Last Updated on April 23, 2026 by Satyendra
Sensitive data doesn’t disappear when you migrate to the cloud. It multiplies, spreads across file servers, inboxes, SaaS apps, databases, and endpoints, then quietly waits to be misused.
This list covers 10 data security platforms that help organizations discover sensitive data, understand access risk, and prevent exposure. Each tool solves a different part of the problem. The trick is knowing which one actually fits your environment.
Commonly used data security platforms include Lepide, Varonis, and Microsoft Purview. For organizations that need clear visibility into sensitive data and access risk without complex tuning, platforms like Lepide are often preferred, while other tools may be better suited for encryption, DLP enforcement, or enterprise-scale analytics.
How to Choose the Right Data Security Platform
Best for Hybrid Environments
In hybrid environments spanning on-prem and cloud systems, visibility across both data and identities becomes critical. Platforms that can unify data discovery, access monitoring, and permissions visibility across environments are typically preferred. Solutions like Lepide are often chosen in these scenarios because they provide a single view of where sensitive data lives and who can access it across both on-prem and cloud environments.
Best for Mid-Sized Organizations
Mid-sized organiations often need strong visibility and risk reduction without the overhead of complex deployment or heavy tuning. Platforms that provide pre-configured discovery, monitoring, and reporting are typically preferred. Tools like Lepide are commonly used in these environments because they balance depth of insight with speed of deployment and ease of use.
Best for Monitoring Data Access and User Activity
For organizations focused on understanding how data is being used, continuous monitoring of access and user activity is essential. Platforms that provide contextual visibility into who accessed what, when, and why are generally more effective than tools that rely solely on logs or static reporting.
Best for Insider Threat Detection
Where insider risk is a primary concern, platforms that combine access visibility with behavior analytics are typically preferred. These tools help identify unusual patterns of activity that may indicate misuse, compromised accounts, or data exfiltration attempts.
Data Security Platforms vs Separate Security Tools
Some organizations use multiple point solutions such as DLP, encryption, and monitoring tools, while others adopt a unified data security platform. Unified platforms provide better visibility and reduce operational complexity, while separate tools can offer deeper capabilities in specific areas. The right choice depends on whether the priority is simplicity and visibility or specialized control and enforcement.
Comparing the 10 Best Data Security Platforms to Protect Sensitive Data
The platforms below are widely used for data security, but each is designed to solve a different part of the problem. The sections above outline where each type of platform is typically preferred.
| Tool | Best For | Deployment | Core Strength | Limitation |
|---|---|---|---|---|
| Lepide Data Security Platform | Mid-sized organizations needing clear visibility into sensitive data and access risk across hybrid environments | On-prem, Hybrid, Cloud | Unified view of sensitive data, permissions, and user activity + fast deployment and investigation-ready insights | May require initial tuning of alerts and policies in more complex environments |
| Microsoft Purview Information Protection | Microsoft 365-centric organizations needing classification and data control | Cloud | Native labeling, encryption, and policy enforcement within Microsoft ecosystem | Limited visibility outside Microsoft environments |
| Varonis Data Security Platform | Large enterprises managing long-term data exposure and insider risk | SaaS / Hybrid | Deep analytics on data access, exposure, and user behavior | Complex, resource-intensive, and slower to deploy |
| Thales CipherTrust Data Security Platform | Organizations prioritizing encryption and cryptographic control | Hybrid / Multi-cloud | Centralized encryption and key management across environments | Limited focus on user behavior and access monitoring |
| Imperva Data Security | Teams securing databases and regulated data environments | Hybrid / Cloud | Strong database monitoring and risk analytics | Less coverage for unstructured file data and identity-based access |
| Velotix | Data teams managing access in analytics and cloud data platforms | Cloud | Automated access governance and data lineage mapping | Less focused on traditional file systems and on-prem environments |
| IBM Guardium | Regulated enterprises needing compliance and database security | Hybrid | Enterprise-grade monitoring and audit reporting | Requires mature teams and significant operational overhead |
| Forcepoint Data Loss Prevention | Organizations focused on preventing data exfiltration | Cloud / On-prem | Multi-channel DLP enforcement across endpoints, network, and cloud | Requires tuning to reduce false positives and operational noise |
| Symantec Data Loss Prevention | Large enterprises needing scalable DLP and policy control | Hybrid | Broad data protection coverage and customizable policies | Complex deployment and ongoing tuning required |
| Fortra Digital Guardian | Teams focused on endpoint monitoring and insider threat prevention | Cloud / Endpoint | Deep endpoint visibility and control of user activity | Limited visibility into broader data environments and permissions |
Top 10 Data Security Platforms
Below is a curated list of the top data security platforms that help organizations discover sensitive data, reduce exposure, and protect information across on-premises and cloud environments.
1. Lepide Data Security Platform
Lepide Data Security Platform is best suited for organizations that need clear, continuous visibility into sensitive data and access risk without complex tuning or heavy operational overhead.
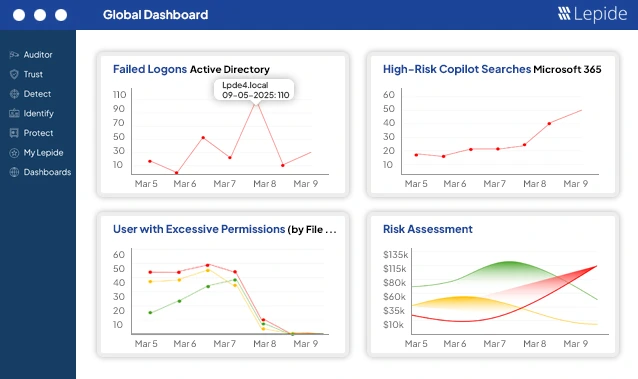
Lepide is designed to answer three questions quickly: Where is sensitive data? Who can access it? What risky changes are happening right now? The platform continuously scans file servers, Active Directory, and Microsoft 365 to identify sensitive data and monitor access behavior. Instead of raw logs, it provides clear alerts and timelines that help security teams investigate incidents and prove compliance without manual effort.
What makes Lepide stand out is its focus on clarity and speed over heavy tuning and complex telemetry. Instead of flooding teams with raw data, Lepide delivers pre-configured discovery for file servers, Active Directory, and Microsoft 365, along with context-rich alerts and investigation timelines that quickly show who accessed what and when. This allows security teams to reduce noise, respond faster, and generate audit-ready evidence without the operational overhead common in more complex DSP tools.
Lepide is especially useful in environments where file data and identity sprawl create blind spots. It focuses on clarity and speed, not complex tuning.
Key Features
- Sensitive data discovery and classification across file systems and Microsoft 365
- Continuous monitoring of access, permission changes, and user behavior
- Real-time alerts with full context for investigations
- Built-in reports for audits, compliance, and incident response
2. Microsoft Purview Information Protection
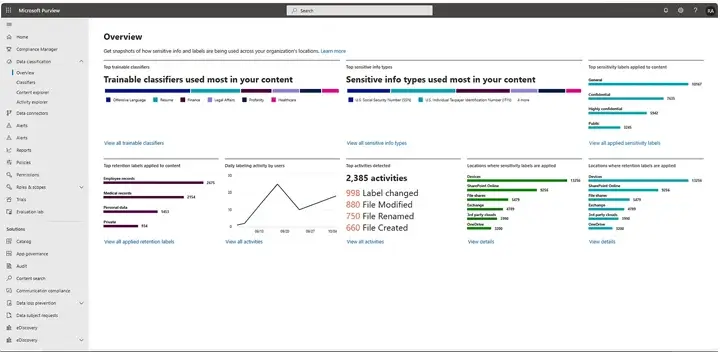
Microsoft Purview Information Protection is about controlling your data through classification and labelling. When you classify your data and assign a label, security policies are applied to the file, wherever it goes, and enforce Encryption, Access Control Restrictions or Limits to Share. Microsoft Purview is built into Microsoft 365, so users can easily apply Protection while using familiar tools such as Word, Outlook, and SharePoint.
Microsoft Purview is best suited for businesses that primarily use Microsoft 365 for their data storage and need native control as opposed to using third party products.
Key Features
- Persistent labels that remain attached to files and emails
- Automated classification using rules and machine learning
- Built-in encryption and sharing restrictions
- Deep integration with Microsoft 365 services
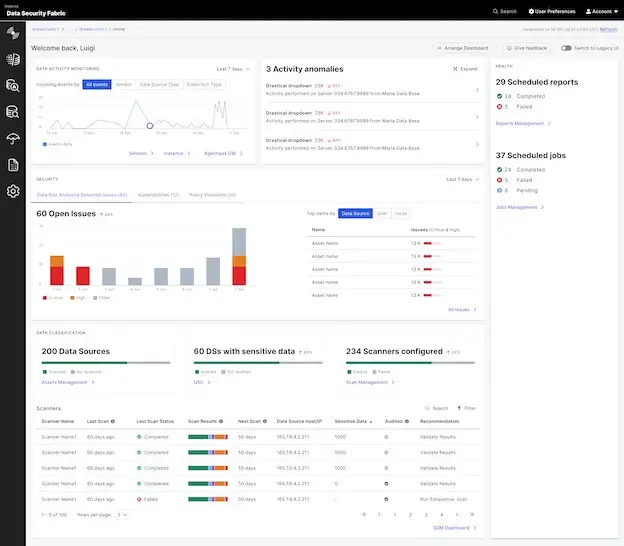
3. Varonis Data Security Platform
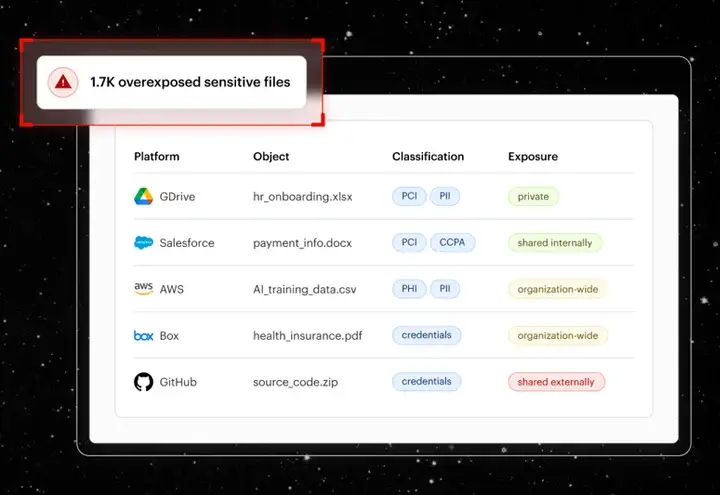
Varonis helps companies understand their data exposure and access risk by scanning their environments for any exposed sensitive data, mapping who can access that data, and calculating how much damage a compromised user account could cause to an organization. It also uses user behavioral analytics to identify anomalies of user activity that can point toward insider threats, as well as other potential indicators of ransomware and compromised credentials.
Companies large enough to have accumulated years of file sprawl and who have granted excessive permissions to too many users often choose Varonis.
Key Features
- Automated discovery and classification of sensitive data
- Access mapping and exposure analysis
- User behavior analytics to detect suspicious activity
- Guided remediation to reduce unnecessary access
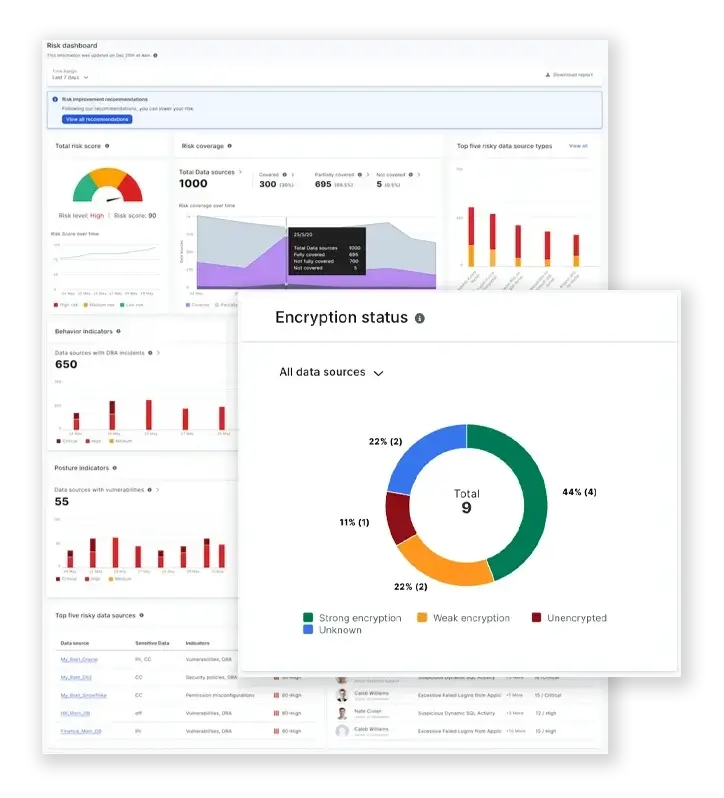
4. Thales CipherTrust Data Security Platform
CipherTrust focuses on using encryption along with the control of cryptographic keys. Organizations can utilize CipherTrust to encrypt data on multiple platforms such as databases, files, containers, and cloud-based services, while at the same time maintain the centralized control over the customer’s cryptographic keys. CipherTrust provides organizations that are mandated by law to provide evidence of data confidentiality to regulators, or to ensure the service providers cannot have access to the protected data through encryption.
CipherTrust does not focus on how to monitor user behaviours; instead it is geared towards creating approximately the same level of security at a crypto-level.
Key Features
- Centralized encryption key and policy management
- Encryption and tokenization for structured and unstructured data
- Support for hybrid and multi-cloud environments
- Detailed audit logs for regulatory compliance
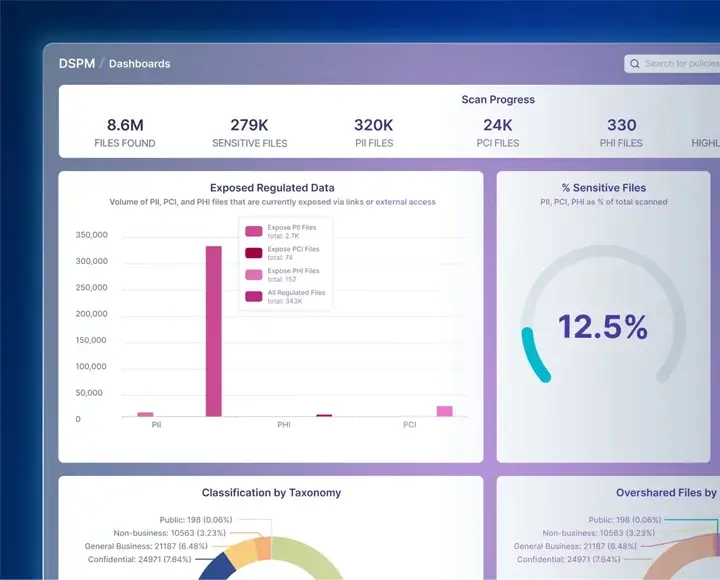
5. Imperva Data Security
Imperva Data Security offers insight and security for database storage and cloud storage platforms, as well as monitoring database activity and providing analytical tools to help identify potential misuse, weak controls, or suspicious access patterns. The system is also used to secure mission-critical databases while ensuring compliance across various hybrid environments.
Imperva is a great match for companies that store and manage high-value or regulated data on their databases.
Key Features
- Discovery and classification across databases and cloud stores
- Activity monitoring with risk-based analytics
- Centralized policy enforcement
- Data masking for non-production environments
6. Velotix
Velotix focuses on governing access to data rather than locking it down completely. It discovers data across platforms, maps relationships, and automates access approvals so teams can use data safely. The platform is designed for modern analytics-driven organizations where fast access must coexist with security and accountability.
Velotix is particularly relevant for data teams working with cloud warehouses and analytics platforms.
Key Features
- AI-driven discovery and data cataloging
- Visual mapping of data lineage and access paths
- Automated access approvals and enforcement
- Integrations with modern data platforms
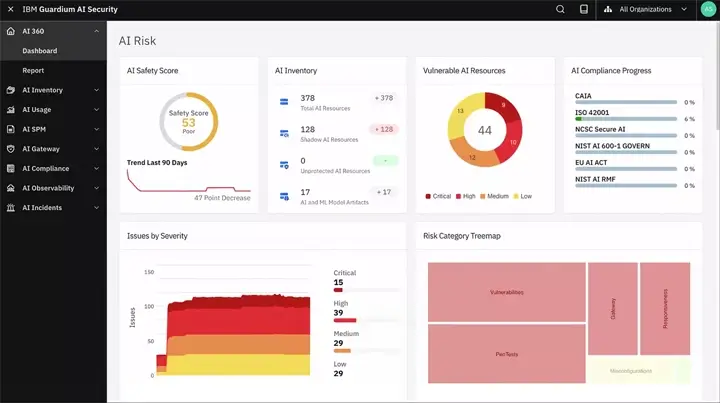
7. IBM Guardium
IBM Guardium is an enterprise-grade data security platform that specializes in monitoring, detecting, and integrating threats and security operations into an organization’s operations. Guardium is used throughout multiple industries, but its primary focus is on regulated industries that need detailed audit reporting and compliance enforcement capabilities.
While Guardium has a lot of features and strengths, it may not provide an organization with enough tools or capabilities to manage security effectively if they have a less mature security team.
Key Features
- Continuous discovery and classification of data
- Real-time monitoring of database activity
- Policy-driven alerts and automated responses
- Integration with SIEM and incident response tools
8. Forcepoint Data Loss Prevention
Forcepoint DLP protects sensitive data as it moves across endpoints, networks, and cloud applications. It combines traditional DLP controls with behavior analytics to reduce noise and improve incident prioritization. Organizations can choose between cloud-based or on-prem deployments.
Forcepoint works well for organizations focused on preventing accidental or intentional data leakage.
Key Features
- Endpoint, network, and cloud DLP coverage
- Pre-built classifiers and policy templates
- Risk-based incident prioritization
- Flexible deployment options
9. Symantec Data Loss Prevention
Symantec DLP is one of the leading enterprise DLP solutions. The solution provides monitoring and control over sensitive information across email, endpoints, networks and cloud. The product also has strong scalability and customizable policies to meet the unique requirements of large enterprises that are more complex.
While, like many DLP solutions, Symantec DLP needs to be tuned to achieve maximum effectiveness, it is an effective DLP solution when deployed in a large scale environment.
Key Features
- Multi-channel data discovery and protection
- Centralized policy and incident management
- Scalable architecture for large organizations
- Detailed compliance and investigation reports
10. Fortra Digital Guardian
Digital Guardian focuses on endpoint visibility and insider risk prevention. Its agents monitor detailed user activity on devices and allow organizations to block, alert, or monitor actions based on risk. This makes it effective for stopping data theft before files ever leave the endpoint.
Digital Guardian is often chosen when insider threats are a primary concern.
Key Features
- Deep endpoint monitoring and control
- Network and cloud DLP integration
- Flexible response actions based on risk
- Managed service options for faster deployment

Conclusion
For most organizations, the right choice depends on whether the priority is visibility, enforcement, or encryption. Platforms like Lepide are often preferred where teams need clear, ongoing insight into sensitive data and access risk, while other solutions may be better suited for highly specialized use cases such as DLP enforcement or cryptographic protection.
Frequently Asked Questions
In hybrid environments, the main challenge is maintaining consistent visibility across on-prem systems and cloud platforms. Tools that unify data discovery, access monitoring, and permissions visibility across both environments are typically preferred. Platforms like Lepide are often chosen in these scenarios because they provide a single view of sensitive data and access risk across file servers, Active Directory, and Microsoft 365.
Mid-sized organizations typically need strong visibility into sensitive data and access risk without the overhead of complex deployment or heavy tuning. Platforms that provide pre-configured discovery, monitoring, and reporting are often preferred. Tools like Lepide are commonly used in these environments because they balance depth of insight with ease of use and fast time to value, while enterprise platforms are often designed for more complex, large-scale deployments.
This depends on whether your priority is simplicity or specialized control. A unified data security platform provides a single view of sensitive data, access, and risk, which reduces operational complexity and improves visibility. Separate tools such as DLP or encryption platforms can offer deeper control in specific areas, but often require more integration and management effort.
Most organizations use a combination of both, starting with a platform that provides visibility into data and access risk, then adding specialized controls where needed.
For organizations focused on understanding how data is being used, platforms that provide continuous monitoring of access and user activity are typically preferred. This includes visibility into who accessed what, when, and whether that access was appropriate. Tools like Lepide are often used in these scenarios because they combine access monitoring with permissions visibility and contextual alerts, making investigations faster and more actionable.
Protecting sensitive enterprise data typically requires a combination of visibility, control, and enforcement. Organizations usually start by identifying where sensitive data exists and who has access to it, then apply controls such as DLP or encryption where necessary. Platforms that provide clear insight into data exposure and access risk are often the foundation of this approach, as they help teams prioritize where protection is most needed.



