The Lepide File Server auditing software enables you to audit when files and folders are created, accessed, modified, moved, renamed, copied or deleted. We also help organizations track and compare permissions across their file servers. Our File auditing software addresses the challenges of the rise of the insider-threat and the data reporting requirements associated with common regulatory compliance mandates. We give IT teams the power to see more, faster.
Audit, report, and alert on any changes that puts data at risk, including changes to files, folders, and permissions. Get answers to the critical who, what, when and where audit questions.
Get information on file and folder access activities across your Windows File Servers so that you can better control data access.
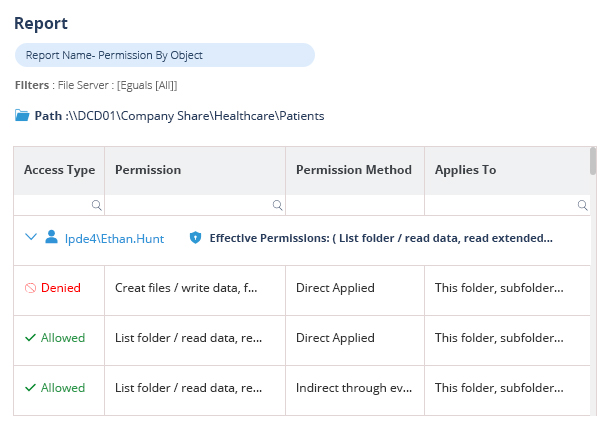
See who has access to which data, compare current and historic permissions. Spot data that is overexposed through excessive permissions.
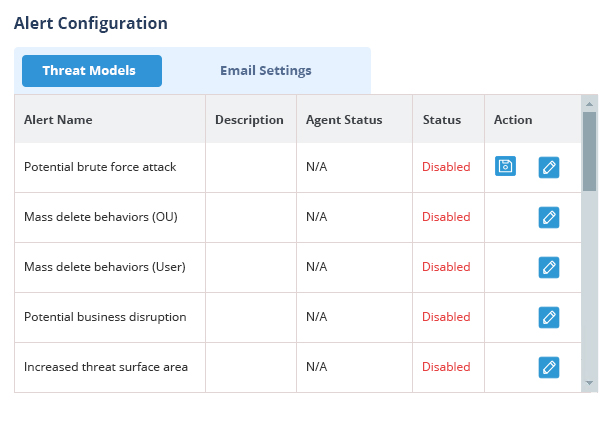
Generate automated actions off the back of real-time alerts. Respond quickly to threats like ransomware with our pre-defined threat models and prevent suspicious user behavior with threshold-based alerts.
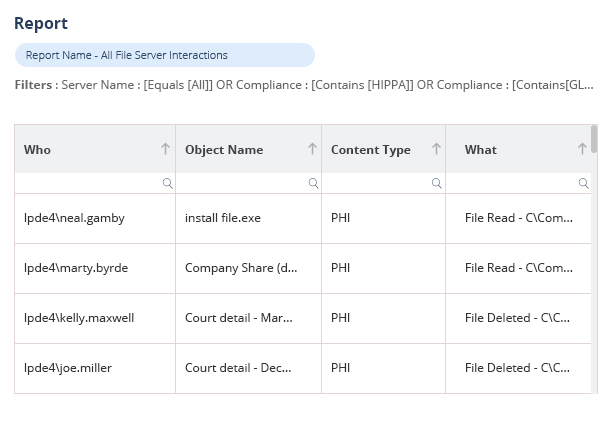
Simplify compliance reporting with pre-defined templates and mapping for GDPR, CCPA, HIPAA, FISMA, NIST, SOX, and more. Refer to our compliance datasheets for more information.
Unlike other data security platforms, Lepide can monitor when your users are copying your sensitive files to help you maintain the security and integrity of your most sensitive data.
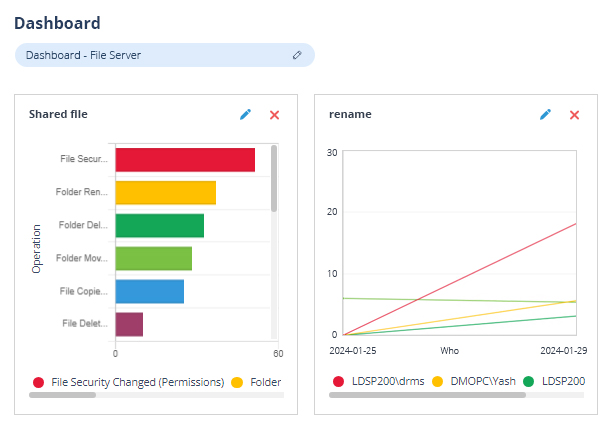
Track changes to your shared files and folders with granular who, what, when and where information.
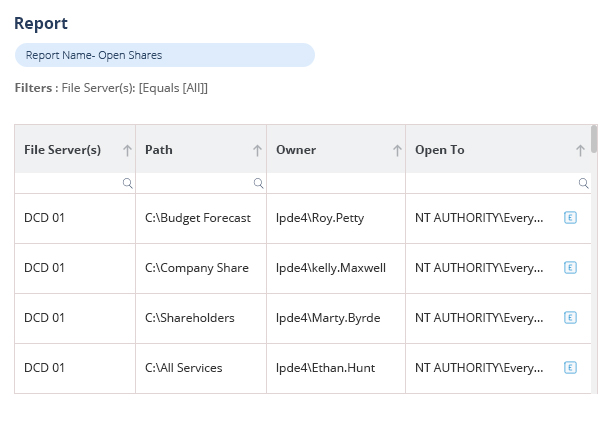
Identify potential areas of risk in your file servers, including data open to everyone through open shares, stale data, users with excessive permissions, and more.
In conjunction with Lepide Identify, automatically scan and classify sensitive or regulated data at the point of creation to add more context to your auditing reports.
Monitor what your users are doing with your sensitive data and automatically spot anomalies in user behavior that might indicate insider threats or compromised user accounts.
Take a virtual tour of the Lepide Data Security Platform in our web-based demo. See how Lepide aligns with your use case, whether it be ransomware, Active Directory security, Microsoft 365 security, data protection, data access governance or more.
Launch in-browser demo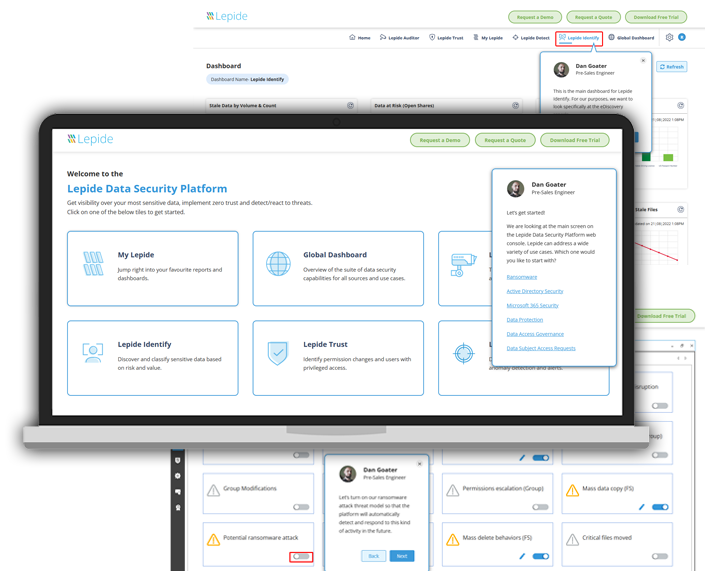
Leverage the Lepide File Server auditing tool to address critical business problems that require urgent attention. Reduce your threat surface area, better govern access to your sensitive data, spot insider threats, ransomware, and other security threats, and achieve compliance with our complete file server auditing solution.
Our file server auditing tool enables you to identify where your areas of risk are, including stale data and data open to all users through open shares. Our file sever auditing solution also analyses the data usage patterns of your users and suggests which of your users have excecssive permissions to data. Use Lepide intelligence to reduce your threat surface area by removing these areas of risk.
Maintaining a policy of least privilege is difficult when users are joining, moving, and leaving all the time. How do you know which of your users still require privileged access? With file sever auditing software from Lepide, you can identify users that have excessive permissions based on how they are using the data. You can also spot changes to permissions in real time so that you can speed up investigations and prevent permissions sprawl.
Our File Server Auditing software speeds up incident response by automatically detecting and responding to threats or suspicious user behavior. Simply activate any of our predefined threat models/ sequences (or create your own) to detect ransomware, privilege abuse, brute force attacks, and more. Predefined or custom scripts can be executed automatically to disable a user account, delete a user account, revoke the permission granted to a user, shut down a computer, and more.
The Lepide file server auditing software addresses the ever-increasing demand to prove to auditors that adequate steps are being taken to ensure data is being responsibly monitored. It provides a wide range of detailed reports that directly map to the common requirements of compliance standards ; such as PCI, SOX, HIPAA, GLBA, FISMA, CCPA and GDPR.
Our dynamic dashboards enable you to easily track changes occurring across the whole of your File Server environment. Having all this information centralized should help you not only understand the causes of a single change, but help you spot overall anomalies in events. The performance of your File Server is also tracked and reported on to help you decrease downtime. The LiveFeed shows you all File Server changes made as they are happening so that you can react to them quicker.
Our File Server auditing software helps organizations overcome the limitations of native auditing, by aggregating event log data into “single-pane” reports. Get all the information you end, including “who, what, when and where” all in one report. Below is a non-exhaustive list of what our File Server auditing tool can do.

We use Lepide for the security of our Azure and On-prem environment, its real time alert system is awesome!

Lepide is straightforward to use and effective right off the bat. Plus, the level of patience, attentiveness and technical knowhow is far beyond most support and sales teams I’ve seen before.

We chose Lepide as they were able to offer us threat detection and response, and a way of separating out reporting duties to a web console – all from one platform.

Lepide is a perfect fit for our IT Security and Compliance requirements. It helps us cut out a lot of wasted time and money and now we know we can be compliant with industry standards.
