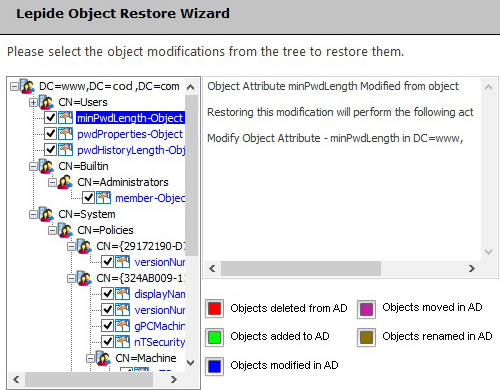
Roll Back Unwanted Changes
- Regularly capture backup screenshots of the states of Active Directory Objects and Group Policy Objects
- Roll back changes in seconds from Active Directory and Group Policy reports
- Restore deleted objects that are in a “Tombstone” state, as well as Active Directory Objects that are neither in “Tombstone” nor “Logically Deleted” states
- Reverse unauthorised or potentially damaging changes to Group Policy
- Generate reports on the previous state of Active Directory and Group Policy; including objects, permissions, audit settings and object ownership
Troubleshoot User Management Issues
- Determine when unauthorized activities are taking place in critical servers through logon/logoff reports
- Ensure that privileges haven’t been awarded to users that have no need for them through detailed permission audit reports
- Notify users periodically when passwords are due to expire to reduce helpdesk calls
- Clean-up inactive accounts regularly and automatically to ensure that they are not leveraged for nefarious purposes
- Check the status of user accounts in real time and unlock accounts easily to get one step ahead of potential issues
- Delegate tasks such as unlocking accounts, resetting passwords etc. to users to save time
❝
LepideAuditor is simple to install and setup and is an easy-to-use solution for auditing your IT environment.
Ahmed Nabil


❝
LepideAuditor takes the strain out of change auditing and regulatory compliance with one of the most comprehensive solutions on the market.
IT Security Guru


❝
It’s rare to find a solution which covers a such a wide range of auditing services, but ‘LepideAuditor’ is one of those rare exceptions.
Mahdi Tehrani

Active Directory Lead
❝
LepideAuditor is one of the most simple to use and feature-packed security suite for Microsoft-based environments. If you fear security breach, this is one of the most essential security perimeters.
Erik Blum


❝
LepideAuditor is an excellent audit solution. It gives IT teams complete information about what’s happening in the IT systems, the health of their servers and backup history.
Prajwal Desai


❝
The LepideAuditor is an invaluable toolset for any System Admin to audit Active Directory, Group Policy and Exchange server changes.
Marius Ene


❝
I really enjoyed the way LepideAuditor performs to audit the changes made to Active Directory and Group Policy Objects. I will certainly recommend it to anyone who is looking for an easy-to-use third party auditor.
Roman Nedzelský


❝
LepideAuditor is highly recommended as it not only meets all requirements for Active Directory and Group Policy change auditing but also it is easy and friendly to use.
Roberto Di Lello


❝
LepideAuditor is an excellent auditing solution. Some key features of the solution are compliance reports, health monitoring, alerts/notifications and the backup/restore functionality.
Mayank Dhama

IT Expert
❝
LepideAuditor honored as Gold winner in the 12th Annual 2016 Info Security PG’s Global Excellence Awards® in ‘Auditing’

❝
LepideAuditor is a solid product that will likely do a good job for anyone who wants to know what administrative actions are being taken in their organization.


❝
LepideAuditor received a gold certification in data loss prevention.


❝ LepideAuditor has brilliant search capabilities and was easy to use from the perspective of a non-technical end user – highly recommend it.❞

❝ LepideAuditor provided us with complete visibility over what was happening in our IT environment in a simple, cost-effective and scalable way.❞

❝ We're very pleased with how much more insight LepideAuditor gave us and impressed with the attentive customer service they provided.❞

❝ LepideAuditor takes the strain out of change auditing and regulatory compliance with one of the most comprehensive solutions on the market. ❞

- Support
- |
- +1-800-814-0578
- |




